Critical Linux Kernel Vulnerability ‘Copy Fail’ Grants Root Access Across Major Distributions
A significant zero-day vulnerability, known as Copy Fail and designated as CVE-2026-31431, has been identified in the Linux kernel. This flaw allows unprivileged local users to escalate their privileges to root on nearly all major Linux distributions released since 2017.
Discovery and Exploitation
The vulnerability was uncovered by researcher Taeyang Lee from Theori. The Xint Code Research Team further developed a comprehensive exploit chain using AI-assisted analysis. Unlike previous vulnerabilities such as Dirty Cow (CVE-2016-5195) and Dirty Pipe (CVE-2022-0847), Copy Fail does not rely on race conditions, specific kernel version offsets, recompilation, or compiled payloads.
Technical Details
Copy Fail is a straightforward logic flaw located in the Linux kernel’s `authencesn` cryptographic template. It is accessible through the AF_ALG socket interface combined with the `splice()` system call. A 732-byte Python script, utilizing only standard library modules, can deterministically achieve root access across various distributions and architectures.
The exploit manipulates the kernel’s page cache—the in-memory representation of files—by initiating a controlled 4-byte write into a page cache page of any file readable by the attacker. Since the kernel does not mark the corrupted page as dirty for writeback, the on-disk file remains unchanged, allowing the attacker to execute the modified in-memory version of a setuid binary, such as `/usr/bin/su`, to gain root access.
Root Cause Analysis
The vulnerability stems from an optimization introduced in 2017 to `algif_aead.c` (commit `72548b093ee3`). When a user splices a file into a pipe and feeds it into an AF_ALG socket, the AEAD input scatterlist references the kernel’s physical page cache pages directly, rather than creating copies. For AEAD decryption operations, `algif_aead.c` sets `req->src = req->dst`, causing both the source and destination to point to the same scatterlist. This configuration places page cache pages into a writable destination scatterlist. The `authencesn` algorithm, used by IPsec for 64-bit Extended Sequence Number (ESN) support, then utilizes the caller’s destination buffer as scratch space to rearrange ESN bytes, writing 4 bytes at an offset of `assoclen + cryptlen` beyond the declared output boundary, directly into chained page cache pages.
Three independent code changes from 2011, 2015, and 2017 converged to create this exploitable condition, which remained undetected for nearly a decade.
Affected Systems
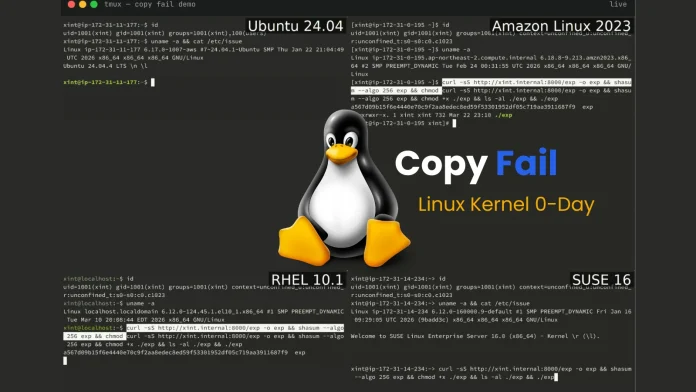
The vulnerability was introduced with kernel version 4.14 and affects all subsequent distributions up to the point of the fix. The unmodified exploit script successfully achieved root access on the following tested platforms:
– Ubuntu 24.04 LTS: Kernel version 6.17.0-1007-aws
– Amazon Linux 2023: Kernel version 6.18.8-9.213.amzn2023
– RHEL 14.3: Kernel version 6.12.0-124.45.1.el10_1
– SUSE 16: Kernel version 6.12.0-160000.9-default
Broader Implications
Beyond local privilege escalation, Copy Fail serves as a Kubernetes container escape primitive. Since the page cache is shared across all processes on a host, including across container boundaries, a compromised container can corrupt setuid binaries visible to other containers and the host kernel. This vulnerability enables a full Kubernetes node compromise, as detailed in Part 2 of the Xint Code research series.
Mitigation and Patch
The official fix (commit `a664bf3d603d`) reverts the problematic optimization in `algif_aead.c`, effectively addressing the vulnerability. Users and administrators are strongly advised to apply the patch promptly to secure their systems against potential exploits.
Conclusion
The discovery of the Copy Fail vulnerability underscores the importance of continuous vigilance and prompt patching in maintaining system security. Its widespread impact across major Linux distributions highlights the need for collaborative efforts within the open-source community to identify and address such critical flaws.