In the ever-evolving landscape of cybersecurity, recent developments have underscored the persistent threats facing organizations worldwide. This week’s ThreatsDay Bulletin highlights critical vulnerabilities and emerging challenges that demand immediate attention.
Exploited PAN-OS Remote Code Execution Vulnerability
Palo Alto Networks has released patches to address a critical buffer overflow vulnerability, identified as CVE-2026-0300, in its PAN-OS software’s User-ID Authentication Portal service. This flaw allows unauthenticated attackers to execute arbitrary code with root privileges by sending specially crafted packets. The company has observed limited exploitation of this vulnerability since at least last month, with threat actors deploying payloads like EarthWorm and ReverseSocks5.
Unauthorized Access to Anthropic’s Mythos AI Tool
Anthropic’s advanced AI model, Mythos, designed for cybersecurity applications, has reportedly been accessed by unauthorized users. A private online forum managed to gain access through a third-party vendor, raising concerns about the potential misuse of such powerful tools. Anthropic is currently investigating the breach to assess the extent of unauthorized access and potential implications. ([techcrunch.com](https://techcrunch.com/2026/04/21/unauthorized-group-has-gained-access-to-anthropics-exclusive-cyber-tool-mythos-report-claims/?utm_source=openai))
AI Tokenizer Attacks: A New Frontier in Cyber Threats
Researchers have identified a novel attack vector targeting AI tokenizers, the components responsible for breaking down text input into manageable units for processing by language models. These attacks can manipulate tokenizers to produce unintended outputs, potentially leading to data leakage or model misbehavior. As AI systems become more integrated into critical applications, securing their foundational components is paramount.
Zero-Authentication Data Leak in Defense Sector
