Unveiling PhantomRPC: A Critical Windows RPC Vulnerability Enabling Privilege Escalation Across All Versions
A significant security flaw, dubbed PhantomRPC, has been uncovered within the Windows Remote Procedure Call (RPC) architecture, potentially allowing attackers to escalate privileges to SYSTEM level across all Windows versions. This vulnerability, rooted in the architectural design of the Windows RPC runtime (rpcrt4.dll), was detailed by Kaspersky’s application security specialist, Haidar Kabibo, at the Black Hat Asia 2026 conference on April 24.
Unlike traditional vulnerabilities that stem from memory corruption or logic errors in specific components, PhantomRPC exploits a fundamental design weakness in how the Windows RPC runtime manages connections to unavailable RPC servers. When a high-privilege process initiates an RPC call to a server that is offline or disabled, the RPC runtime fails to verify the authenticity of the responding server. This oversight allows an attacker, operating a low-privilege process under accounts like NT AUTHORITY\NETWORK SERVICE, to set up a malicious RPC server that impersonates a legitimate endpoint and intercepts these calls.
The exploitation hinges on the `RpcImpersonateClient` API. When a privileged client connects to the attacker’s fake server with a high impersonation level, the malicious server can invoke this API to adopt the client’s security context, effectively escalating the attacker’s privileges from a low-level service account to SYSTEM or Administrator.
Five Exploitation Scenarios Identified:
1. gpupdate.exe Coercion: Executing `gpupdate /force` prompts the Group Policy Client service, running as SYSTEM, to make an RPC call to TermService. If TermService is disabled, the attacker’s fake RPC server can intercept this call, granting SYSTEM-level access.
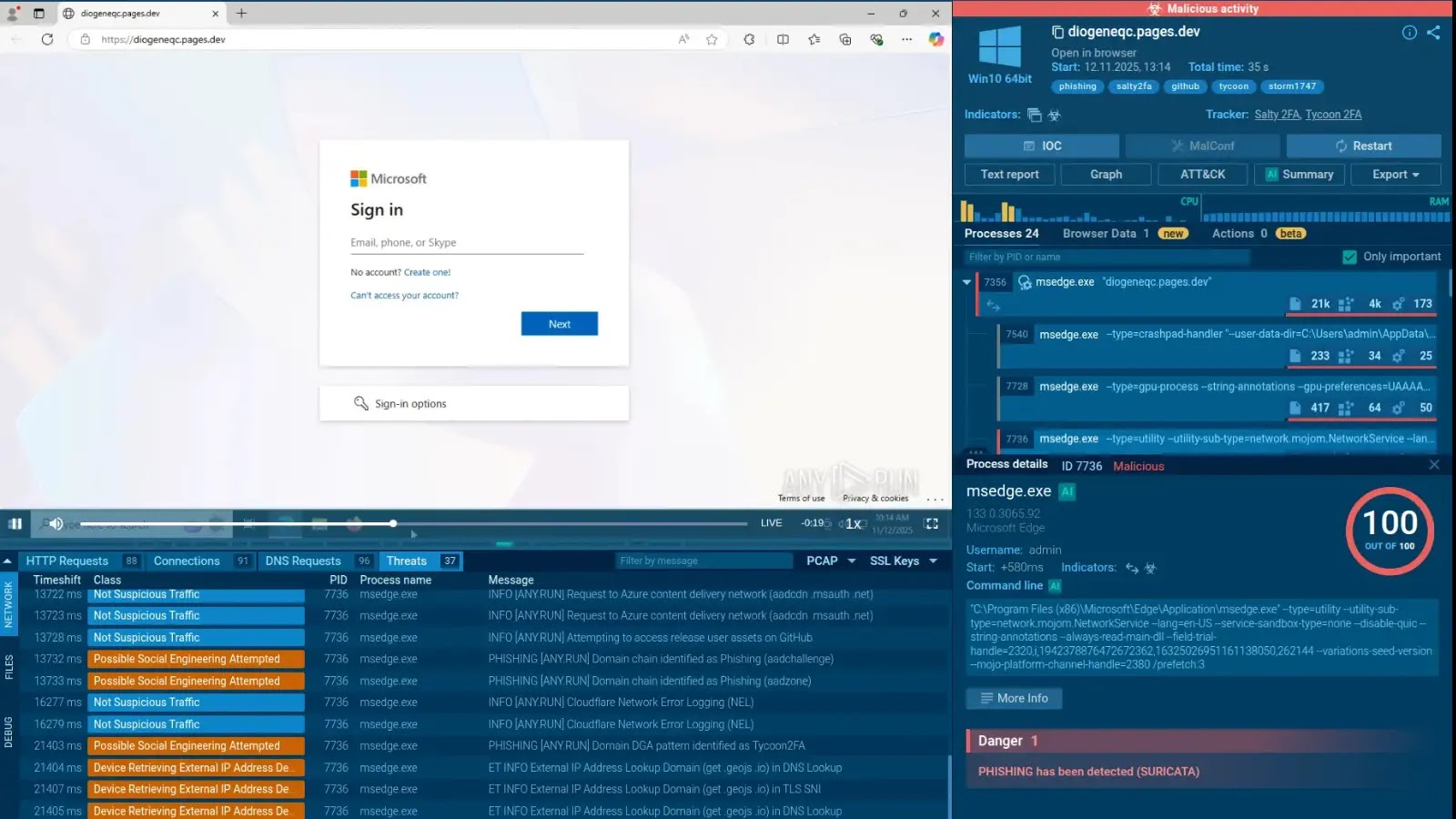
2. Microsoft Edge Startup: Launching msedge.exe triggers an RPC call to TermService with a high impersonation level. An attacker with a spoofed endpoint can escalate from Network Service to Administrator without any user interaction.
3. WDI Background Service: The Diagnostic System Host (WdiSystemHost), operating as SYSTEM, periodically contacts TermService every 5–15 minutes. An attacker can passively wait for this automated call to intercept and escalate privileges.
4. ipconfig.exe and DHCP Client: Running `ipconfig.exe` initiates an internal RPC call to the DHCP Client service. If DHCP is disabled and a fake server is in place, an attacker with Local Service privileges can escalate to Administrator.
