Hackers Exploit Cisco Firepower Devices Using Known Vulnerabilities to Deploy Advanced Backdoor
State-sponsored cyber actors are actively targeting Cisco Firepower devices by exploiting known vulnerabilities to install a sophisticated backdoor, granting them unauthorized remote access to compromised networks.
Cisco’s security research team, Talos, has identified that the espionage-focused group UAT-4356 is leveraging two specific vulnerabilities, CVE-2025-20333 and CVE-2025-20362, to infiltrate Firepower Extensible Operating System (FXOS) environments. This group previously orchestrated the ArcaneDoor campaign, which successfully targeted network perimeter devices for widespread espionage activities.
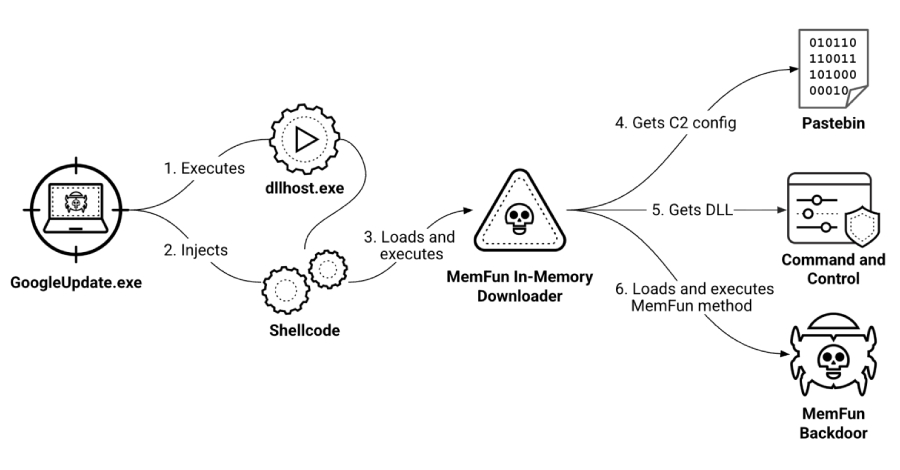
In this latest campaign, the attackers utilize their initial access to deploy FIRESTARTER, an advanced implant that embeds itself deep within the core components of Cisco’s Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) appliances. FIRESTARTER specifically targets the LINA process, allowing attackers to execute arbitrary shellcode directly in the device’s memory.
Malicious Payload Execution
To establish a persistent foothold, UAT-4356 manipulates the device’s boot sequence by altering the Cisco Service Platform mount list. Notably, this persistence mechanism is entirely transient and activates only during a graceful reboot.
When the device processes a standard termination signal, FIRESTARTER copies itself to a backup log file and updates the mount list to ensure re-execution. Upon restarting, the malicious payload cleans up its tracks by restoring the original mount list and deleting temporary files.
Due to the malware’s reliance on runlevel states, administrators can completely eradicate the implant by performing a hard reboot, such as physically disconnecting the hardware from its power source.
During the infection phase, FIRESTARTER meticulously scans the LINA process’s memory for specific byte markers and an executable memory range associated with the shared library framework. After locating the appropriate environment, the malware copies its secondary shellcode into memory and overwrites a legitimate internal data structure.
This process successfully replaces a standard WebVPN XML handler function with the attacker’s malicious routine. FIRESTARTER then actively intercepts incoming WebVPN requests. If an incoming request matches a specific custom prefix, the malware immediately executes the attached shellcode. If the data lacks the required prefix, FIRESTARTER quietly forwards the request to the original handler to evade suspicion.
Analysts note that this sophisticated loading mechanism shares substantial technical overlap with RayInitiator’s deployment tactics.
Detection and Mitigation
Security teams are advised to proactively hunt for FIRESTARTER infections to prevent further espionage activity. Cisco Talos Intelligence recommends the following steps to secure infrastructure:
– Search for the malicious background process or the temporary core log file hiding on the disk.
– Reimage all affected devices to definitively clear the FIRESTARTER infection from the system architecture.
– Terminate the compromised process and reload the system on FTD software operating outside of lockdown mode.
– Apply critical software upgrades as recommended in Cisco’s Security Advisory and CISA Emergency Directive 25-03.
– Deploy Snort rules 65340 and 46897 to detect vulnerability exploitation, and rule 62949 to flag backdoor activity.
By implementing these measures, organizations can enhance their defenses against this sophisticated threat and protect their networks from unauthorized access.