Pwn2Own Berlin 2026: Unveiling Critical Vulnerabilities in Microsoft Edge, Windows 11, and LiteLLM
The Pwn2Own Berlin 2026 cybersecurity competition commenced with a series of groundbreaking exploits targeting prominent software platforms, including Microsoft Edge, Windows 11, and LiteLLM. On the first day alone, security researchers uncovered 24 unique zero-day vulnerabilities, earning a collective $523,000 in rewards. These findings underscore the persistent security challenges within widely used technologies and the emerging risks associated with artificial intelligence (AI) infrastructures.
Edge Sandbox Escape
A highlight of the event was the sophisticated sandbox escape executed against Microsoft Edge by Orange Tsai of the DEVCORE Research Team. By chaining four distinct logic vulnerabilities, Tsai achieved a full system compromise, demonstrating the potential for minor flaws to escalate into significant security breaches. This exploit earned him $175,000 and 17.5 Master of Pwn points, positioning DEVCORE at the forefront of the competition. The attack serves as a stark reminder of the complexities involved in modern browser security and the necessity for continuous vigilance.
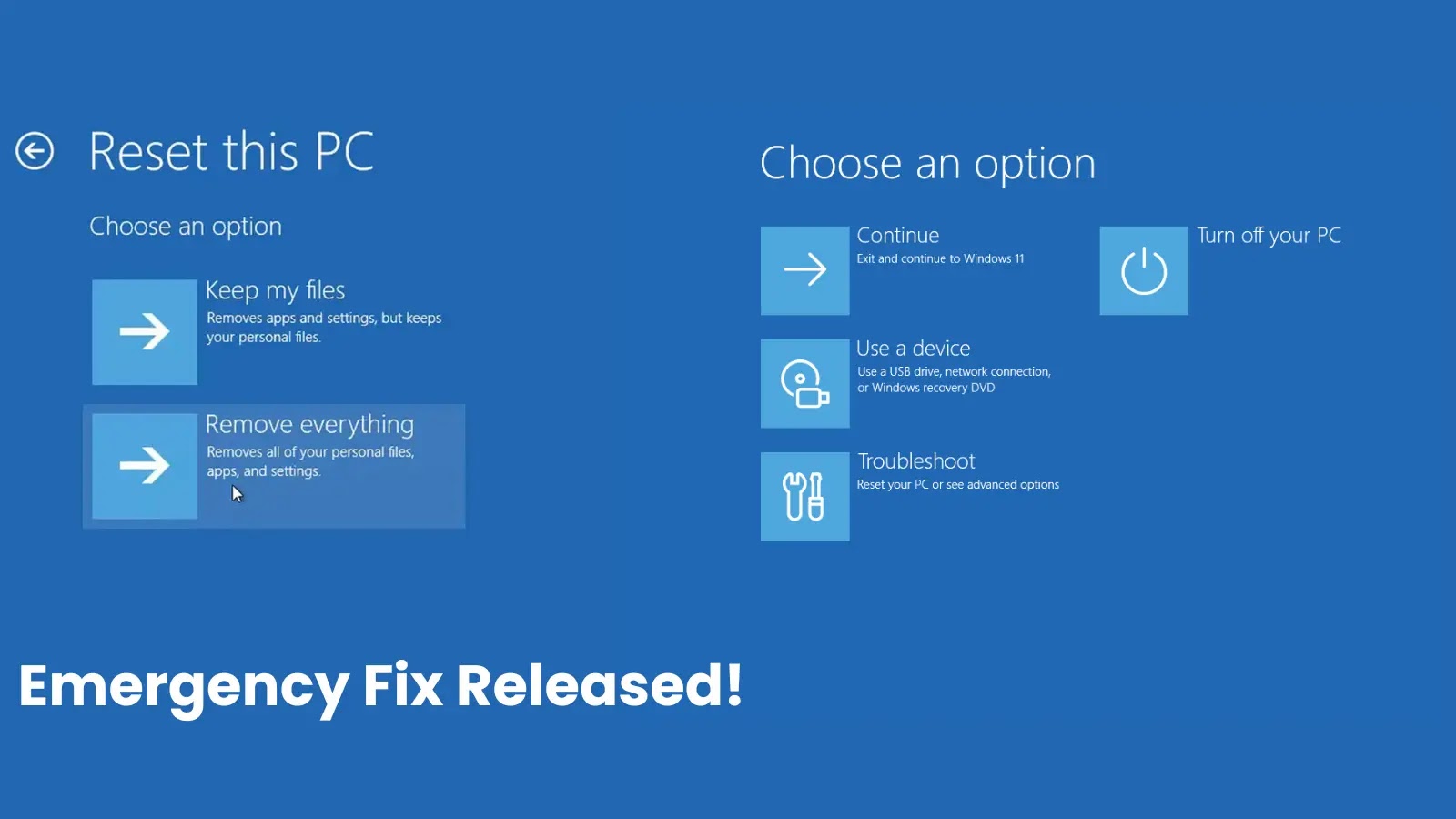
Windows 11 Privilege Escalations
Microsoft’s latest operating system, Windows 11, was also a focal point for researchers, with multiple successful privilege escalation attacks recorded. Techniques such as heap-based buffer overflows and use-after-free vulnerabilities were employed to gain elevated privileges. Notably, researchers Angelboy and TwinkleStar03 from DEVCORE exploited an improper access control flaw, further highlighting the ongoing challenges in securing mature operating systems against sophisticated attacks.