5. w32tm.exe and Windows Time: The Windows Time executable attempts to connect to a nonexistent named pipe `\PIPE\W32TIME`. An attacker can expose this endpoint without disabling the legitimate W32Time service, then impersonate any privileged user who runs the binary.
These scenarios demonstrate the versatility and severity of the PhantomRPC vulnerability, highlighting the need for immediate attention and remediation.
Microsoft’s Response and Current Status:
The vulnerability was reported to the Microsoft Security Response Center (MSRC) on September 19, 2025. Microsoft responded 20 days later, classifying the issue as moderate severity, citing that the attack requires `SeImpersonatePrivilege`, a privilege already held by default by Network Service and Local Service accounts. Consequently, no Common Vulnerabilities and Exposures (CVE) identifier was assigned, and the case was closed without a scheduled fix.
Mitigation Strategies:
In the absence of an official patch, organizations and users are advised to implement the following measures to mitigate potential exploitation:
– Enable ETW-Based RPC Monitoring: Utilize Event Tracing for Windows (ETW) to monitor for `RPC_S_SERVER_UNAVAILABLE` errors, which can indicate attempts to exploit this vulnerability.
– Restrict Privileges: Limit the use of service accounts with `SeImpersonatePrivilege` to essential services only, reducing the risk of privilege escalation.
– Regular Audits: Conduct regular audits of RPC server availability and monitor for unauthorized or suspicious RPC servers within the network.
– Network Segmentation: Implement network segmentation to isolate critical systems and services, minimizing the potential impact of an exploit.
By proactively adopting these strategies, organizations can enhance their security posture against potential exploits targeting the PhantomRPC vulnerability.
Conclusion:
The discovery of PhantomRPC underscores the importance of continuous vigilance and proactive security measures in the face of evolving cyber threats. While Microsoft has not issued a patch for this vulnerability, understanding its mechanics and implementing recommended mitigations can significantly reduce the risk of exploitation. Organizations are encouraged to stay informed about emerging vulnerabilities and to adopt a comprehensive approach to cybersecurity that includes regular system updates, privilege management, and network monitoring.