Cyber attackers are increasingly targeting cloud logging services like AWS CloudTrail and Google Cloud Logging to conceal their activities and exfiltrate sensitive data. These services, […]
Archives
WhatsApp to Require iOS 15.5 on Older iPhones by November 2026
WhatsApp has announced that, starting November 30, 2026, the messaging app will require iOS 15.5 or later to function, an increase from the current requirement […]
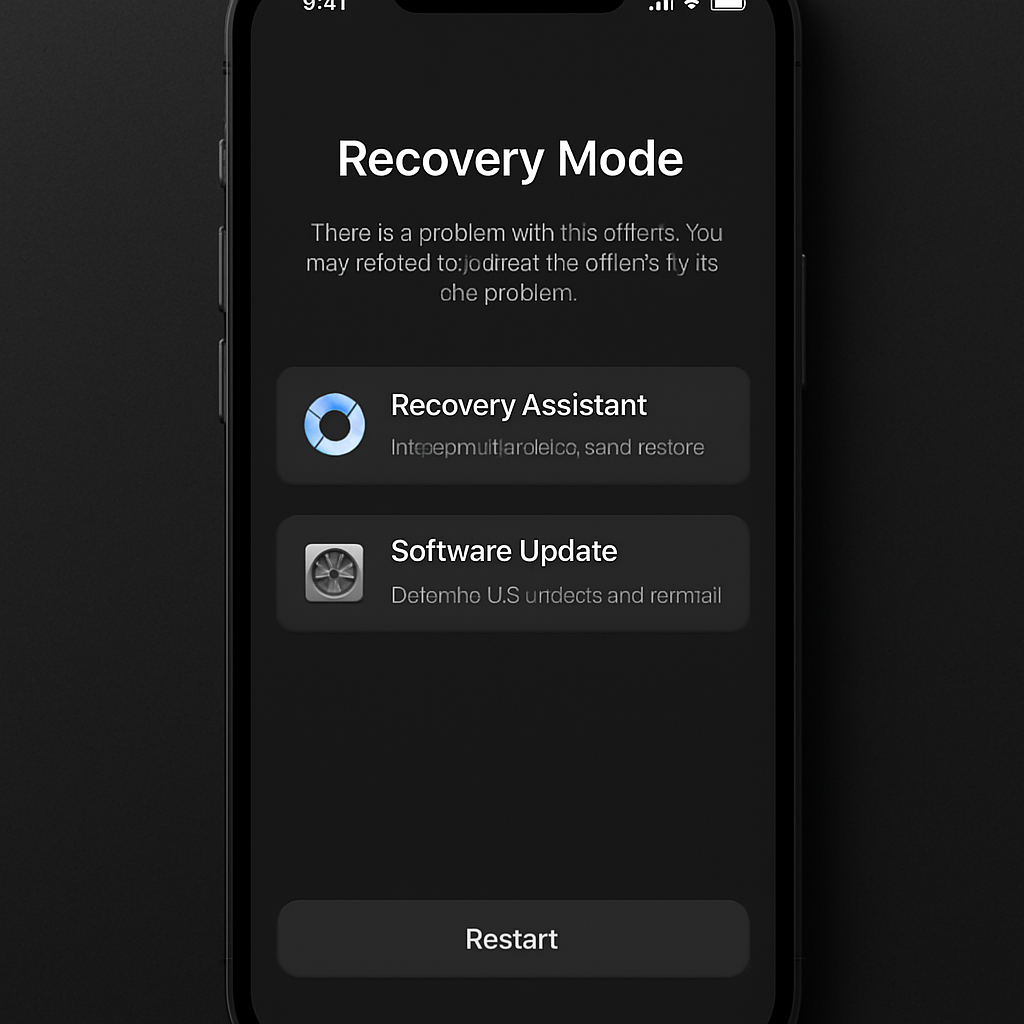
iOS 27 Introduces Mac-Like Recovery Mode for iPhone and iPad
Apple’s latest update, iOS 27, brings a significant enhancement to device recovery by introducing a Mac-like recovery mode for iPhones and iPads. This new feature […]
Apple Details 250 Enhancements in iOS 27 and macOS Golden Gate