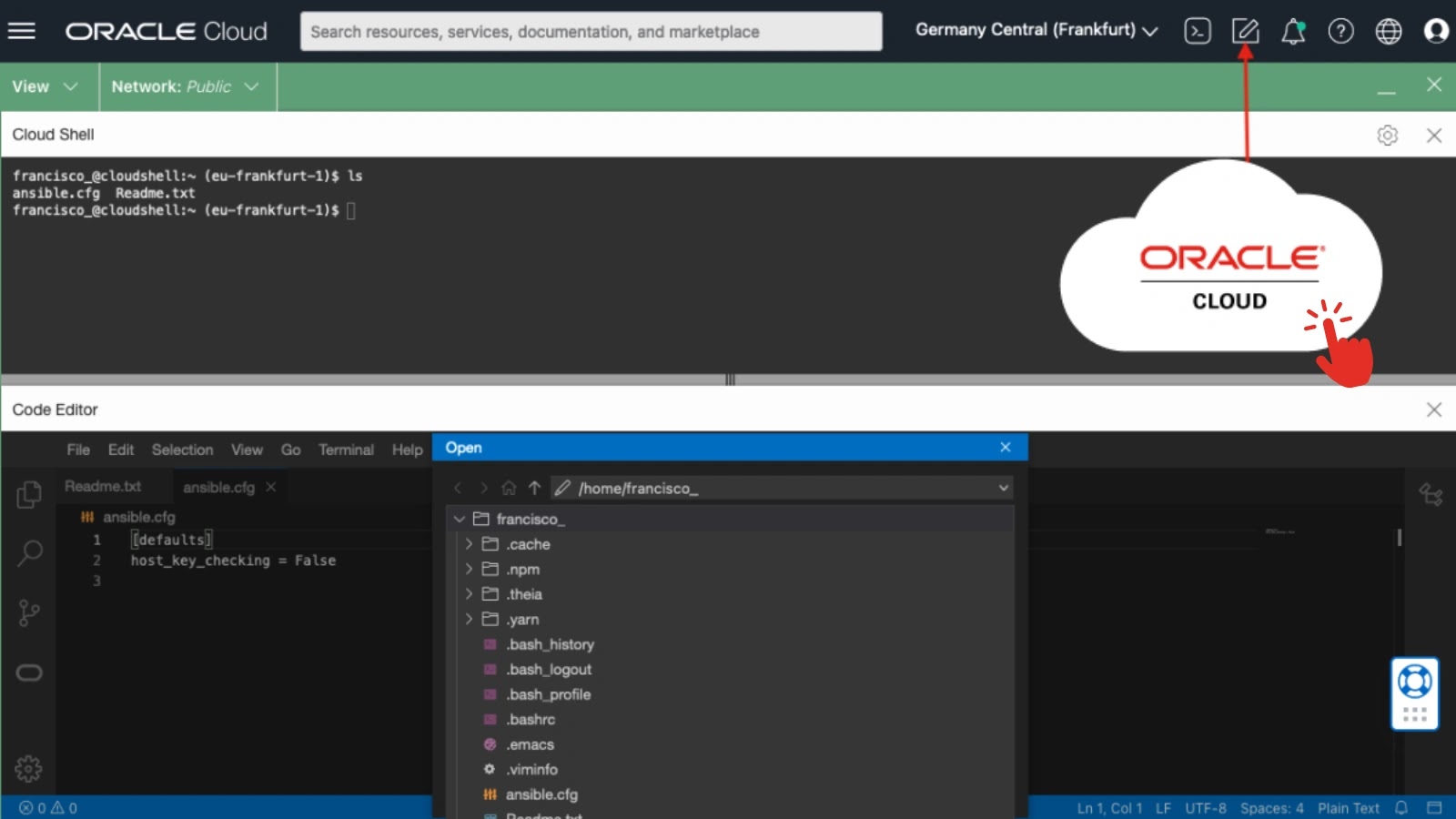
LiteLLM Exploited
The competition also shed light on vulnerabilities within AI infrastructures. Researcher k3vg3n executed a full-chain exploit against LiteLLM, combining three vulnerabilities, including Server-Side Request Forgery (SSRF) and code injection, to achieve full system takeover. This exploit, which earned $40,000, emphasizes the critical need for robust security measures in AI frameworks, particularly those handling external inputs and APIs.
AI and Developer Tools Under Pressure
Beyond LiteLLM, other AI-focused platforms faced scrutiny. OpenAI Codex was exploited using a CWE-150 flaw by Compass Security researchers, while NVIDIA’s Megatron Bridge was breached multiple times due to overly permissive allow lists and path-traversal vulnerabilities. IBM X-Force researchers also successfully exploited a single bug in the NV Container Toolkit. These incidents highlight the evolving threat landscape within AI and developer tooling ecosystems, underscoring the importance of secure design and threat resilience.
While several researchers failed to exploit targets such as OpenAI Codex and Oracle Autonomous AI Database within the allotted time, the successful exploits demonstrated during Pwn2Own Berlin 2026 provide invaluable insights into existing security gaps. The event serves as a crucial platform for identifying and addressing vulnerabilities, ultimately contributing to the development of more secure technologies.