Chinese Cyber Espionage Targets NASA: Employees Unwittingly Share Sensitive Defense Software
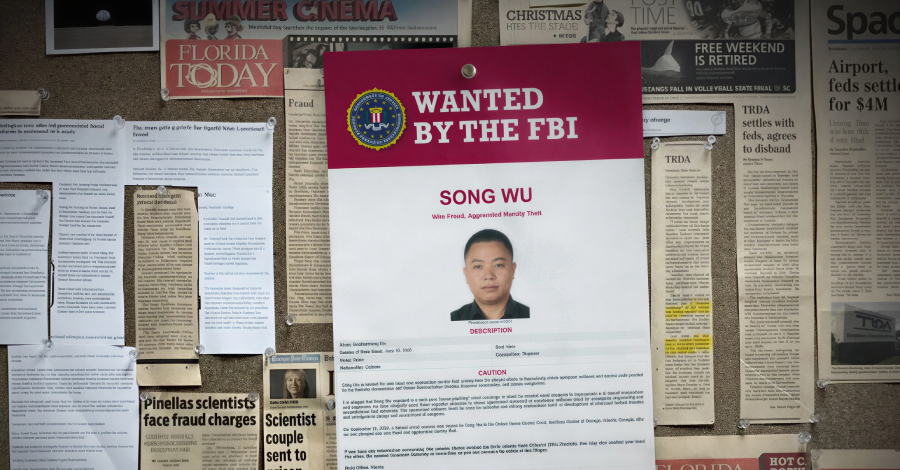
In a sophisticated cyber espionage operation, a Chinese national, Song Wu, successfully infiltrated NASA and other U.S. institutions by impersonating American researchers. This elaborate scheme led to the unauthorized acquisition of sensitive defense-related software, highlighting significant vulnerabilities in information security protocols.
The Deceptive Strategy
Between January 2017 and December 2021, Song Wu, an engineer at the Aviation Industry Corporation of China (AVIC)—a state-owned aerospace and defense conglomerate—executed a targeted spear-phishing campaign. By masquerading as colleagues and friends within the research and engineering communities, he deceived numerous individuals into sharing proprietary software and source code. This operation extended beyond NASA, affecting the Air Force, Navy, Army, Federal Aviation Administration, major universities, and private sector firms.
Unveiling the Breach
The U.S. Department of Justice (DoJ) unsealed an indictment against Song Wu in September 2024, charging him with 14 counts of wire fraud and 14 counts of aggravated identity theft. If convicted, he faces up to 20 years in prison for each wire fraud count and an additional two-year consecutive sentence for identity theft. Despite these charges, Song remains at large.
Implications for National Security
The compromised software is integral to aerospace design and weapons development, including advanced tactical missiles and aerodynamic assessments. The Federal Bureau of Investigation (FBI) emphasized that such technology has both industrial and military applications, underscoring the gravity of the breach.
Identifying Red Flags
The Office of Inspector General (OIG) highlighted several indicators that could help detect similar phishing schemes:
– Repeated Requests: Multiple solicitations for the same software without clear justification.
– Unusual Payment Methods: Suggestions of suspicious wire transfers or unconventional payment terms.
– Evasive Tactics: Abrupt changes in payment sources and the use of unconventional transfer methods to conceal identities and circumvent shipping restrictions.
Broader Context of Cyber Espionage
This incident is part of a larger pattern of cyber espionage activities attributed to Chinese state-sponsored actors. In March 2024, the DoJ charged seven Chinese nationals for their involvement in a 14-year hacking operation targeting U.S. and foreign critics, journalists, businesses, and political officials. These individuals were linked to APT31, a group known for conducting malicious cyber operations on behalf of the Hubei State Security Department.
Strengthening Cybersecurity Measures
The recurring nature of these cyber threats underscores the need for robust cybersecurity protocols. Organizations must implement comprehensive training programs to educate employees about recognizing and responding to phishing attempts. Regular audits and updates to security systems are essential to safeguard sensitive information against evolving cyber threats.
Conclusion
The infiltration of NASA and other U.S. institutions by Song Wu serves as a stark reminder of the persistent and evolving nature of cyber espionage. It highlights the critical importance of vigilance, education, and proactive security measures in protecting national security interests.