Apple has unveiled a comprehensive list of over 250 new features and improvements across its latest software updates, including iOS 27 and macOS Golden Gate, […]
OceanLotus Targets Vietnamese Investors with SPECTRALVIPER Malware
The Vietnam-aligned cyber espionage group known as OceanLotus has been linked to two distinct campaigns targeting domestic entities and stock investors, deploying a backdoor named […]
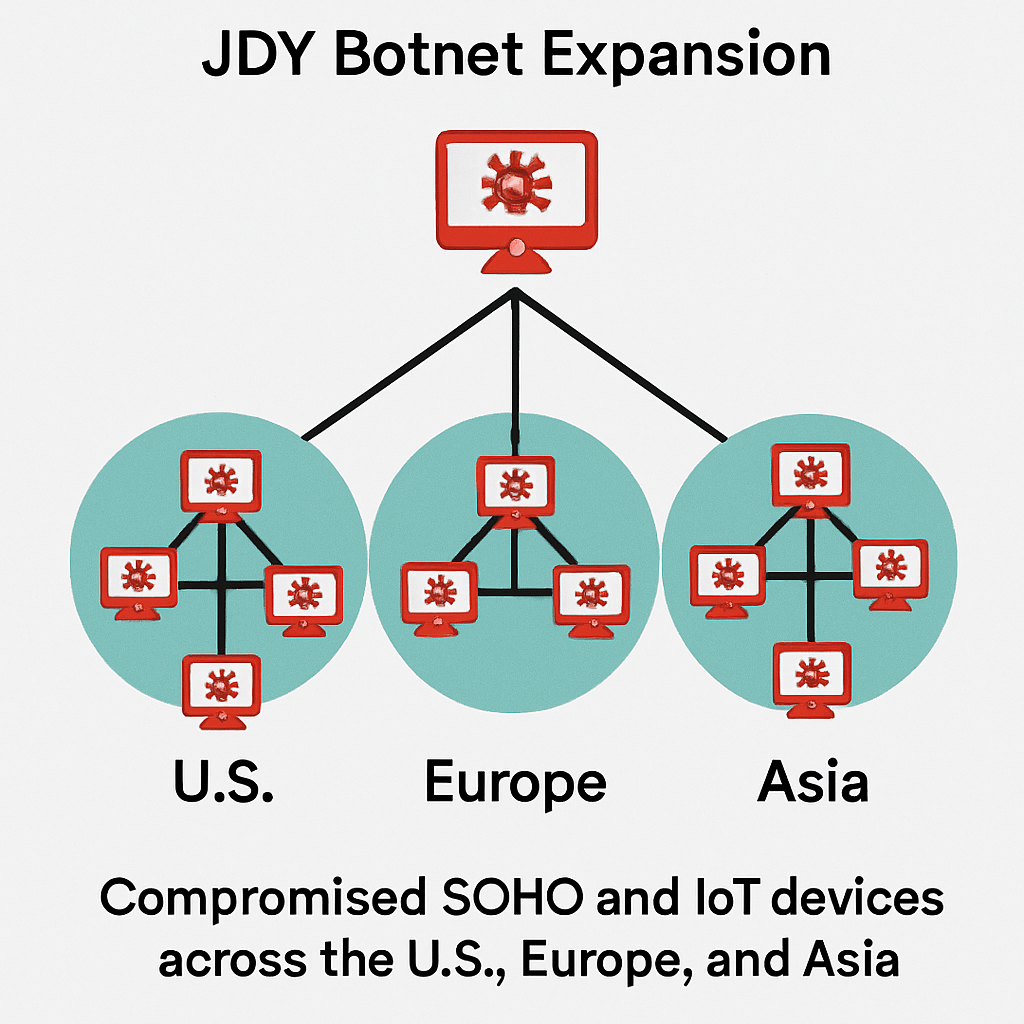
China-Linked JDY Botnet Expands, Targets SOHO and IoT Devices
A China-linked botnet known as JDY has significantly expanded its reach, now controlling over 1,500 small office/home office (SOHO) and Internet of Things (IoT) devices […]
Android 17 QPR1 Beta 4 Introduces ‘Screen Reactions’ Feature
Google’s latest Android 17 QPR1 Beta 4 update brings the ‘Screen Reactions’ feature to Pixel devices, enabling users to record their screen and front-facing camera […]
