Enhancing SOC Maturity Through Integrated Threat Intelligence Feeds
Security Operations Centers (SOCs) are the frontline defense against cyber threats, yet many struggle to evolve beyond reactive measures due to fragmented and outdated threat intelligence. To achieve true maturity, SOCs must embed real-time, contextual threat intelligence directly into their workflows, transforming data into actionable insights that drive faster detection, accurate triage, and effective response.
The Stagnation of SOC Maturity Without Integrated Intelligence
Despite investments in advanced tools like Security Information and Event Management (SIEM), Endpoint Detection and Response (EDR), and Security Orchestration, Automation, and Response (SOAR) systems, many SOCs face persistent challenges:
– Alert Fatigue: Analysts are overwhelmed by a deluge of alerts, many of which are false positives, leading to burnout and missed genuine threats.
– Delayed Detection: Without timely intelligence, SOCs often detect threats only after significant damage has occurred.
– Inconsistent Response Quality: Lack of contextual information hampers the ability to prioritize and respond effectively to incidents.
These issues often stem from reliance on fragmented threat data that requires manual validation and correlation, slowing decision-making and creating operational friction. Achieving SOC maturity necessitates a shift to continuous, contextual intelligence seamlessly integrated into operations.
Transforming Data into Operational Intelligence
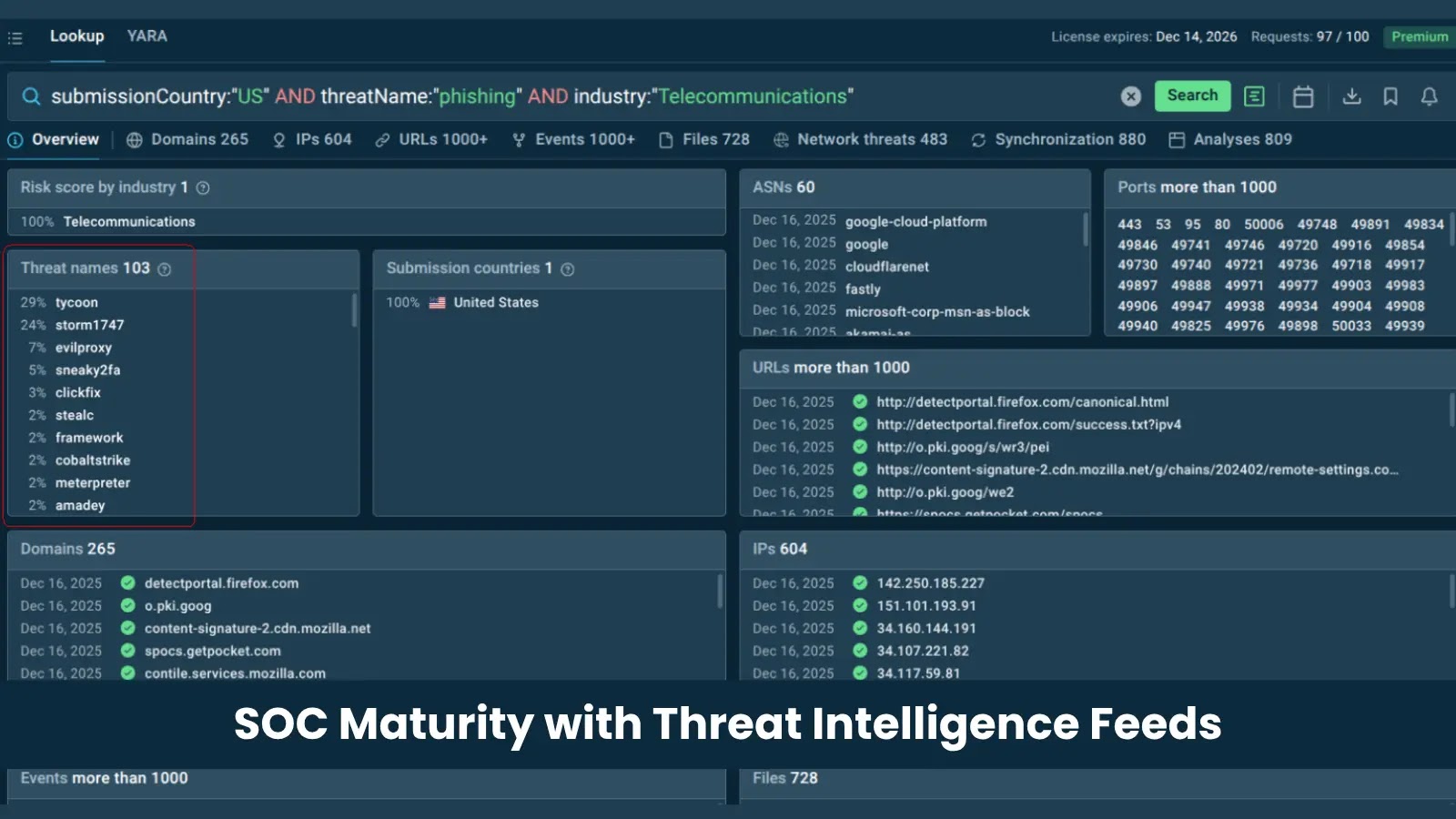
ANY.RUN’s Threat Intelligence Feeds offer a solution by delivering real-time, validated indicators directly into existing security pipelines. Sourced from live attack investigations conducted by thousands of organizations worldwide, these feeds provide immediate visibility into emerging threats.
Key benefits include:
– Automated Context Delivery: Eliminates the need for manual enrichment by providing comprehensive threat data.
– Early Detection: Continuous updates ensure detection systems are equipped with the latest indicators, reducing dwell time.
– Integrated Operations: Seamless integration into SIEM and SOAR platforms via STIX/TAXII protocols enhances workflow efficiency.
By embedding these feeds, SOCs can transition from reactive to proactive defense, improving alert quality and reducing manual workload.
Operational Impact of Integrated Threat Intelligence
Organizations across various industries have realized significant operational improvements by integrating ANY.RUN’s Threat Intelligence Feeds:
– Reduced Dwell Time: Real-time Indicator of Compromise (IOC) streams enable earlier detection of threats.
– Enhanced Alert Quality: Automated enrichment provides context, reducing false positives and alert fatigue.
– Efficient Resource Utilization: Analysts can focus on high-priority threats, improving response times and reducing burnout.
This integration not only strengthens the security posture but also optimizes resource allocation, leading to a more resilient and efficient SOC.
Conclusion
Achieving SOC maturity requires more than just advanced tools; it demands the integration of real-time, contextual threat intelligence into daily operations. ANY.RUN’s Threat Intelligence Feeds provide the continuous, validated data necessary to transform SOCs from reactive to proactive defenders, enhancing detection capabilities, streamlining workflows, and ultimately fortifying organizational security.