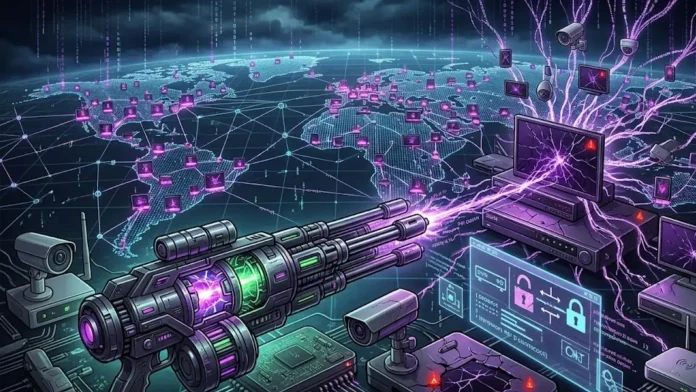
Emergence of Nexcorium: A New Mirai Variant Exploiting TBK DVR Vulnerabilities
A new variant of the infamous Mirai botnet, named Nexcorium, has been identified actively targeting internet-connected video recording devices. According to recent research by Fortinet’s FortiGuard Labs, cybercriminals are exploiting a known command injection vulnerability to compromise TBK DVR systems, thereby constructing a large-scale Distributed Denial-of-Service (DDoS) botnet.
The campaign specifically targets TBK DVR-4104 and DVR-4216 models by exploiting CVE-2024-3721, an OS command injection flaw. This vulnerability allows attackers to deliver a downloader script by manipulating arguments within the device system. During the exploitation phase, network traffic reveals a custom HTTP header reading X-Hacked-By: Nexus Team – Exploited By Erratic, leading FortiGuard Labs to attribute the campaign to a relatively unknown threat actor identified as the Nexus Team.
Once the downloader script executes, it fetches multi-architecture payloads supporting ARM, MIPS, and x86-64 environments, subsequently displaying a console message stating nexuscorp has taken control.
Technical Capabilities and Infection Mechanisms
Fortinet’s analysis reveals that Nexcorium shares fundamental architecture with traditional Mirai variants, utilizing XOR-encoded configurations and modular components. The technical operation relies on several core mechanisms:
– Modular Architecture: The malware deploys standard Mirai features, including a watchdog module to distinguish sub-processes, a scanner for network propagation, and an attacker module for DDoS execution.
– Legacy Exploit Integration: To maximize its infection radius, Nexcorium incorporates the older CVE-2017-17215 vulnerability, which targets Huawei router devices.
– Aggressive Brute-Forcing: The malware launches Telnet-based brute-force attacks against other networked hardware using a hardcoded list of common and default credentials.
– Self-Preservation: Nexcorium verifies its own integrity using FNV-1a hashing algorithms; if the binary is altered or unreadable, it dynamically duplicates itself under a new filename to evade detection.
To maintain long-term access to compromised systems, the malware establishes persistence through four distinct mechanisms rather than relying on a single configuration file. The botnet secures its foothold by:
– Modifying `/etc/inittab` to ensure automatic process restarts if the malware is terminated.
– Updating `/etc/rc.local` to guarantee execution during the device’s system startup sequence.
– Creating a dedicated systemd service named `persist.service` for persistent background operation.
– Planting scheduled tasks via crontab for reliable post-reboot execution.
Following this extensive setup, Fortinet notes that Nexcorium deletes its original binary from the execution path to thwart security analysts.
The primary objective of the Nexus Team campaign is launching devastating DDoS attacks. Based on FortiGuard Labs’ decryption of the malware’s configuration table, Nexcorium communicates with a centralized command-and-control (C2) server to receive attack directives. Instead of a narrow attack scope, the botnet is equipped with a versatile arsenal of flood techniques. These include standard UDP, TCP ACK, TCP SYN, SMTP, and TCP PSH floods, along with more sophisticated methods like DNS amplification and HTTP GET/POST floods.
Implications and Recommendations
The emergence of Nexcorium underscores the evolving threat landscape where cybercriminals continuously adapt and enhance malware capabilities to exploit known vulnerabilities in IoT devices. The use of TBK DVR systems as entry points highlights the critical need for robust security measures in internet-connected devices.
To mitigate the risks associated with such botnet activities, it is imperative for organizations and individuals to:
– Regularly Update Firmware: Ensure that all IoT devices, including DVRs, are running the latest firmware versions to patch known vulnerabilities.
– Change Default Credentials: Replace default usernames and passwords with strong, unique credentials to prevent unauthorized access.
– Implement Network Segmentation: Isolate IoT devices from critical network infrastructure to limit potential lateral movement by attackers.
– Monitor Network Traffic: Utilize intrusion detection systems to identify and respond to unusual network activity indicative of compromise.
By adopting these proactive measures, the potential impact of botnet infections like Nexcorium can be significantly reduced, safeguarding both individual users and organizational networks from large-scale DDoS attacks and other malicious activities.