Hackers Deface School Login Pages Amid Instructure Data Breach Fallout
In a recent escalation of cyberattacks targeting educational institutions, the notorious hacking group ShinyHunters has defaced multiple school login pages associated with Instructure’s Canvas platform. This development follows closely on the heels of a significant data breach disclosed by Instructure, the company behind Canvas, a widely used learning management system (LMS).
Initial Data Breach Disclosure
On May 1, 2026, Instructure confirmed a cybersecurity incident that compromised sensitive user information. The breach exposed names, email addresses, student ID numbers, and messages exchanged between students and instructors. Notably, the company stated that passwords, birth dates, government identifiers, and financial information were not affected. The ShinyHunters group claimed responsibility for this attack, alleging they had stolen data from nearly 9,000 schools worldwide, impacting approximately 275 million individuals. ([malwarebytes.com](https://www.malwarebytes.com/blog/news/2026/05/millions-of-students-personal-data-stolen-in-major-education-cyberattack?utm_source=openai))
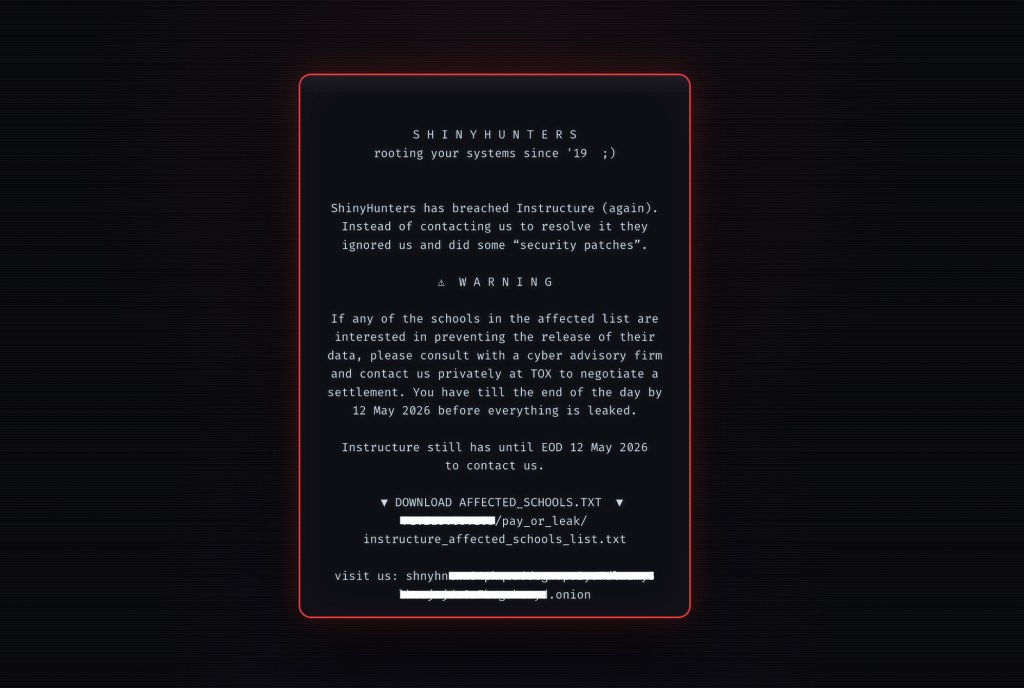
Defacement of School Login Pages
Shortly after the initial breach, ShinyHunters escalated their activities by defacing the login pages of several schools utilizing the Canvas platform. The hackers injected HTML code into these pages, displaying messages threatening to release the stolen data publicly if Instructure did not negotiate a settlement by May 12. This tactic aims to increase pressure on Instructure and its clients to comply with the hackers’ demands.
Impact on Educational Institutions
The defacement and data breach have had widespread repercussions across the educational sector. Institutions relying on Canvas for managing coursework, assignments, and communication have faced disruptions. For instance, the University of Massachusetts Amherst described the event as a vendor-driven national event affecting multiple institutions. ([claimdepot.com](https://www.claimdepot.com/data-breach/instructure-inc-2026?utm_source=openai)) The breach has raised concerns about the security of third-party educational platforms and the potential exposure of sensitive student and staff information.
Instructure’s Response and Ongoing Investigation
In response to the incidents, Instructure has been working with external forensic experts to investigate the breaches and assess the full scope of the compromised data. The company has implemented measures such as revoking certain credentials and access tokens, increasing monitoring, and enhancing security protocols. Instructure has also communicated with affected institutions, providing guidance on mitigating potential risks and reinforcing security practices. ([tech.co](https://tech.co/news/edtech-instructure-confirms-data-breach?utm_source=openai))
ShinyHunters’ Modus Operandi
ShinyHunters is a cybercriminal group known for its financially motivated attacks. Their typical strategy involves infiltrating organizations, exfiltrating sensitive data, and then extorting victims by threatening to release the information unless a ransom is paid. In this case, the group has utilized both data theft and public defacement to pressure Instructure and the affected educational institutions.
Broader Implications for Cybersecurity in Education
This series of attacks underscores the vulnerabilities present in educational technology platforms and the critical need for robust cybersecurity measures. Educational institutions are increasingly becoming targets for cybercriminals due to the vast amounts of sensitive data they handle. The incidents involving Instructure highlight the importance of proactive security practices, regular system audits, and comprehensive incident response plans to protect against and respond to cyber threats effectively.
Recommendations for Educational Institutions
In light of these events, educational institutions should consider the following actions:
1. Review and Strengthen Security Protocols: Conduct thorough assessments of current security measures and implement necessary enhancements to protect against potential breaches.
2. Educate Staff and Students: Provide training on recognizing phishing attempts, the importance of strong passwords, and safe online practices to reduce the risk of credential compromise.
3. Implement Multi-Factor Authentication (MFA): Enforce MFA across all platforms to add an additional layer of security beyond just passwords.
4. Regularly Update and Patch Systems: Ensure that all software and systems are up to date with the latest security patches to mitigate vulnerabilities.
5. Develop and Test Incident Response Plans: Establish clear protocols for responding to security incidents and conduct regular drills to ensure preparedness.
Conclusion
The recent cyberattacks targeting Instructure’s Canvas platform serve as a stark reminder of the evolving threats facing the education sector. As cybercriminals employ increasingly sophisticated tactics, it is imperative for educational institutions and technology providers to collaborate closely, share threat intelligence, and adopt comprehensive security strategies to safeguard sensitive information and maintain the trust of students, educators, and stakeholders.