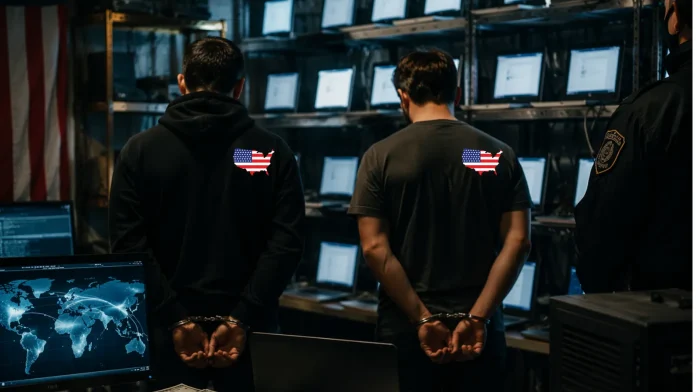
U.S. Nationals Sentenced for Operating Laptop Farm Supporting DPRK Cyber Operations
In a significant legal development, two American citizens have been sentenced to federal prison for orchestrating a complex laptop farm scheme that infiltrated over 100 U.S. companies. This operation funneled more than $5 million to the Democratic People’s Republic of Korea (DPRK), directly supporting its weapons programs.
Sentencing Details
– Kejia Wang, 42, received a 108-month prison sentence.
– Zhenxing Wang, 39, was sentenced to 92 months.
Both individuals pleaded guilty to conspiracy charges, including wire fraud, money laundering, and identity theft.
Operational Tactics
Between 2021 and October 2024, the Wangs managed physical locations within the United States to host company-issued laptops. This setup masked the true overseas locations of North Korean IT workers, enabling them to secure remote positions within major American corporations, including several Fortune 500 companies.
Identity Theft and Financial Laundering
The scheme involved the theft of identities from over 80 U.S. citizens to obtain remote IT roles. To legitimize the illicit earnings, the Wangs established shell companies such as Hopana Tech LLC and Independent Lab LLC. These entities had no actual employees but served as conduits to launder millions of dollars to overseas collaborators. The U.S.-based operators retained nearly $700,000 for their facilitation efforts.
National Security Implications
Beyond financial fraud, this operation posed severe risks to U.S. national security. Unauthorized remote access granted North Korean operatives entry into sensitive employer networks and proprietary source code repositories. Notably, in early 2024, overseas actors breached a California-based defense contractor, exfiltrating artificial intelligence technical data controlled under the International Traffic in Arms Regulations (ITAR).
Technical Exploitation
The perpetrators utilized Keyboard-Video-Mouse (KVM) switches to connect victim companies’ laptops, enabling overseas workers to remotely access the devices while appearing to log in from U.S. residential IP addresses. This method facilitated the theft of critical data and proprietary information.
Law Enforcement Response
This sentencing marks a significant milestone in the Department of Justice’s DPRK RevGen: Domestic Enabler Initiative. Federal agents conducted raids across multiple states, seizing numerous laptops, remote access devices, and web domains linked to the shell companies. Concurrently, the U.S. Department of State announced a $5 million reward for information leading to the disruption of eight additional fugitive co-conspirators involved in the financial mechanisms supporting this DPRK scheme.
Preventative Measures
The FBI and Homeland Security Investigations emphasize the importance of vigilance against remote worker fraud. Organizations are urged to implement stringent verification processes and monitor for signs of unauthorized access to safeguard against similar infiltrations.