A newly identified Remote Access Trojan (RAT) toolkit, dubbed SpankRAT, is being utilized by cybercriminals to exploit legitimate Windows processes, effectively bypassing security controls and maintaining persistent access to compromised systems. This sophisticated malware, developed in the Rust programming language, has demonstrated a remarkable ability to evade detection, with most samples remaining undetected on VirusTotal at the time of analysis.
The SpankLoader: Initial Stage of the Attack
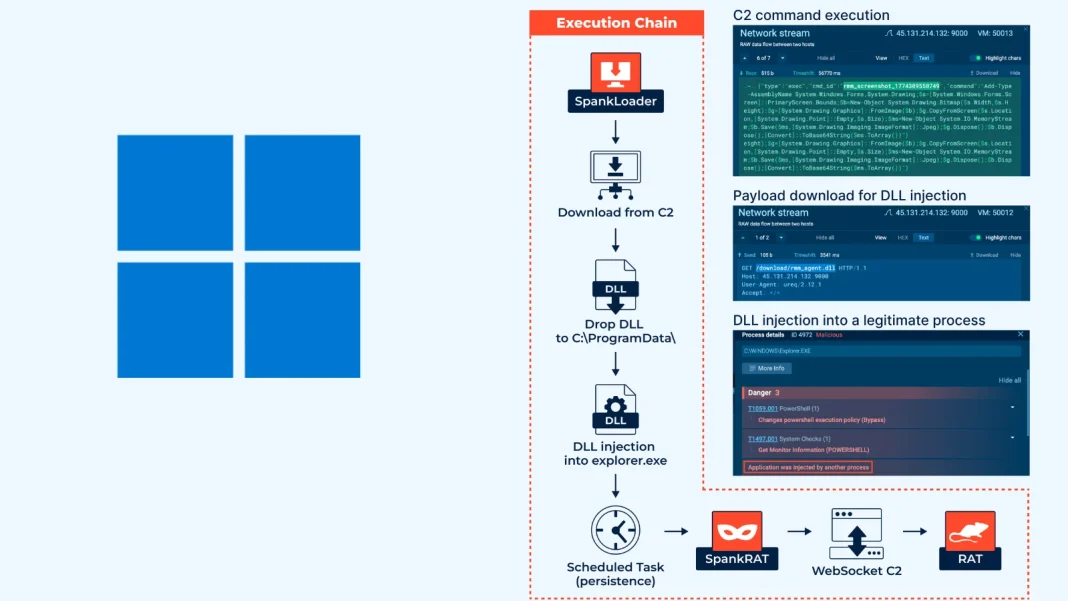
The attack sequence commences with SpankLoader, a lightweight loader designed to fetch the primary payload from a command-and-control (C2) server over unencrypted HTTP. Upon execution, SpankLoader escalates its privileges using the `SeDebugPrivilege` function and deposits a malicious DLL (`rmm_agent.dll`) into the `C:\ProgramData\` directory. Subsequently, it injects this DLL into the legitimate `explorer.exe` process through classic DLL injection techniques.
To ensure persistence across system reboots, SpankLoader establishes a Scheduled Task named `RmmAgentCore`, configured to trigger at logon with the highest privilege execution. This method of injecting into `explorer.exe` is particularly insidious, as it causes malware-generated network traffic to appear as originating from a trusted Windows process. This effectively masks the malicious activity from traditional endpoint and network detection solutions, complicating the identification and mitigation of the threat.
SpankRAT: Comprehensive Remote Access Capabilities
Once embedded within `explorer.exe`, SpankRAT initiates a WebSocket-based connection to the C2 server (`ws://
The command set encompasses a wide range of operational capabilities:
– Session Management: Handles registration and heartbeat telemetry, including CPU, RAM, disk usage, and system uptime.
– Remote Execution: Executes arbitrary commands, returning standard output and exit codes; can elevate User Account Control (UAC) via `Start-Process -Verb RunAs`.
– File Operations: Lists, reads, uploads, deletes, renames files, and creates directories.
– Process Control: Enumerates running processes (PID, name, memory usage, user, CPU usage); terminates processes.
– Windows Services Management: Lists services; starts, stops, or restarts services.
– Registry Manipulation: Performs full Create, Read, Update, Delete (CRUD) operations—reads keys/values, sets, creates, and deletes registry entries.
– Scheduled Task Control: Lists, runs, and toggles scheduled tasks.
– Software Inventory: Enumerates installed software.
All system interactions are executed through PowerShell using the `-NoProfile -NonInteractive -ExecutionPolicy Bypass` flags. Operating system fingerprinting retrieves the build number and product name directly from the registry, providing attackers with detailed system information.
Evasion Techniques and Detection Challenges
SpankRAT’s ability to route C2 traffic through trusted system processes like `explorer.exe` allows it to evade reputation-based detection controls effectively. Since the malicious network activity appears to originate from legitimate Windows binaries, it is often deprioritized during security operations center (SOC) triage processes. This significantly reduces visibility into the compromise and increases the risk of undetected breaches.
The use of Rust for SpankRAT’s development contributes to its stealth, as Rust’s compilation process can produce binaries that are less recognizable to traditional signature-based detection systems. Additionally, the malware’s modular design and the use of unencrypted HTTP for payload retrieval further complicate detection efforts.
Indicators of Compromise (IOCs)
Security teams should be vigilant for the following indicators across their environments:
– C2 Servers: `45.131.214[.]132:9000` (HTTP)
– Malicious DLL: `rmm_agent.dll` located in `C:\ProgramData\`
– Scheduled Task: `RmmAgentCore` configured with logon trigger and highest privilege execution
– Injected Process: `explorer.exe` exhibiting unusual network activity
Mitigation Strategies
To defend against threats like SpankRAT, organizations should implement a multi-layered security approach:
1. Behavioral Analysis: Utilize advanced behavioral analysis platforms capable of detecting anomalies in process behavior and network traffic.
2. Endpoint Detection and Response (EDR): Deploy EDR solutions that can identify and respond to suspicious activities, such as unauthorized DLL injections and unusual scheduled tasks.
3. Network Monitoring: Monitor network traffic for connections to known malicious IP addresses and unusual patterns indicative of C2 communication.
4. Regular Updates: Keep all systems and software up to date with the latest security patches to mitigate vulnerabilities that could be exploited by malware.
5. User Education: Educate users about the risks of phishing attacks and the importance of not executing unknown or unsolicited files.
Conclusion
The emergence of SpankRAT underscores the evolving sophistication of cyber threats and the necessity for robust, adaptive security measures. By exploiting legitimate Windows processes and employing advanced evasion techniques, SpankRAT presents a significant challenge to traditional detection methods. Organizations must remain vigilant, continuously update their security protocols, and invest in advanced detection and response capabilities to effectively combat such threats.