Critical Vulnerability in Microsoft Entra ID’s Agent ID Administrator Role Enables Service Principal Hijacking
A significant security flaw has been discovered within Microsoft’s Entra ID, specifically involving the Agent ID Administrator role. This vulnerability permitted unauthorized users to assume control over service principals, potentially leading to extensive privilege escalation across entire organizational tenants. Microsoft has since addressed and patched this issue as of April 2026.
Understanding the Vulnerability
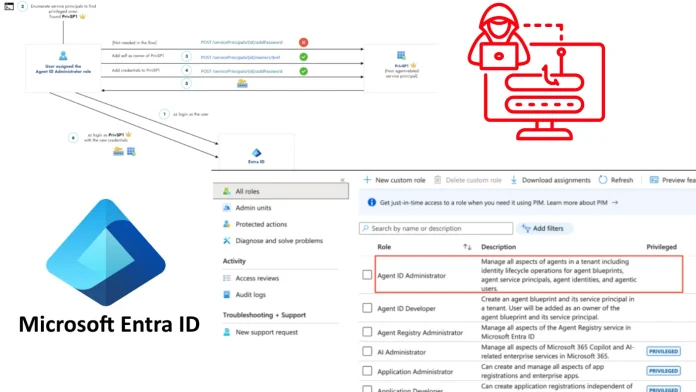
Microsoft’s Entra ID introduced the Agent Identity Platform to provide artificial intelligence agents with distinct identities, utilizing components such as blueprints, agent identities, and agent users. To manage these non-human entities, the Agent ID Administrator role was established, purportedly confined to overseeing agent-related objects. However, due to the foundational structure of agent identities being built upon standard application and service principal frameworks, a critical oversight emerged.
Researchers at Silverfort identified that the Agent ID Administrator role could be exploited to alter the ownership of any service principal within the tenant. This manipulation allowed individuals with the Agent ID Administrator role to assign themselves as owners of unrelated, high-privilege service principals. Once ownership was established, the attacker could generate new credentials and authenticate as the targeted application. If the compromised service principal possessed elevated directory roles or significant Graph API permissions, this takeover could lead to a full-scale compromise of the environment.
Potential Impact
The exploitation of this vulnerability posed severe risks, including:
– Privilege Escalation: Attackers could elevate their access rights, gaining control over critical organizational resources.
– Data Breach: Unauthorized access to sensitive information could result in data leaks or theft.
– Operational Disruption: Malicious actors could disrupt services, leading to downtime and operational inefficiencies.
Microsoft’s Response
Upon identification of the vulnerability, Microsoft acted promptly to remediate the issue. By April 2026, the company had fully patched the flaw across all cloud environments, ensuring that the Agent ID Administrator role could no longer be exploited to hijack service principals.
Recommendations for Organizations
To safeguard against similar vulnerabilities and enhance security posture, organizations are advised to:
1. Review Role Assignments: Regularly audit and review role assignments within Entra ID to ensure that permissions are appropriately granted and scoped.
2. Monitor Service Principals: Identify and monitor service principals with elevated privileges, ensuring they are secured and their usage is justified.
3. Implement Least Privilege Principle: Assign roles and permissions based on the minimum necessary access required for users to perform their duties.
4. Stay Informed: Keep abreast of security updates and patches released by Microsoft to promptly address potential vulnerabilities.
Conclusion
The discovery and subsequent patching of the vulnerability within Microsoft’s Entra ID underscore the importance of continuous vigilance and proactive security measures. Organizations must remain diligent in monitoring and managing their identity and access management systems to prevent unauthorized access and potential breaches.