Cybercriminals Exploit Event Invitations to Steal Credentials and Deploy Malware
A sophisticated phishing campaign is currently targeting organizations across the United States, utilizing deceptive event invitations to compromise security. These seemingly legitimate invitations serve as a conduit for attackers to steal login credentials and install remote management software on victims’ systems.
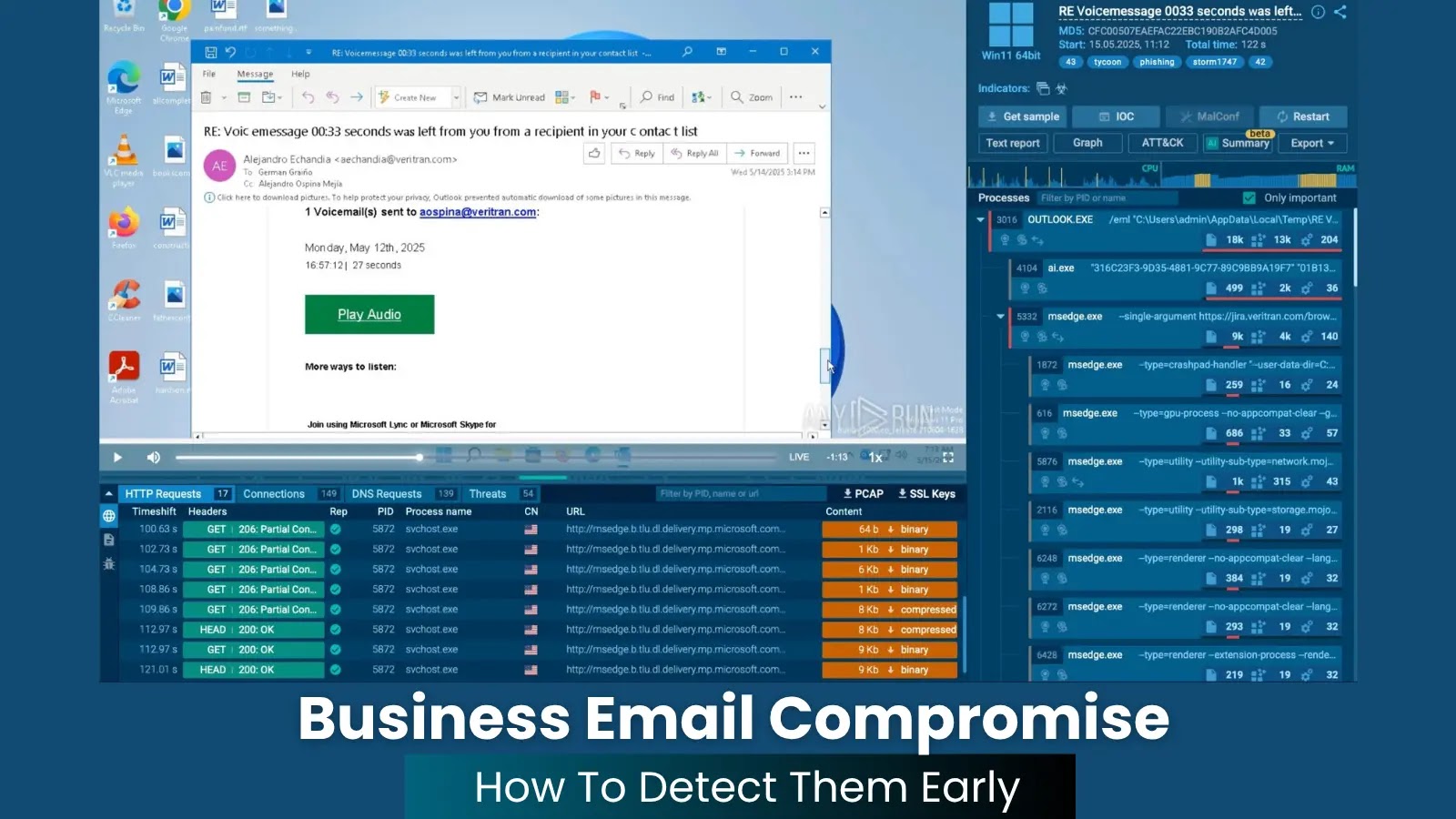
The Deceptive Tactic
The attack initiates with an email containing an event invitation that appears authentic. Upon clicking the provided link, recipients are directed to a webpage that closely resembles a genuine event page. This page often includes a CAPTCHA verification, adding an extra layer of perceived legitimacy. Once the CAPTCHA is completed, the victim is presented with a sign-in prompt, requesting their email credentials.
In some instances, selecting a service like Google redirects the user to a counterfeit Google authorization form. Credentials entered here are transmitted to the attackers via specific server endpoints, such as /pass.php and /mlog.php. For other email services, the page collects the email and password directly, facilitating unauthorized access to the victim’s account.
Scope and Impact
Research by cybersecurity firm ANY.RUN has revealed the extensive reach of this campaign. Between April 22 and April 27, 2026, nearly 160 suspicious links were identified, leading to approximately 80 phishing domains, many registered under the .de top-level domain since December 2025.
The sectors most affected include Education, Banking, Government, Technology, and Healthcare. These industries are particularly vulnerable due to their reliance on email communications and remote administration tools. A single compromised account in these fields can lead to significant security breaches, data theft, and operational disruptions.
Technical Execution
The attackers employ a reusable phishing toolkit, enabling the rapid creation of event-themed lure sites. Some elements of these pages suggest the use of AI-assisted content generation, allowing for swift expansion of the attack while maintaining a consistent structure that can be detected by vigilant security measures.
The attack chain typically follows these steps:
1. Invitation Email: The victim receives an email with an event invitation link.
2. CAPTCHA Verification: Clicking the link leads to a CAPTCHA page, often served through Cloudflare, enhancing the appearance of legitimacy.
3. Credential Harvesting: After completing the CAPTCHA, the victim is prompted to log in, leading to credential theft.
4. Malware Deployment: In some cases, the page initiates the download of remote management software, granting attackers control over the victim’s system.
Preventive Measures
To mitigate the risk posed by such phishing campaigns, organizations and individuals should adopt the following practices:
– Verify Invitations: Confirm the authenticity of event invitations through direct communication with the purported sender.
– Inspect URLs: Hover over links to check their actual destination before clicking.
– Enable Multi-Factor Authentication (MFA): Implement MFA to add an extra layer of security to accounts.
– Educate Employees: Conduct regular training sessions on recognizing phishing attempts and the importance of cybersecurity hygiene.
– Utilize Security Tools: Deploy email filtering solutions and endpoint protection to detect and block phishing attempts.
Conclusion
The exploitation of event invitations in phishing campaigns underscores the evolving tactics of cybercriminals. By staying informed and implementing robust security measures, organizations can protect themselves against these deceptive attacks.