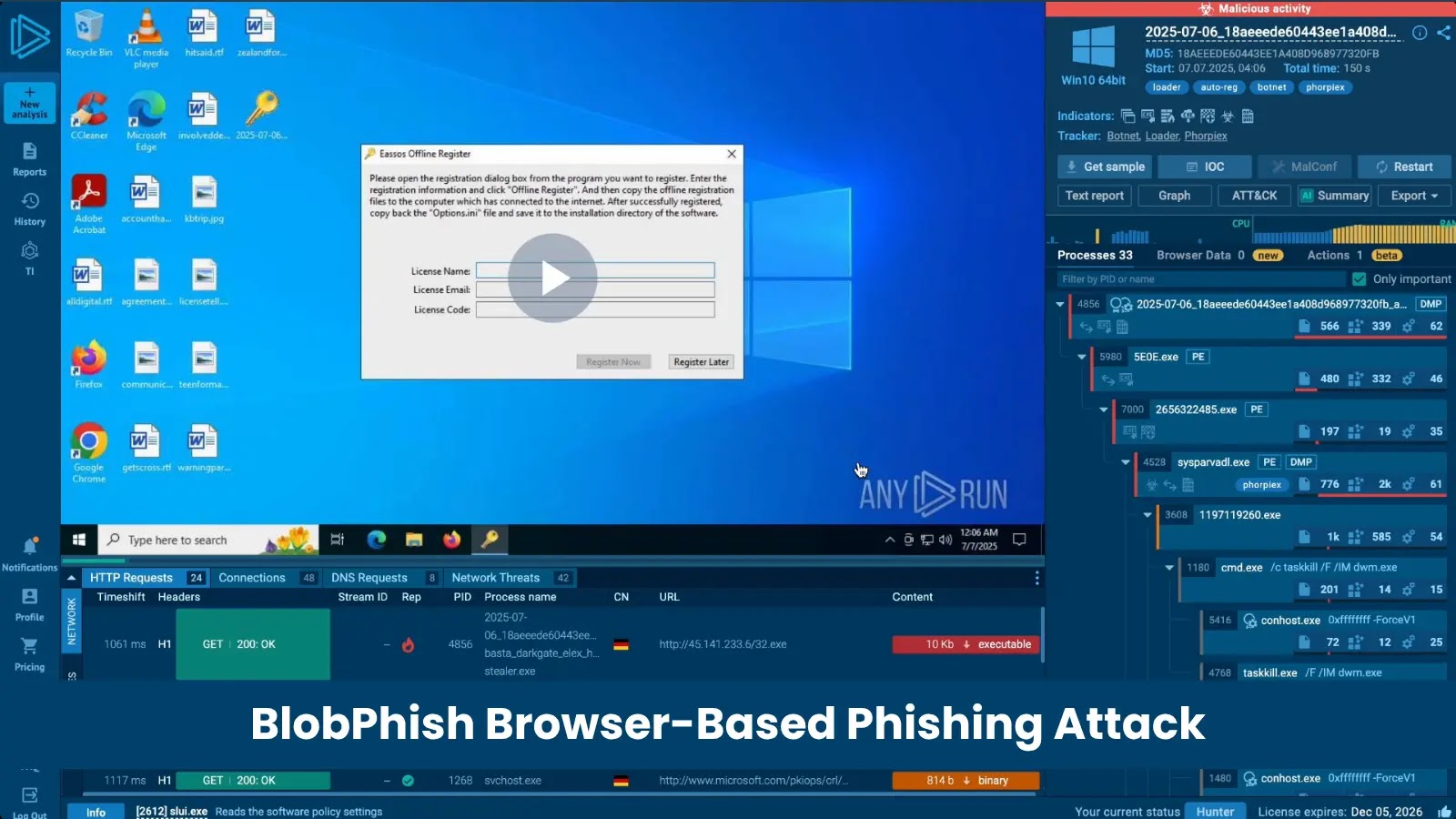
BlobPhish: The Stealthy Browser-Based Attack Targeting Microsoft 365 and Financial Institutions
In the ever-evolving landscape of cyber threats, a sophisticated phishing campaign known as BlobPhish has emerged, posing significant risks to Microsoft 365 users and major financial institutions. Active since October 2024, BlobPhish leverages browser Blob URL APIs to create in-memory phishing pages, effectively bypassing traditional security measures and leaving minimal traces for detection.
Understanding BlobPhish
Unlike conventional phishing attacks that host malicious login pages on external servers, BlobPhish generates these pages directly within the victim’s browser using JavaScript Blob objects. This method results in phishing content that resides solely in memory, eliminating the presence of files on disk or suspicious network traffic that could alert security systems.
The Attack Mechanism
The BlobPhish attack unfolds through a meticulously crafted sequence:
1. Initial Contact: Victims receive phishing emails masquerading as financial alerts, invoices, or document-sharing notifications. These emails contain links that appear to lead to legitimate services like DocSend or utilize shortened URLs. In some instances, PDF attachments with QR codes redirect users to malicious JavaScript pages.
2. Loader Activation: Clicking the link directs the victim to an attacker-controlled HTML page containing a JavaScript loader. This loader performs the following actions:
– Creates a hidden `` anchor element.
– Decodes a Base64-encoded phishing payload using the `atob()` function.
– Constructs a `Blob` object of type `text/html`.
– Generates a `blob:https://` URL via `window.URL.createObjectURL()`.
– Forces the browser to navigate to the generated Blob URL, all without visible user interaction.
3. Evidence Elimination: Immediately after navigation, the loader invokes `window.URL.revokeObjectURL()` and removes the anchor element from the Document Object Model (DOM), erasing any residual traces of its operation.
4. Credential Harvesting: The victim is presented with a convincing replica of a Microsoft 365 or financial service login page. The browser’s address bar displays a `blob:https://` URL, which may appear legitimate to unsuspecting users. A failed-login counter prompts victims to re-enter credentials multiple times, enhancing the accuracy of the harvested data. Captured credentials are then exfiltrated via HTTP POST requests to attacker-controlled endpoints, often hosted on compromised legitimate WordPress sites.
Implications and Challenges
The BlobPhish campaign represents a significant advancement in phishing tactics, effectively circumventing both network-based and file-based security defenses. By operating entirely within the browser’s memory, it leaves minimal forensic evidence, complicating detection and analysis efforts.
Security professionals must adapt to these evolving threats by implementing advanced detection mechanisms capable of identifying in-memory attacks. User education is also crucial; individuals should be trained to recognize subtle anomalies in URLs and be cautious of unsolicited emails requesting credential input.
Conclusion
As cybercriminals continue to refine their methods, the emergence of attacks like BlobPhish underscores the need for continuous vigilance and adaptation in cybersecurity practices. Organizations and individuals alike must stay informed about such sophisticated threats and employ comprehensive security strategies to mitigate potential risks.