Critical iTerm2 Vulnerability Allows Remote Code Execution via Malicious Text
A significant security flaw has been identified in iTerm2, a popular terminal emulator for macOS, which could allow attackers to execute arbitrary code on a user’s system by simply displaying specially crafted text. This vulnerability exploits iTerm2’s SSH integration feature, turning seemingly harmless text output into a potential attack vector.
Understanding the Vulnerability
iTerm2 enhances user experience by integrating SSH capabilities directly into the terminal. This integration involves deploying a helper script, known as the conductor, on remote machines. The conductor facilitates tasks such as identifying the login shell, changing directories, and uploading files. Communication between iTerm2 and the conductor occurs over standard terminal input/output channels via the pseudoterminal (PTY), eliminating the need for separate network services.
The core issue arises from iTerm2’s acceptance of SSH conductor protocol messages from any terminal output, regardless of its origin. This means that untrusted terminal output can impersonate the conductor by embedding specific terminal escape sequences:
– DCS 2000p: Used to forge a hook into the SSH conductor.
– OSC 135: Employed to send fake replies and messages back to iTerm2.
An attacker can embed these sequences into a text file, server response, or even a Message of the Day (MOTD). When such a file is displayed in iTerm2, the terminal processes these sequences, initiating what it believes to be a legitimate SSH integration exchange. For instance, executing a command like `cat readme.txt` on a malicious file would print the forged sequences to the screen, deceiving iTerm2 into initiating the SSH integration process.
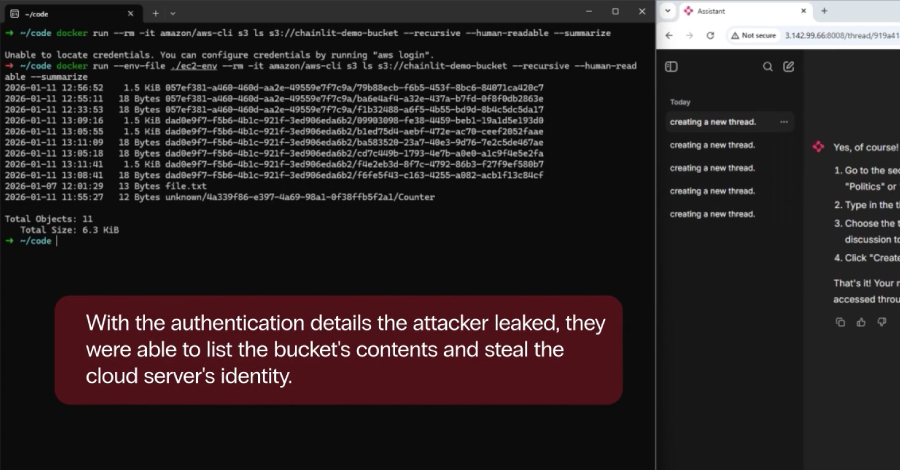
Exploitation Mechanism
Once iTerm2 accepts the fake conductor hook, it proceeds with its standard workflow, sending requests to verify shell environments and Python versions. The malicious text file, acting as a counterfeit transcript, provides precise replies that guide iTerm2 down its fallback execution path.
Believing it is communicating with a remote server, iTerm2 constructs a command execution request using attacker-controlled `sshargs`, writing the commands to the PTY as base64-encoded strings. However, since there is no actual SSH connection, the local shell interprets these base64 strings as local input.
The exploit relies on formatting the `sshargs` payload so that the final base64-encoded chunk translates into a valid local file path, such as `ace/c+aliFIo`. If the attacker places an executable payload at that specific relative path, the terminal interprets the base64 string as a local command and unknowingly executes the malware.
Potential Impact
This vulnerability poses a significant risk due to its low exploitation complexity and the widespread use of iTerm2 among developers and system administrators. An attacker could craft a malicious text file and distribute it via email, websites, or other means. Once a user views the file in iTerm2, the embedded escape sequences could trigger the execution of arbitrary code, potentially leading to:
– Unauthorized access to sensitive data.
– Installation of malware or backdoors.
– Complete system compromise.
Mitigation and Recommendations
The vulnerability was reported to iTerm2 on March 30, 2026, and a fix was committed the following day. However, as of April 21, 2026, the patched version has not yet reached stable releases. Users are advised to exercise extreme caution when displaying untrusted text files or connecting to unfamiliar SSH servers, as these may contain malicious terminal output designed to exploit this flaw.
To mitigate the risk:
1. Update iTerm2: Regularly check for updates and install the latest version once the patch becomes available.
2. Avoid Untrusted Content: Refrain from opening or displaying text files from unknown or untrusted sources within iTerm2.
3. Disable SSH Integration: If not essential, consider disabling the SSH integration feature in iTerm2 until the vulnerability is patched.
4. Monitor System Activity: Keep an eye on system logs and processes for any unusual activity that may indicate exploitation attempts.
Conclusion
The discovery of this vulnerability underscores the importance of vigilance when handling terminal output, especially in applications with integrated features like SSH. Users of iTerm2 should remain alert and adopt the recommended precautions to safeguard their systems against potential exploitation.