The Russian state-sponsored hacking group Turla has evolved its Kazuar backdoor into a modular peer-to-peer (P2P) botnet, enhancing its stealth and persistence on compromised systems. This development, reported by The Hacker News, signifies a strategic shift towards more resilient and covert cyber operations.
Turla, associated with Russia’s Federal Security Service (FSB), has a history of targeting government, diplomatic, and defense sectors across Europe and Central Asia. The group’s latest upgrade to Kazuar aligns with its objective of maintaining long-term access to systems for intelligence collection.
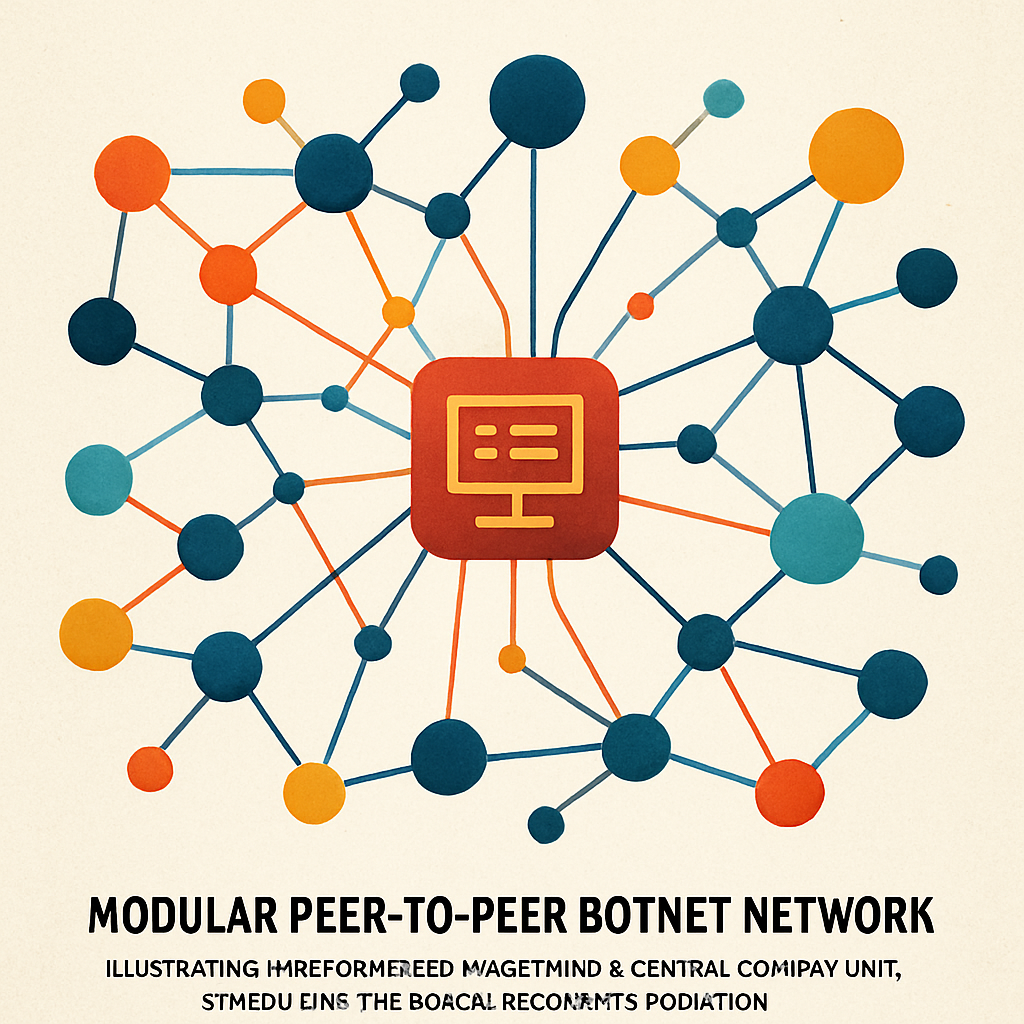
Modular Architecture of Kazuar
The revamped Kazuar now operates with a modular structure comprising three distinct components:
- Kernel Module: Serves as the central coordinator, issuing tasks to Worker modules, managing communication with the Bridge module, and performing anti-analysis checks. It also handles configuration settings related to command-and-control (C2) communication and data exfiltration.
- Bridge Module: Acts as a proxy between the Kernel module and the C2 server, facilitating communication while maintaining operational security.
- Worker Module: Responsible for logging keystrokes, monitoring Windows events, tracking tasks, and gathering system information, including file listings and Messaging Application Programming Interface (MAPI) details.
This modular design allows for flexible configuration, reduces the malware’s observable footprint, and facilitates broad tasking capabilities.
Communication and Coordination
The Kernel module employs three internal communication mechanisms—Windows Messaging, Mailslot, and named pipes—and supports three methods for contacting attacker-controlled infrastructure: Exchange Web Services, HTTP, and WebSockets. Notably, the Kernel module elects a leader based on operational metrics, which then coordinates with the Bridge module on behalf of other Kernel instances.
According to The Hacker News, this evolution of Kazuar into a modular botnet underscores Turla’s commitment to developing sophisticated tools that enhance their operational resilience and stealth. For organizations, this highlights the critical need for robust cybersecurity measures and continuous monitoring to detect and mitigate such advanced threats.
Source: The Hacker News