In early May 2026, cybersecurity researchers uncovered a sophisticated supply chain attack targeting DAEMON Tools, a widely used disk image mounting software. Malicious actors compromised official installers distributed from the legitimate DAEMON Tools website, embedding malware that has since affected users across more than 100 countries.
Scope and Nature of the Attack
The attack was first identified by Kaspersky security researchers, who noted that the compromised installers were available for download starting April 8, 2026. These installers, spanning versions 12.5.0.2421 to 12.5.0.2434, were signed with valid digital certificates from AVB Disc Soft, the software’s developer. This use of legitimate certificates allowed the malicious installers to bypass many security measures, making detection more challenging.
The attackers demonstrated a high degree of selectivity in their operations. While thousands of infection attempts were recorded globally, the threat actors focused their post-compromise activities on a limited number of high-value targets. Artifacts within the malicious implants suggest the involvement of a Chinese-speaking threat actor, though definitive attribution remains unconfirmed.
Technical Details of the Compromise
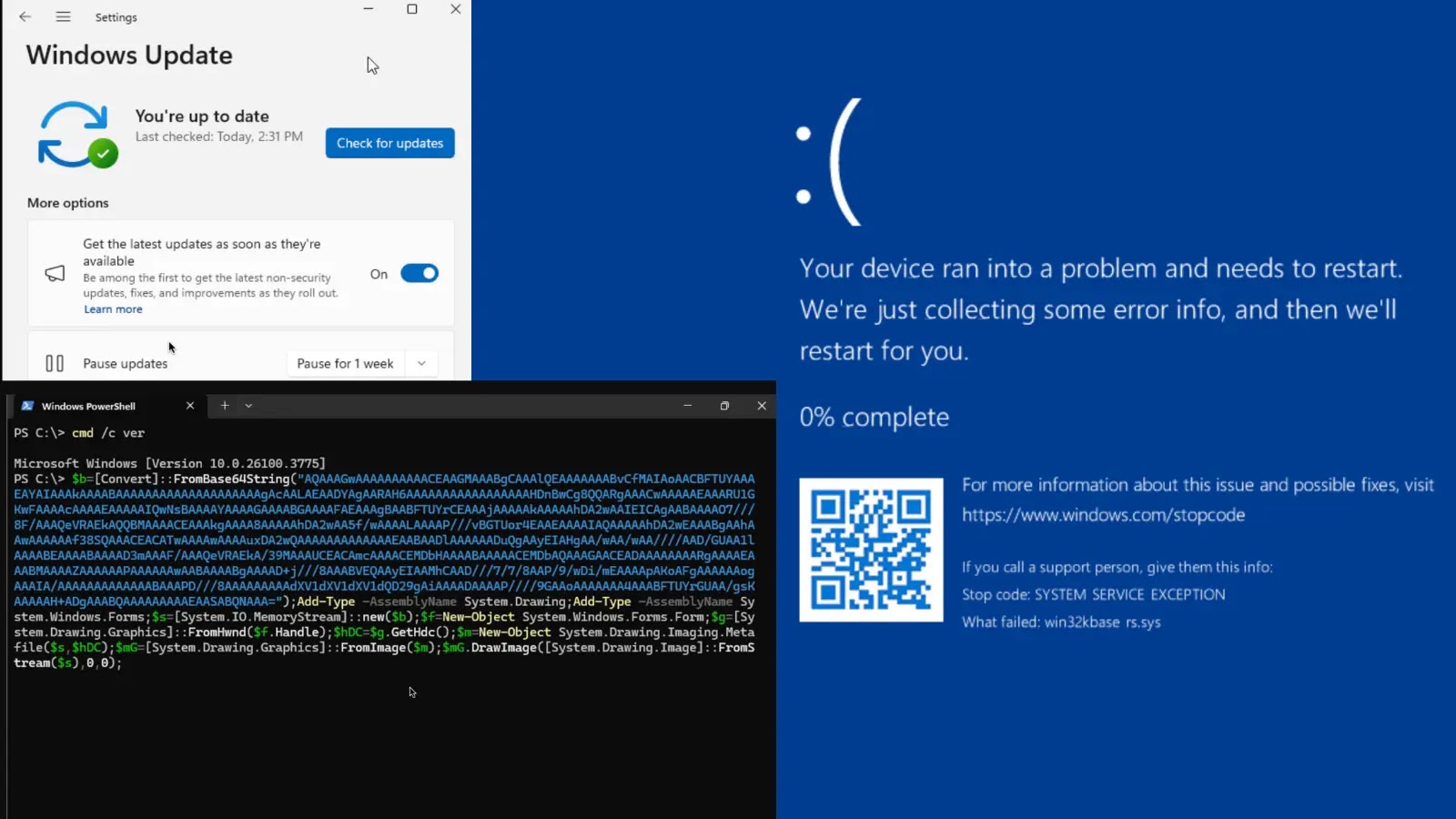
The attack sequence initiates when specific compromised binaries within the DAEMON Tools installation directory are executed. These binaries include DTHelper.exe, DiscSoftBusServiceLite.exe, and DTShellHlp.exe. Upon execution, a backdoor embedded in the C Runtime initialization code activates, operating in a dedicated thread. This backdoor initiates HTTP GET requests to a command-and-control (C2) server designed to closely resemble the legitimate DAEMON Tools domain—a technique known as typosquatting.
The C2 server, registered shortly before the campaign began, responds with shell commands that utilize PowerShell to download and execute the first-stage payload. This initial payload functions as an advanced information collector, gathering extensive system profiling data such as MAC addresses, hostnames, running processes, installed software, and system locales. Notably, the .NET executable contains strings written in Chinese, providing early clues about the potential origin of the operators.
Targeted Exploitation and Secondary Payloads
Telemetry data indicates that the threat actors sifted through the massive volume of profiling data to select high-value targets for further exploitation. Out of thousands of initial infections, only about a dozen machines belonging to government, scientific, manufacturing, and retail sectors in Russia, Belarus, and Thailand received a secondary payload.
