Over 1,370 Microsoft SharePoint Servers Exposed to Critical Spoofing Vulnerability
A significant security flaw, identified as CVE-2026-32201, has been discovered in Microsoft SharePoint Server, leaving over 1,370 internet-facing servers vulnerable to potential spoofing attacks. This vulnerability, stemming from improper input validation within SharePoint’s request processing component, allows unauthenticated remote attackers to impersonate legitimate users, thereby accessing or manipulating sensitive organizational data.
Microsoft disclosed this vulnerability on April 14, 2026, during its April Patch Tuesday update, which addressed a total of 169 vulnerabilities. The affected versions include SharePoint Server 2016, 2019, and the Subscription Edition. Concurrently, the Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2026-32201 to its Known Exploited Vulnerabilities (KEV) catalog, citing confirmed evidence of active exploitation. CISA has set a federal remediation deadline of April 28, 2026, emphasizing the urgency of addressing this issue.
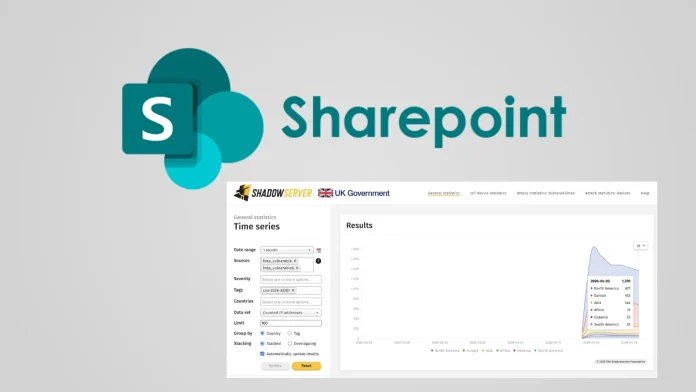
The Shadowserver Foundation’s recent scans have identified 1,370 unpatched IP addresses exposed to this vulnerability as of April 20, 2026. The geographic distribution of these vulnerable servers is as follows:
– North America: 677 servers, with the United States accounting for 587.
– Europe: 452 servers.
– Asia: 144 servers.
– Oceania: 33 servers.
– South America: 33 servers.
– Africa: 31 servers.
The United States has the highest concentration of vulnerable SharePoint deployments, followed by significant clusters in Europe, particularly in Germany, France, and the UK.
Despite its Medium CVSS rating of 6.5, CVE-2026-32201 poses a severe risk due to its pre-authentication nature, meaning attackers do not require credentials to exploit it. Potential consequences include credential theft, data exfiltration, unauthorized document access, and lateral movement within enterprise networks.
Mitigation Steps:
Organizations are urged to take the following immediate actions:
1. Apply Security Updates: Implement Microsoft’s April 2026 Patch Tuesday security updates for all supported SharePoint Server versions (2016, 2019, Subscription Edition).
2. Audit Deployments: Review internet-facing SharePoint deployments and limit public exposure where feasible.
3. Monitor Activity: Keep an eye out for unusual authentication activities and signs of spoofed sessions.
4. Prioritize Remediation: Refer to CISA’s KEV catalog and address CVE-2026-32201 before the April 28 federal deadline.
Given the active exploitation of this vulnerability, organizations must act swiftly to secure their SharePoint environments and protect sensitive data from potential breaches.