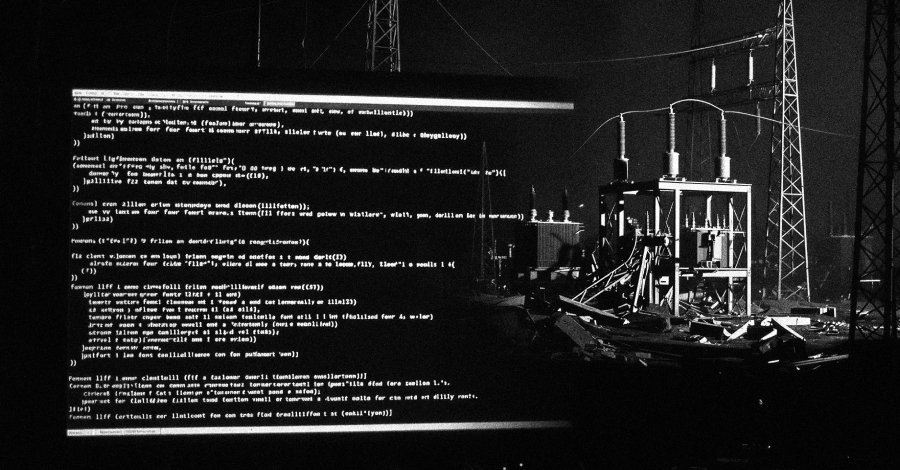
Lotus Wiper Malware Devastates Venezuelan Energy Infrastructure
In a significant cybersecurity incident, researchers have identified a new data-wiping malware, named Lotus Wiper, which has been actively targeting Venezuela’s energy and utilities sector. This malicious software was deployed in a series of attacks from late 2025 into early 2026, causing substantial operational disruptions.
Kaspersky, a leading cybersecurity firm, uncovered that the attack sequence is initiated by two batch scripts. These scripts are designed to weaken system defenses and disrupt normal operations, setting the stage for the final wiper payload. They coordinate the attack across the network, ensuring maximum impact before retrieving and executing the previously unknown wiper.
Once activated, Lotus Wiper systematically erases recovery mechanisms, overwrites physical drive contents, and deletes files across all affected volumes. This comprehensive destruction renders the infected systems completely inoperable. Notably, the malware does not include any ransom demands or payment instructions, indicating that financial gain is not the motive behind these attacks.
The malware was first uploaded to a public platform in mid-December 2025 from a machine in Venezuela. This occurred just weeks before the U.S. military intervention in the country in early January 2026. While a direct connection between these events remains unconfirmed, Kaspersky highlighted that the malware’s appearance coincided with increased reports of cyber activities targeting the same sector and region, suggesting a highly targeted campaign.
The attack begins with a batch script that initiates a multi-stage process to deploy the wiper payload. It attempts to disable the Windows Interactive Services Detection (UI0Detect) service, which alerts users when background services display interactive dialogs. The presence of this setting indicates that the script is designed for systems running versions of Windows prior to 10 version 1803, which no longer include this feature.
The script then checks for a NETLOGON share and accesses a remote XML file. It also verifies the existence of a corresponding local file in directories like C:\lotus or %SystemDrive%\lotus. Regardless of the local file’s presence, the script proceeds to execute a second batch script.
Kaspersky noted that this local check likely determines if the machine is part of an Active Directory domain. If the remote file is unavailable, the script exits. In cases where the NETLOGON share is initially unreachable, the script introduces a randomized delay of up to 20 minutes before retrying the remote check.
The second batch script, if not previously executed, performs several actions:
– Enumerates local user accounts.
– Disables cached logins.
– Logs off active sessions.
– Deactivates network interfaces.
– Executes the diskpart clean all command to wipe all identified logical drives.
Additionally, it uses the robocopy command-line utility to recursively mirror folders, overwriting existing contents or deleting them. It calculates available free space and employs fsutil to create a file that fills the entire drive, exhausting storage capacity and hindering recovery efforts.
After preparing the environment for destruction, Lotus Wiper is launched to:
– Delete restore points.
– Overwrite physical sectors by writing all zeroes.
– Clear the update sequence numbers (USN) of the volumes’ journals.
– Erase all system files across each mounted volume.
Organizations, especially those in critical infrastructure sectors, are advised to monitor for changes in NETLOGON shares, potential credential dumping or privilege escalation activities, and the use of native Windows utilities like fsutil, robocopy, and diskpart, which can be exploited for destructive actions.
Kaspersky emphasized that the malware’s functionalities targeting older Windows versions suggest that the attackers had prior knowledge of the environment and had compromised the domain long before the attack occurred.