Veeam Addresses Seven Critical Vulnerabilities in Backup & Replication Software Veeam has recently released security updates to rectify seven critical vulnerabilities in its Backup & […]
Archives
OAuth Exploits, EDR Bypasses, Messaging App Attacks Highlight Latest Cybersecurity Threats
Emerging Cyber Threats: OAuth Exploits, EDR Bypasses, and Messaging App Attacks In the ever-evolving landscape of cybersecurity, recent developments have unveiled sophisticated tactics employed by […]
New Android Malware Targets Pix Payments, Banking Apps, and Crypto Wallets in Brazil
Emerging Android Malware Threatens Pix Payments, Banking Apps, and Crypto Wallets Cybersecurity experts have recently identified six new Android malware families designed to infiltrate devices, […]
Rust-Based VENON Trojan Targets Brazilian Banks with Advanced Evasion Techniques
Emergence of VENON: A Rust-Based Banking Trojan Targeting Brazilian Financial Institutions Cybersecurity experts have recently identified a sophisticated banking malware named VENON, which is specifically […]
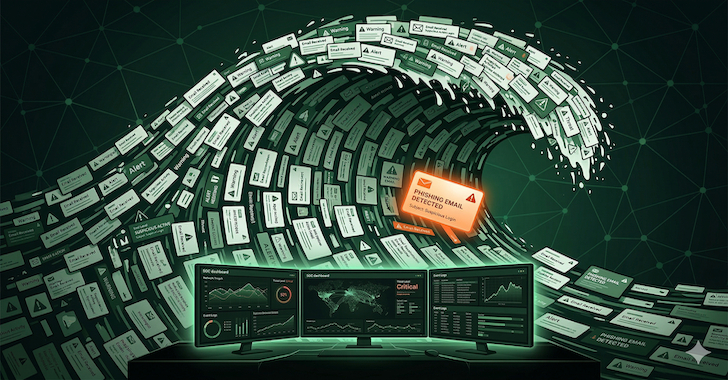
CISOs Urged to Scale SOCs for Advanced Phishing Detection and Response
Scaling Phishing Detection in Your SOC: A Strategic Guide for CISOs Phishing has evolved into a sophisticated threat, leveraging trusted infrastructures and encrypted communications to […]
AI-Generated Slopoly Malware Emerges: Hive0163 Boosts Ransomware Persistence with New AI Tools
Hive0163’s AI-Generated Slopoly Malware Enhances Ransomware Persistence In a significant development within the cybersecurity landscape, researchers have unveiled details about Slopoly, a malware believed to […]
Critical n8n Vulnerability Exposes Over 24,700 Instances to Remote Code Execution Risk
Critical n8n Vulnerability Exploited: Over 24,700 Instances at Risk The Cybersecurity and Infrastructure Security Agency (CISA) has recently added a critical security flaw affecting the […]
Authorities Dismantle Global Proxy Botnet Exploiting 369,000 IPs in Major Cybercrime Bust
Authorities Dismantle Global SocksEscort Proxy Botnet Exploiting 369,000 IPs In a significant international law enforcement operation, authorities have successfully dismantled the SocksEscort proxy botnet, a […]
Phishing Attacks Overwhelm SOCs with IDoS Tactics, Threatening Cybersecurity Defenses
Phishing Attacks Evolve: Overwhelming SOCs to Breach Defenses In the ever-evolving landscape of cyber threats, phishing attacks have transcended their traditional boundaries. No longer solely […]
Apple Issues Security Updates for Older iOS Devices to Tackle Coruna WebKit Exploit Vulnerability
Apple Releases Critical Security Updates for Older iOS Devices to Counter Coruna WebKit Exploit In a proactive move to safeguard users of older devices, Apple […]