A defense technology company with Department of Defense contracts exposed sensitive user records and military training materials through API endpoints lacking proper authorization checks. The vulnerability allowed low-privilege accounts to access data across multiple tenants, including user listings, organization records, and training metadata. The company has since addressed the issue and stated that there is no evidence of third-party exploitation.
FCC Extends Deadline for Router Security Updates
The U.S. Federal Communications Commission (FCC) has extended the deadline for owners of banned internet routers to provide security updates to U.S.-based users by two years. Initially, the FCC banned the import and sale of certain foreign-produced consumer-grade routers due to national security concerns. The extension aims to ensure the continued functionality and security of already deployed routers in the U.S.
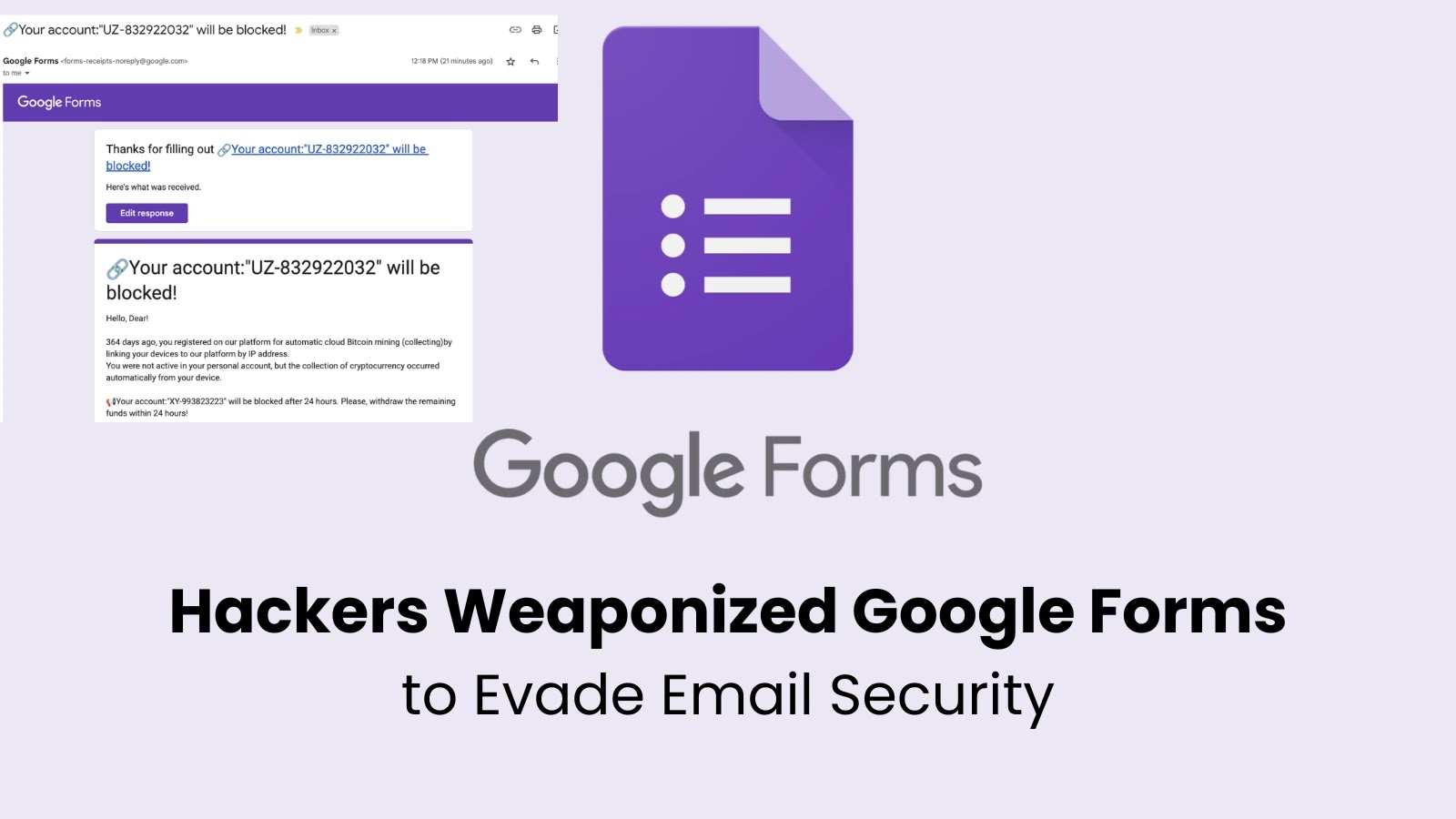
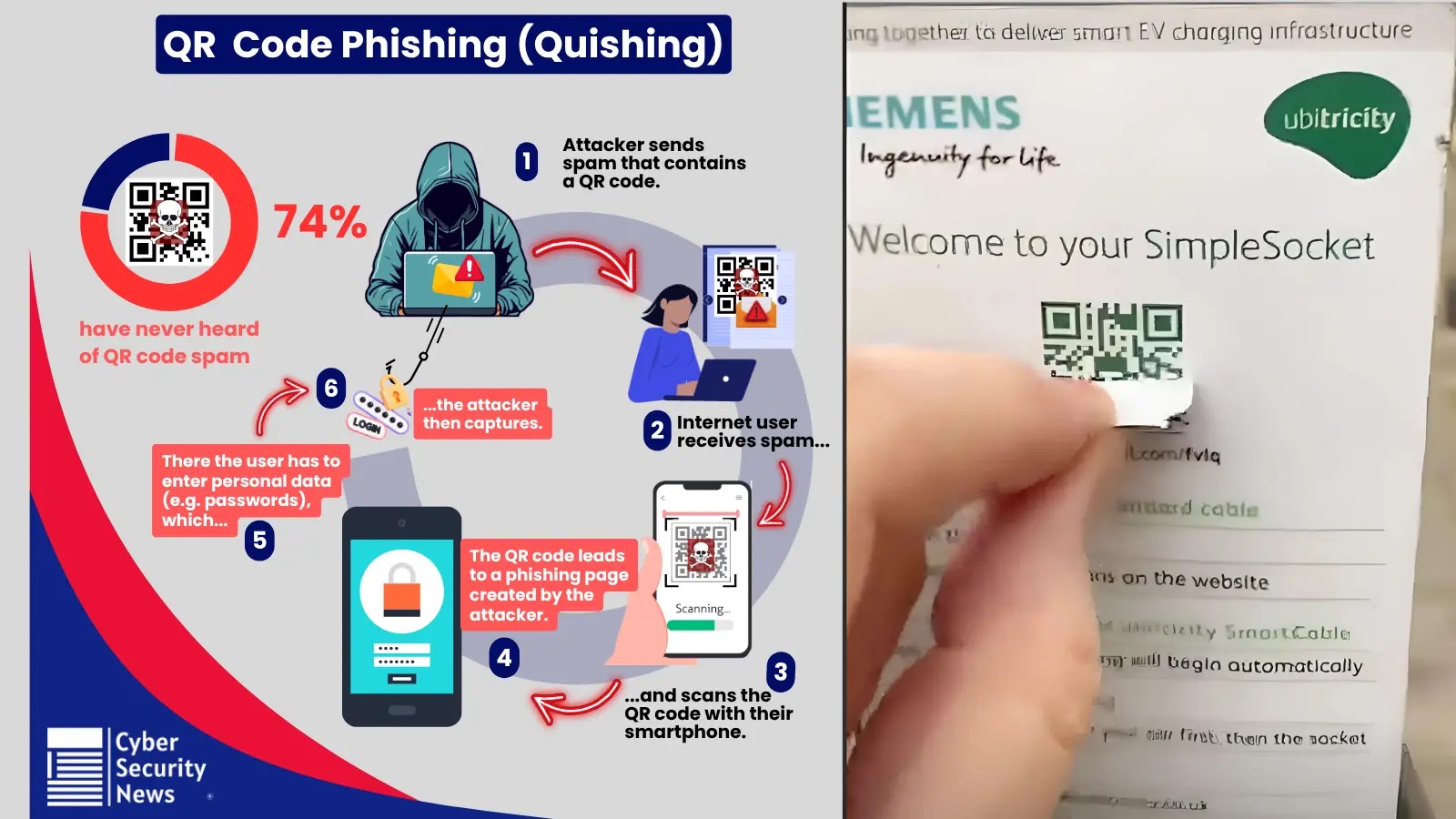
Advanced Persistent Threat (APT) Phishing Campaigns
Recent reports indicate a surge in sophisticated phishing campaigns orchestrated by Advanced Persistent Threat (APT) groups. These campaigns employ highly targeted social engineering tactics to compromise high-value targets, emphasizing the need for continuous vigilance and robust email security measures.
Emerging Threats in AI-Integrated Applications
The integration of Large Language Models (LLMs) into applications has introduced new vulnerabilities, particularly Remote Code Execution (RCE) risks. A recent study uncovered multiple RCE vulnerabilities in LLM-integrated frameworks, highlighting the necessity for comprehensive security assessments in AI application development. ([arxiv.org](https://arxiv.org/abs/2309.02926?utm_source=openai))
Conclusion
The cybersecurity landscape continues to present complex challenges, from critical software vulnerabilities to the unintended consequences of AI integration. Organizations must adopt a proactive approach, emphasizing regular security assessments, prompt patch management, and continuous monitoring to mitigate these evolving threats.