Malicious npm Package Exploits Hugging Face for Malware Distribution and Data Theft
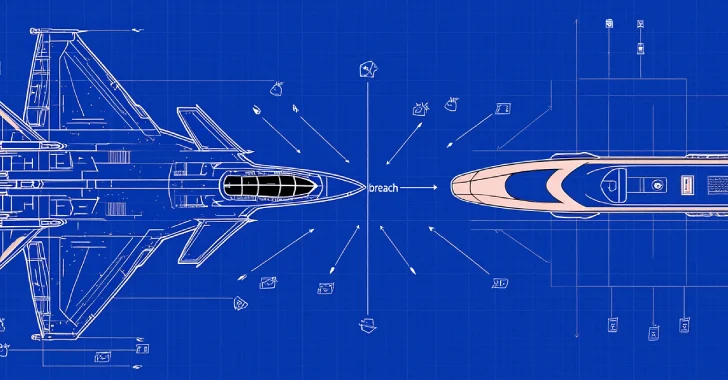
In a recent cybersecurity incident, a malicious npm package named `js-logger-pack` has been identified leveraging Hugging Face, a reputable AI model hosting platform, to disseminate malware and exfiltrate sensitive data. This attack underscores a growing trend where cybercriminals exploit trusted cloud services to conduct supply chain attacks while evading detection.
Deceptive Package Deployment
The `js-logger-pack` package masqueraded as a legitimate logging utility. Upon installation, it appeared to integrate a benign logger into the developer’s project. However, the true malicious activity commenced through a `postinstall` script that executed automatically during the installation process. This script initiated a background process, allowing the visible npm installation to complete without raising suspicion, while a concealed downloader operated in the background.
Depending on the host operating system, the downloader retrieved one of four malicious binaries from a public Hugging Face repository controlled by the attacker, identified as `Lordplay/system-releases`. These binaries targeted Windows, macOS, and Linux platforms.
Uniform Malicious Payload Across Platforms
Security researchers from JFrog analyzed the embedded JavaScript payload within each of the four Node.js Single Executable Application (SEA) binaries. Their findings revealed that all four binaries contained the same cross-platform JavaScript bundle, indicating a uniform malicious implant wrapped inside different Node.js runtime containers.
Establishing Persistence and Command Control
Once deployed, the implant established persistence using platform-specific methods:
– Windows: Utilized scheduled tasks and registry Run keys.
– macOS: Employed LaunchAgent entries.
– Linux: Implemented systemd user units.
The implant then initiated communication with a hard-coded command-and-control (C2) server at `195.201.194.107` via WebSocket. This connection granted the attacker the capability to execute arbitrary file operations, scan for credentials, log keystrokes, monitor clipboard activity, and deploy additional payloads.
Innovative Use of Hugging Face for Data Exfiltration
A particularly alarming aspect of this campaign was the utilization of Hugging Face as a data exfiltration channel. Instead of transmitting stolen data to a private server, the attacker redirected all collected information into private Hugging Face datasets, effectively outsourcing data storage to Hugging Face’s infrastructure.
When the attacker initiated an upload task via the C2 server, the implant received specific parameters, including a Hugging Face token, username, target path, and upload ID. It then compressed the targeted files into a gzip archive, created or accessed a private dataset under the attacker’s Hugging Face account, and uploaded the archive using an embedded Hugging Face hub client. Upon completion, the implant notified the Hetzner-hosted controller. Pending uploads were tracked locally and resumed upon reconnection, ensuring no data loss even if the connection was interrupted.
Operational Advantages for the Attacker
This method provided significant operational benefits to the attacker:
– Reduced Exposure: The C2 server did not store stolen content directly, minimizing its risk of detection.
– Evasion of Detection: By leveraging Hugging Face’s trusted platform, the malicious activity blended with legitimate traffic, making it harder to identify.
– Efficient Data Management: The implant’s ability to resume interrupted uploads ensured comprehensive data exfiltration without loss.
Credential Harvesting Tactics
The implant also featured a session-clearing function that terminated browser processes and erased credentials, compelling users to re-enter passwords. With the keylogger active, any credentials entered post-logout were captured and transmitted to a private dataset within minutes.
Implications and Recommendations
This incident highlights the evolving tactics of cybercriminals who exploit trusted platforms to conduct sophisticated supply chain attacks. Developers and organizations are urged to:
– Vigilantly Monitor Dependencies: Regularly audit and monitor third-party packages for unusual behavior or unauthorized updates.
– Implement Robust Security Measures: Utilize security tools capable of detecting anomalous activities during package installation and execution.
– Educate Development Teams: Provide training on recognizing and mitigating supply chain attacks to enhance overall security posture.
By adopting these practices, organizations can better defend against the increasing threat of supply chain attacks that exploit trusted platforms for malicious purposes.