This second stage involves deploying a minimalistic backdoor via a shellcode loader that uses RC4 encryption to execute the malicious payload directly in memory. Researchers noted misspellings such as chiper and rypto.dll in the deployment commands, suggesting that this phase involved manual execution by the attackers.
Deployment of QUIC RAT
For the most valuable targets, this minimalistic backdoor facilitated the deployment of an even more sophisticated implant dubbed QUIC RAT. Identified exclusively on the network of a Russian educational institution, QUIC RAT is a highly obfuscated C++ backdoor statically linked with the WolfSSL library. It supports a vast array of communication protocols, including HTTP/3 and QUIC, and actively injects payloads into core system processes like notepad.exe and conhost.exe to evade detection.
Implications and Recommendations
This incident underscores the growing threat of supply chain attacks, where trusted software is compromised to distribute malware. Such attacks can have far-reaching consequences, as they exploit the trust users place in legitimate software providers.
To mitigate the risks associated with such attacks, users and organizations are advised to:
– Verify Software Integrity: Always download software from official sources and verify the integrity of the installer through checksums or digital signatures.
– Maintain Updated Security Measures: Ensure that antivirus and anti-malware solutions are up to date to detect and prevent the execution of malicious code.
– Monitor Network Traffic: Regularly monitor network traffic for unusual patterns that may indicate communication with malicious C2 servers.
– Implement Least Privilege Principles: Limit user permissions to the minimum necessary to reduce the potential impact of compromised accounts.
– Stay Informed: Keep abreast of the latest cybersecurity threats and vulnerabilities to respond promptly to emerging risks.
In response to this attack, AVB Disc Soft has been notified to facilitate immediate remediation. Users who have downloaded DAEMON Tools installers between April 8 and May 5, 2026, are strongly encouraged to verify their systems for potential compromise and take appropriate remedial actions.
Conclusion
The compromise of DAEMON Tools highlights the critical importance of supply chain security in the digital age. As attackers continue to refine their methods, both software providers and users must remain vigilant to protect against such sophisticated threats.