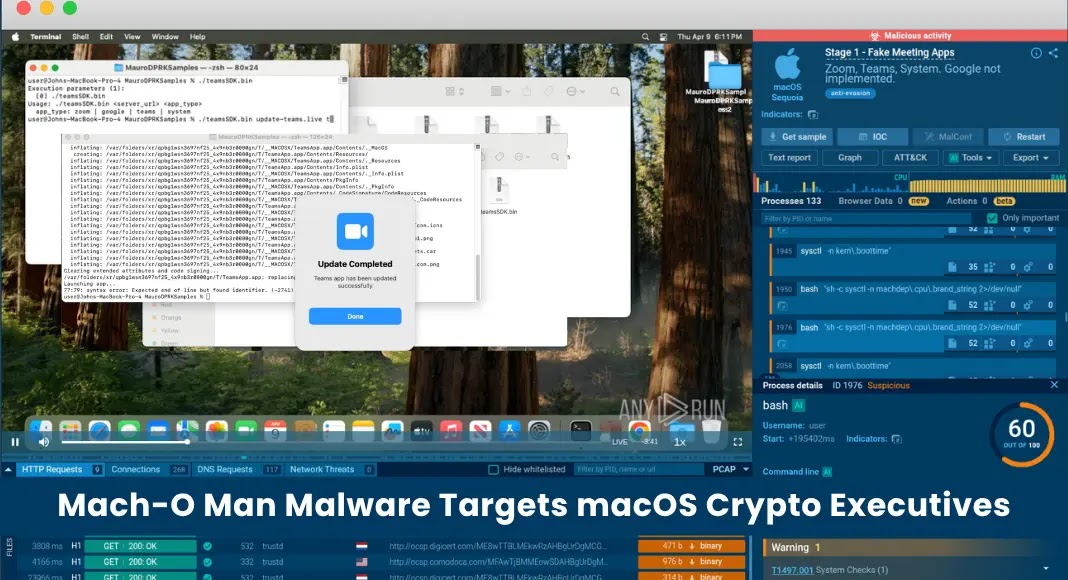
Lazarus Group’s ‘Mach-O Man’ Malware Targets macOS Users in Crypto and Fintech Sectors
The North Korean state-sponsored hacking collective, Lazarus Group, has unveiled a sophisticated macOS malware kit named Mach-O Man. This modular malware employs a four-stage attack chain specifically designed to infiltrate systems of fintech executives, cryptocurrency developers, and high-value enterprise users. The attack initiates through deceptive meeting invitations and advanced social engineering tactics.
Understanding the Mach-O Man Malware
Mach-O Man is a Go-compiled malware suite, consisting of native Mach-O binaries. This design ensures compatibility with both Intel and Apple Silicon Macs, highlighting the malware’s adaptability across different macOS architectures. The malware’s development and deployment have been analyzed by cybersecurity expert Mauro Eldritch in collaboration with the interactive sandbox platform ANY.RUN.
The Attack Sequence
The infection process begins with a social engineering technique known as ClickFix. Targeted individuals, often leaders in Web3, fintech, or cryptocurrency sectors, receive urgent messages via platforms like Telegram. These messages appear to come from trusted contacts and contain what seems to be legitimate invitations to virtual meetings on platforms such as Zoom, Microsoft Teams, or Google Meet.
Upon clicking the provided link, victims are redirected to a counterfeit collaboration platform (e.g., `update-teams[.]live` or `livemicrosft[.]com`). The site displays a simulated connection error, instructing the user to execute a terminal command to resolve the issue. This command discreetly deploys the initial stage of the malware, `teamsSDK.bin`.
Detailed Breakdown of the Four-Stage Attack Chain
1. Stage 1 – The Stager (`teamsSDK.bin`): This component downloads a fake macOS application bundle that impersonates legitimate software like Zoom, Teams, or Google Meet. It applies an ad-hoc code signature to bypass macOS execution controls and prompts the user for their password multiple times, simulating authentication failures before silently accepting the credentials.
2. Stage 2 – The Profiler (`D1YrHRTg.bin` and variants): Once executed, this module registers the infected host with the command-and-control (C2) server. It collects extensive system information, including the hostname, CPU type, boot time, operating system version, running processes, network configuration, and a comprehensive list of installed browser extensions across various browsers such as Chrome, Firefox, Safari, Brave, Opera, and Vivaldi.
3. Stage 3 – Persistence Mechanism (`minst2.bin`): To maintain a foothold on the compromised system, this module creates a directory named Antivirus Service. It places a binary disguised as `OneDrive` within this directory and installs a LaunchAgent (`com.onedrive.launcher.plist`). This setup ensures that the malware re-executes upon each user login, providing persistent access to the system.
4. Stage 4 – The Stealer (`macrasv2`): In the final stage, the malware harvests sensitive information, including browser credentials, session cookies, data stored in SQLite databases, and entries from the macOS Keychain. The collected data is then compressed into a file named `user_ext.zip` and exfiltrated using the Telegram Bot API, a method that blends malicious traffic with normal network activity, making detection more challenging.
Attribution to Lazarus Group
The Mach-O Man malware kit is attributed to the Chollima division of the Lazarus Group. This development signifies a notable escalation in the group’s focus on Apple ecosystems, platforms traditionally considered more secure but increasingly targeted by state-sponsored threat actors.
Since 2017, Lazarus has been implicated in the theft of approximately $6.7 billion in cryptocurrency assets. Recent analyses have linked over $500 million in exploits to the group’s activities, underscoring their persistent and evolving threat to the financial technology sector.
Implications for macOS Security
The emergence of Mach-O Man highlights a growing trend of sophisticated malware targeting macOS platforms. Historically perceived as more secure, macOS systems are now increasingly in the crosshairs of advanced persistent threats (APTs) like Lazarus. This shift necessitates heightened vigilance and proactive security measures among macOS users, especially those in high-risk sectors such as fintech and cryptocurrency.
Recommendations for Users
To mitigate the risk of infection by Mach-O Man and similar threats, users are advised to:
– Exercise Caution with Unsolicited Communications: Be wary of unexpected messages, especially those urging immediate action or containing links to unfamiliar websites.
– Verify Meeting Invitations: Confirm the authenticity of virtual meeting invitations through direct communication with the purported sender, using known and trusted contact methods.
– Avoid Executing Unverified Terminal Commands: Refrain from running terminal commands provided by untrusted sources, as they can be used to deploy malware.
– Implement Robust Security Measures: Utilize reputable security software, keep systems and applications updated, and regularly review system logs for unusual activity.
– Educate and Train Staff: Provide training on recognizing phishing attempts and social engineering tactics to reduce the likelihood of successful attacks.
Conclusion
The Mach-O Man malware campaign orchestrated by the Lazarus Group represents a significant advancement in the targeting of macOS users within the cryptocurrency and fintech industries. By employing sophisticated social engineering techniques and a modular attack chain, the group demonstrates a high level of adaptability and persistence. It is imperative for individuals and organizations in these sectors to remain vigilant, adopt comprehensive security practices, and stay informed about emerging threats to effectively safeguard their digital assets and sensitive information.