The Gentlemen Ransomware Group: A Sophisticated Multi-Platform Threat Targeting Global Organizations
A formidable new ransomware-as-a-service (RaaS) operation, known as The Gentlemen, has rapidly emerged as a significant threat to organizations worldwide. Since its inception in mid-2025, the group has demonstrated a well-structured and aggressive approach, publicly claiming over 320 victims. Notably, more than 240 of these attacks occurred in the early months of 2026, underscoring the group’s swift expansion and operational efficiency.
Cross-Platform Capabilities
What sets The Gentlemen apart is its ability to target multiple operating systems simultaneously. The group offers ransomware variants written in the Go programming language, enabling attacks across Windows, Linux, NAS, and BSD environments. Additionally, they have developed a separate locker in C specifically designed to compromise VMware ESXi hypervisors. This cross-platform capability allows affiliates to inflict maximum damage within a single campaign, affecting both traditional endpoints and critical virtualization infrastructures.
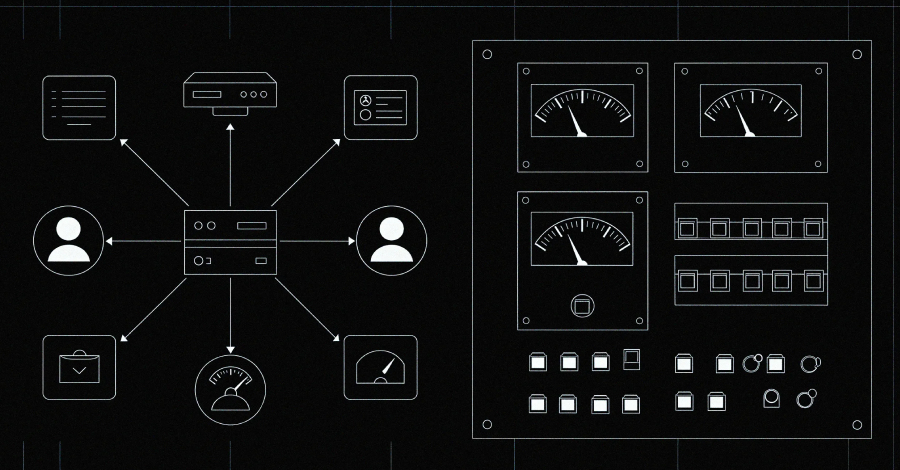
Operational Structure and Recruitment
Operating with a business-like structure, The Gentlemen actively recruit technically proficient affiliates through advertisements on underground forums. Verified partners gain access to advanced tools designed to disable endpoint detection and response (EDR) systems, as well as a private pivot infrastructure. In instances where victims refuse to pay the ransom, their data is published on a dark web leak site, while negotiations are conducted privately via Tox, a peer-to-peer encrypted messaging protocol. The group also maintains an active presence on social media platforms, such as Twitter, where they publicly name victims to increase pressure for payment.
Infection Mechanism and Lateral Movement
The Gentlemen’s attack methodology is both strategic and methodical. Initial access is often achieved through compromised Domain Controllers with administrative privileges. From this foothold, attackers deploy Cobalt Strike payloads to remote systems via administrative shares, using executables with randomized names to evade detection. Early commands, including system information queries and directory listings, indicate a deliberate effort to map the network environment before further exploitation.
For lateral movement, the ransomware utilizes a built-in spread function that leverages harvested domain credentials. It enumerates all domain computers through Active Directory, pings each host to confirm reachability, and then delivers the ransomware binary through multiple channels: PsExec, Windows Management Instrumentation (WMI), remote scheduled tasks, remote services, and PowerShell-based execution methods. Prior to executing the ransomware on each target, the attackers disable Windows Defender, add broad path exclusions for the entire C: drive, shut down the firewall, and re-enable SMB1, thereby facilitating the spread and execution of the malware.
Global Impact and Victim Profile
Analysis of telemetry from SystemBC, a proxy malware associated with The Gentlemen, reveals a botnet comprising over 1,570 victims globally. The United States accounts for the majority of infections, followed by the United Kingdom and Germany. The victim profile strongly suggests that the group deliberately targets organizations rather than individuals, aiming to maximize financial gain through substantial ransom demands.
Mitigation Strategies
Given the sophisticated nature and rapid proliferation of The Gentlemen ransomware, organizations must adopt comprehensive cybersecurity measures to mitigate the risk of infection. Recommended strategies include:
– Regular Software Updates: Ensure that all operating systems and applications are up-to-date with the latest security patches to close vulnerabilities that could be exploited by attackers.
– Network Segmentation: Implement network segmentation to limit the spread of ransomware within the organization, thereby containing potential damage.
– Endpoint Detection and Response (EDR) Solutions: Deploy advanced EDR solutions capable of detecting and responding to suspicious activities in real-time.
– User Training and Awareness: Conduct regular training sessions to educate employees about phishing attacks and other common vectors used to deliver ransomware.
– Regular Backups: Maintain regular, secure backups of critical data to facilitate recovery in the event of an attack.
By implementing these measures, organizations can enhance their resilience against The Gentlemen ransomware and similar threats, thereby safeguarding their operations and sensitive data.