Windows Defender Zero-Day Vulnerabilities: A Deep Dive into BlueHammer and RedSun Exploits
In early April 2026, the cybersecurity community was shaken by the disclosure of two critical zero-day vulnerabilities in Microsoft Defender, known as BlueHammer and RedSun. These exploits, publicly released by a researcher operating under the alias Nightmare-Eclipse (also known as Chaotic Eclipse), have been actively exploited in the wild, posing significant risks to Windows users worldwide.
The Emergence of BlueHammer
On April 2, 2026, Nightmare-Eclipse published the BlueHammer exploit on GitHub, following a reported dispute with Microsoft’s Security Response Center (MSRC) over the handling of vulnerability disclosures. This zero-day vulnerability, now tracked as CVE-2026-33825, exploits a time-of-check to time-of-use (TOCTOU) race condition and path confusion flaw within Windows Defender’s signature update workflow. This flaw enables a low-privileged local user to escalate their privileges to SYSTEM-level access on fully patched Windows 10 and Windows 11 systems.
The exploit leverages the interaction between Microsoft Defender’s file remediation logic, NTFS junction points, the Windows Cloud Files API, and opportunistic locks (oplocks). Notably, it does not require kernel exploits or memory corruption, making it a sophisticated yet accessible attack vector.
Introduction of RedSun and UnDefend
Shortly after the release of BlueHammer, Nightmare-Eclipse introduced two additional tools: RedSun and UnDefend.
– RedSun: This exploit also achieves SYSTEM privileges on Windows 10, Windows 11, and Windows Server 2019. Alarmingly, it remained effective even after the April Patch Tuesday updates, indicating that existing patches did not mitigate this vulnerability.
– UnDefend: This tool disrupts Defender’s update mechanism, progressively degrading its protective capabilities. By interfering with Defender’s ability to update its signatures and engine, UnDefend leaves systems vulnerable to a wide range of threats.
Active Exploitation in the Wild
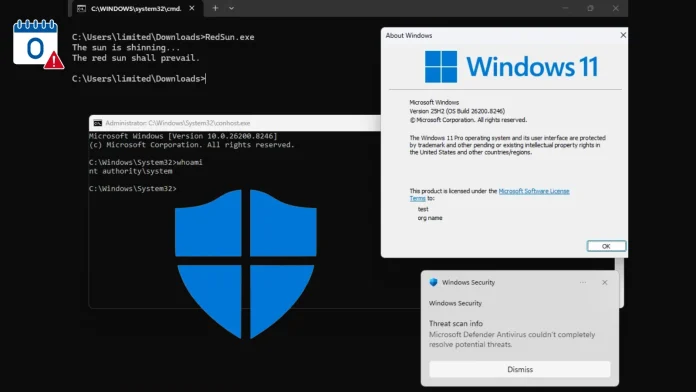
Security firm Huntress has confirmed active exploitation of all three techniques against live targets. Threat actors have been observed deploying binaries such as RedSun.exe and FunnyApp.exe in user-accessible folders like Downloads and Pictures. These files often retain the same names as those from the original proof-of-concept repositories, suggesting a direct adoption of the publicly available exploits.
In one instance, on April 10, 2026, the execution of BlueHammer was detected via:
– `C:\Users\[REDACTED]\Pictures\FunnyApp.exe`
Windows Defender identified and quarantined the file, detecting it as `Exploit:Win32/DfndrPEBluHmrBZ` with a severity classification of Severe. The threat was detected in real-time and quarantined within minutes.
Another incident on April 16, 2026, involved:
– `C:\Users\[REDACTED]\Downloads\RedSun.exe`
This execution triggered a Virus:DOS/EICAR_Test_File alert, a deliberate component of RedSun’s attack technique. The exploit uses an EICAR test file to bait Defender’s real-time engine into a detection-and-remediation cycle that can then be manipulated.
Both exploitation attempts were accompanied by manual enumeration commands consistent with hands-on-keyboard threat actor activity, including:
– `whoami /priv` — to enumerate current user privileges
– `cmdkey /list` — to identify stored credentials
– `net group` — to map Active Directory group memberships
This reconnaissance pattern strongly suggests that skilled adversaries are conducting targeted intrusions rather than opportunistic automated attacks.
Microsoft’s Response and Patch Status
Microsoft addressed CVE-2026-33825 (BlueHammer) in the April 2026 Patch Tuesday update cycle. However, as of this writing, RedSun and UnDefend remain unpatched, leaving millions of Windows systems at ongoing risk.
Recommendations for Users and Organizations
Given the severity and active exploitation of these vulnerabilities, it is imperative for users and organizations to take immediate action:
1. Apply Security Updates: Ensure that all April 2026 Windows security updates are applied promptly.
2. Monitor for Suspicious Executables: Regularly check for unsigned executables in user-writable directories such as `Pictures` and `Downloads` subfolders.
3. Alert on EICAR Test File Drops: Be vigilant for EICAR test file drops by non-administrative processes, as this may indicate exploitation attempts.
4. Hunt for Reconnaissance Commands: Monitor for commands like `whoami /priv`, `cmdkey /list`, and `net group`, which may signal pre-exploitation reconnaissance activities.
5. Educate Users: Inform users about the risks associated with downloading and executing unknown files, especially from untrusted sources.
Conclusion
The disclosure and active exploitation of the BlueHammer and RedSun vulnerabilities underscore the critical importance of timely vulnerability management and the need for robust security practices. As threat actors continue to evolve their tactics, it is essential for organizations to remain vigilant, apply patches promptly, and educate users to mitigate the risks associated with such exploits.