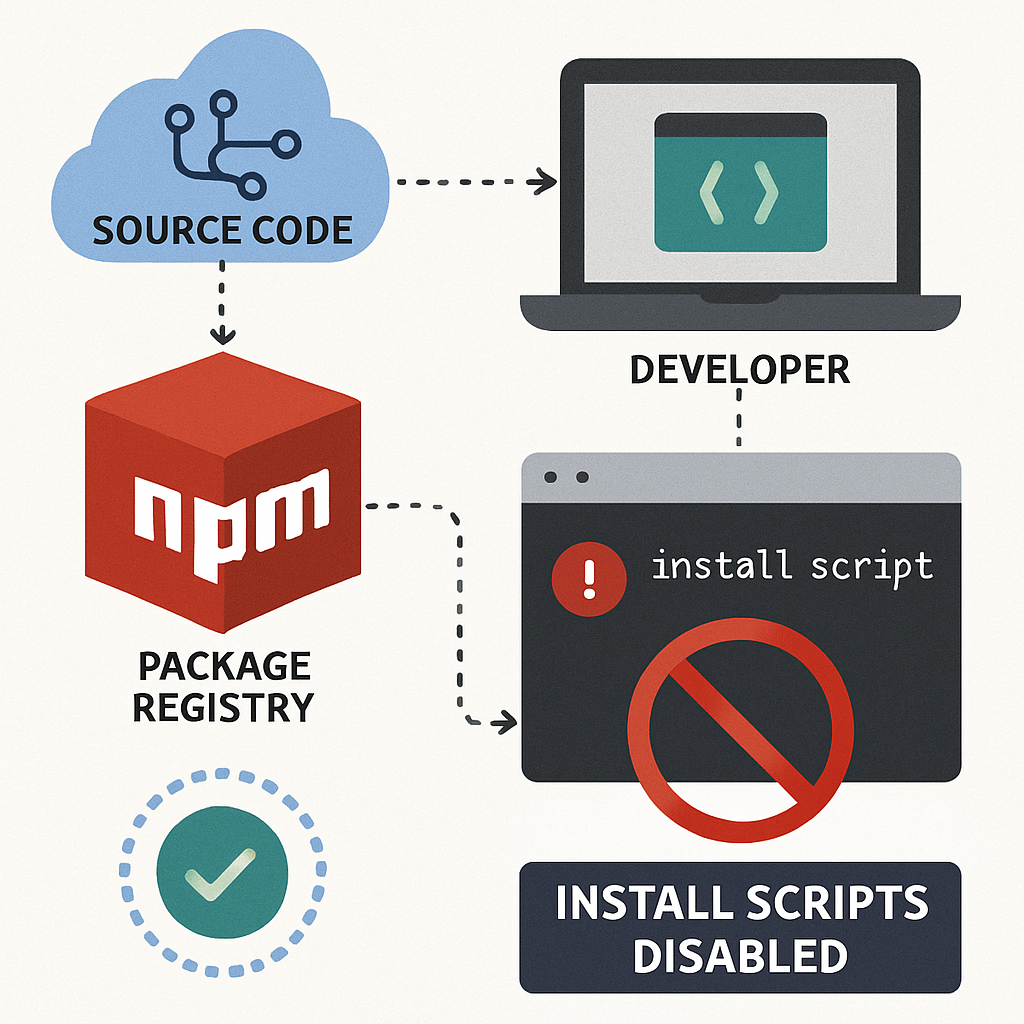
GitHub to Disable npm Install Scripts by Default in Version 12
GitHub has announced significant changes in the upcoming npm version 12, scheduled for release next month, aimed at enhancing software supply chain security. A key […]
Anthropic CEO Dario Amodei’s Unique Management Structure
Anthropic CEO Dario Amodei has adopted an unconventional management approach by having only one direct report—his chief of staff. This structure allows him to concentrate […]
Opendoor’s India Exit Highlights AI’s Impact on Outsourcing
Opendoor, the San Francisco-based online home-buying platform, is closing its India operations less than two years after establishing a presence in the country. CEO Kaz […]