Microsoft Addresses Critical Entra ID Role Vulnerability Allowing Service Principal Takeover
Microsoft has recently addressed a significant security vulnerability within its Entra ID system, which could have permitted unauthorized users to escalate privileges and assume control over service principals. This flaw was identified in the Agent ID Administrator role, a built-in function designed to manage the identity lifecycle of artificial intelligence (AI) agents within a tenant.
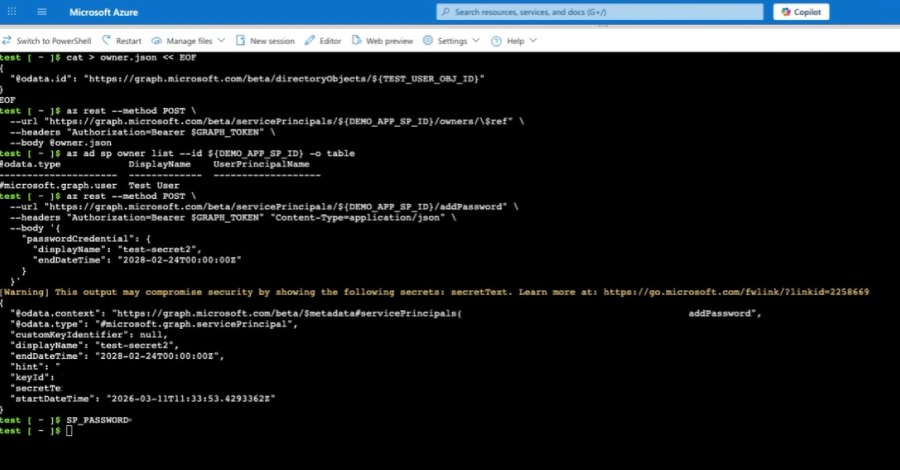
The Agent ID Administrator role is integral to Microsoft’s agent identity platform, facilitating secure authentication and resource access for AI agents, as well as enabling them to discover other agents. However, security researchers at Silverfort discovered that individuals assigned this role could exploit it to gain ownership of any service principal, not limited to those associated with AI agents. By becoming an owner, these individuals could add their own credentials, effectively allowing them to authenticate as the service principal.
Noa Ariel, a security researcher at Silverfort, highlighted the severity of this issue, stating, That’s full service principal takeover. In tenants where high-privileged service principals exist, it becomes a privilege escalation path. This means that attackers could operate within the permissions of the compromised service principal. If the targeted service principal possessed elevated permissions—such as privileged directory roles or high-impact Graph app permissions—the attacker could gain extensive control over the tenant.
Upon responsible disclosure of the vulnerability on March 1, 2026, Microsoft acted promptly, releasing a patch across all cloud environments by April 9. The update prevents the Agent ID Administrator role from assigning ownership over non-agent service principals. Attempts to do so now result in a Forbidden error message, effectively mitigating the risk.
Silverfort emphasized the importance of validating role scopes and permission applications, especially when new identity types are built upon existing frameworks. To further safeguard against such vulnerabilities, organizations are advised to:
– Monitor Sensitive Role Usage: Keep a close watch on roles related to service principal ownership or credential modifications.
– Track Service Principal Ownership Changes: Regularly review and document any changes in ownership to detect unauthorized alterations.
– Secure Privileged Service Principals: Implement stringent security measures to protect service principals with elevated permissions.
– Audit Credential Creation on Service Principals: Conduct thorough audits of credential creation activities to identify and address potential security breaches.
Ariel further noted, Agent identities are part of the broader shift toward non-human identities, built for the age of AI agents. When role permissions are applied on top of shared foundations without strict scoping, access can extend beyond what was originally intended. In this case, that gap led to broader access, especially when privileged service principals were involved.
This incident underscores the critical need for organizations to continuously assess and refine their identity management practices, ensuring that roles and permissions are appropriately scoped to prevent unauthorized access and potential security breaches.