One Click, Total Shutdown: Mastering the ‘Patient Zero’ Defense Against Stealth Breaches
In the realm of cybersecurity, the most formidable challenge isn’t the technology—it’s the human element. Recent high-profile breaches often share a common origin: a single employee, an ingeniously crafted email, and the ensuing Patient Zero infection.
As we navigate through 2026, cyber adversaries are leveraging artificial intelligence to craft phishing attempts that are nearly indistinguishable from legitimate communications. This evolution raises a critical question: if one device within your organization is compromised, do you have a robust strategy to prevent a cascading failure that could incapacitate your entire enterprise?
Understanding Patient Zero
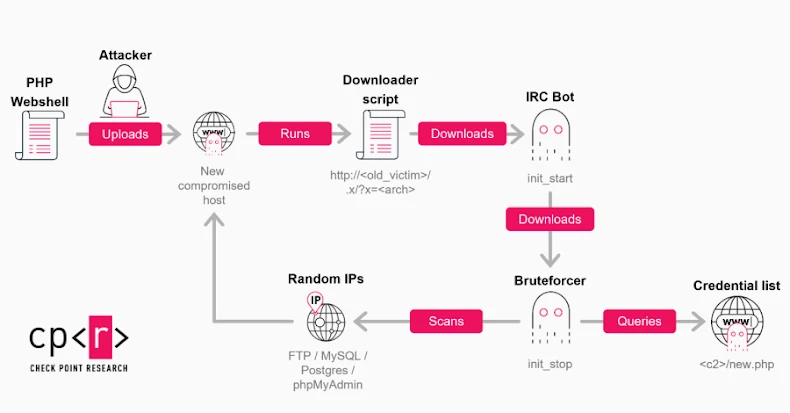
In medical parlance, Patient Zero refers to the initial individual who introduces a disease into a population. Translating this concept to cybersecurity, Patient Zero is the first device infiltrated by an attacker. Once inside, cybercriminals don’t remain static; they rapidly traverse networks to access sensitive data, credentials, and backup systems.
Key Insights from the Webinar
This isn’t your typical lecture. The upcoming webinar offers an in-depth technical exploration of modern breach methodologies and immediate countermeasures. Participants will gain insights into:
– The AI Phish: An examination of how attackers employ generative AI to circumvent existing email filters, making phishing attempts more convincing and harder to detect.
– The 5-Minute Window: An analysis of why the initial moments following an infection are pivotal in determining whether an organization can contain the breach or if it escalates into a public crisis.
– Zero Trust in Action: A practical demonstration of implementing Zero Trust principles to isolate compromised devices, effectively preventing lateral movement of threats within the network.
– The Recovery Blueprint: A step-by-step guide on immediate actions to take upon identifying a Patient Zero, ensuring rapid containment and mitigation of potential damages.
The Imperative to Attend
Traditional security tools excel at identifying known malware signatures. However, they often falter when confronted with stealthy, tailor-made attacks designed specifically for a targeted organization. This webinar is designed to equip you with the knowledge to construct a defense strategy that anticipates inevitable human errors—such as clicking on malicious links—and ensures that such incidents don’t result in catastrophic financial losses.