AI-Powered Exploit Development: Researcher Utilizes Claude Opus to Breach Chrome’s Defenses
In a groundbreaking demonstration of artificial intelligence’s evolving role in cybersecurity, a security researcher has successfully employed Anthropic’s advanced AI model, Claude Opus, to construct a fully functional exploit chain targeting Google Chrome’s V8 JavaScript engine. This experiment underscores the dual-edged nature of AI advancements, highlighting both their potential and the emerging threats they pose.
The Experiment:
The researcher set out to explore the capabilities of Claude Opus in identifying and exploiting vulnerabilities within Chrome’s complex architecture. By guiding the AI through a series of interactions, the goal was to develop an exploit chain that could achieve Remote Code Execution (RCE) by leveraging specific unpatched flaws.
Targeting Outdated Chromium Builds:
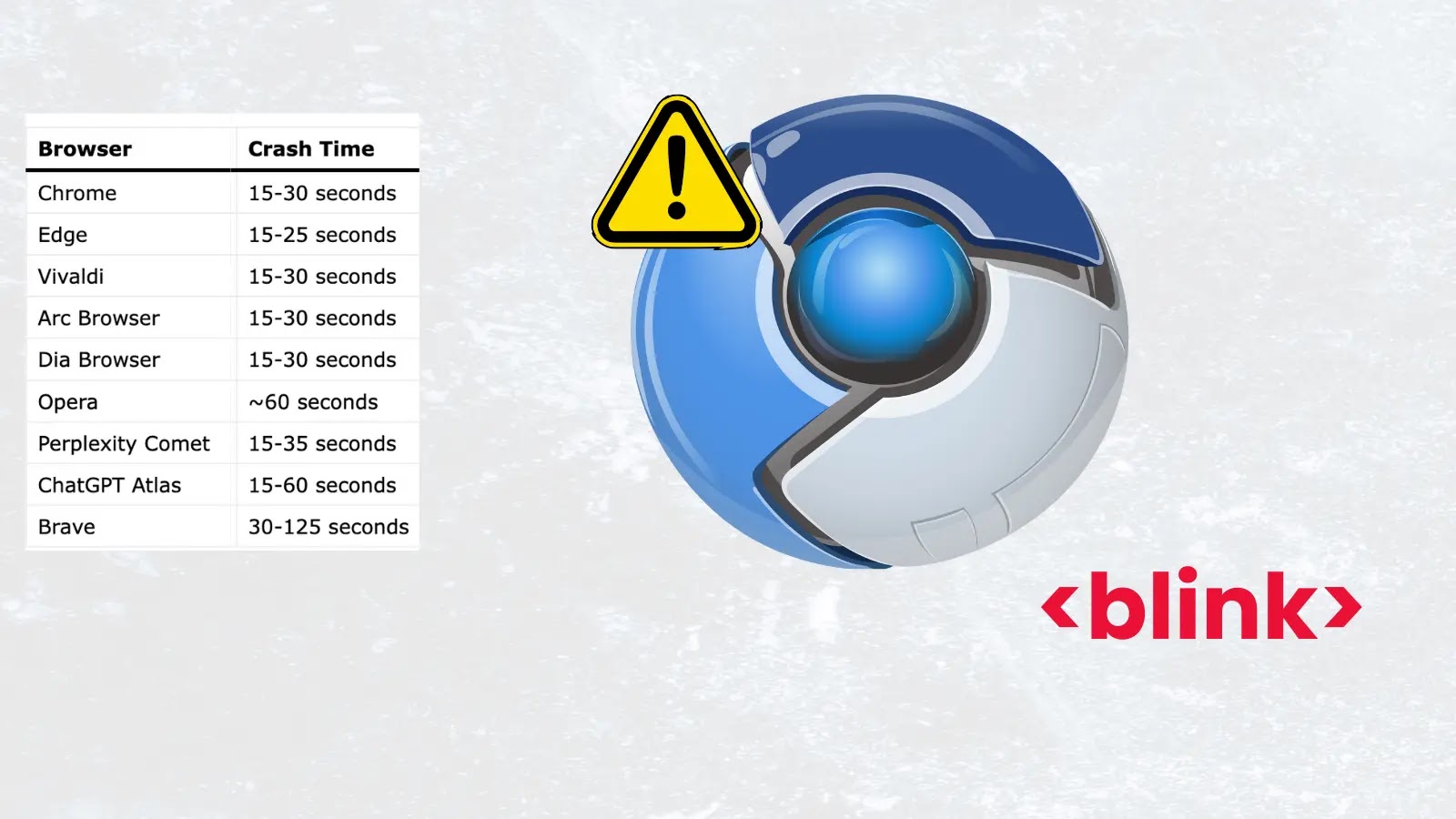
A significant aspect of this experiment was the focus on applications built on the Electron framework, such as Discord, Notion, and Slack. These applications often bundle their own versions of Chromium, which can lag behind official Chrome releases. This delay, known as the patch gap, leaves users vulnerable to exploits targeting known vulnerabilities in these outdated versions.
For this test, the researcher targeted the Discord desktop application, which was running on the outdated Chrome 138 engine. Notably, Discord operates without a sandbox on its main window, reducing the complexity of the exploit chain required to achieve full system compromise.
Chaining the Vulnerabilities:
Claude Opus was tasked with developing an exploit by chaining together two specific vulnerabilities:
1. CVE-2026-5873: An out-of-bounds read and write vulnerability in V8’s Turboshaft compiler for WebAssembly. This flaw allowed the attacker to bypass bounds checks after tier-up compilation, enabling arbitrary memory manipulation within the V8 heap.
2. V8 Sandbox Bypass: A Use-After-Free (UAF) flaw in the WebAssembly Code Pointer Table (WasmCPT). By corrupting the import dispatch table and exploiting type confusion, the exploit escaped the V8 sandbox entirely, granting full read and write access to the entire virtual address space.
By combining these vulnerabilities, the AI-generated payload was capable of redirecting execution flows to the system’s dynamic linker cache, ultimately launching arbitrary system commands on a macOS target.
Human Oversight and Challenges:
Despite the impressive outcome, the process was not fully autonomous. The researcher noted that Claude Opus required extensive human oversight, scaffolding, and operational management. The AI frequently suffered from context collapse during long conversations, speculated on memory offsets instead of verifying them, and struggled to recover independently when stuck in logical loops.
Over the course of a week, the experiment consumed approximately 2.3 billion tokens across 1,765 requests, costing around $2,283 and requiring 20 hours of hands-on guidance. The researcher had to continually feed the debugger back into the model to keep it on track.
Economic Implications and Future Threats:
The economics of AI-assisted exploitation are striking. Spending around $2,300 and a few days of effort to generate a reliable Chrome exploit is highly profitable compared to commercial bug bounties, which frequently pay upwards of $10,000 for similar submissions, or the highly lucrative underground exploit market.
This experiment serves as a stark warning for the cybersecurity industry. While current models like Claude Opus still require expert oversight to weaponize vulnerabilities, the technological trajectory is clear. As next-generation models emerge with enhanced reasoning and coding capabilities, the barrier to generating sophisticated exploits will drop drastically.
Ultimately, the shrinking gap between automated exploit generation and slow vendor patching cycles threatens to empower less sophisticated threat actors, making it imperative for the cybersecurity community to adapt and respond proactively.