Cybercriminals Exploit n8n AI Workflow Automation to Distribute Malware via Trusted Webhooks
In a concerning development, cybercriminals have been exploiting the n8n AI workflow automation platform to distribute malware through trusted webhooks, effectively bypassing traditional security measures. This tactic leverages the inherent trust associated with legitimate platforms to deliver malicious payloads directly to victims’ devices.
Exploitation of n8n’s Webhooks
The n8n platform, widely used for automating workflows and integrating various services, offers webhook functionality that allows applications to send real-time data to one another. Attackers have been creating free developer accounts on n8n, which automatically generate subdomains under the `.app.n8n[.]cloud` namespace. These subdomains, being part of a recognized service, are often deemed trustworthy by corporate security gateways. Consequently, emails and web requests originating from these subdomains can evade detection by many security solutions.
Researchers from Cisco Talos, including Sean Gallagher and Omid Mirzaei, identified this abuse of the n8n platform. Their analysis revealed a significant increase in emails containing n8n webhook URLs, with March 2026 seeing approximately 68% more than January 2025. This sharp rise indicates a deliberate and escalating misuse of the platform.
Dual-Purpose Attacks: Malware Delivery and Device Fingerprinting
The attackers’ campaigns serve two primary objectives: delivering malware and fingerprinting targeted devices.
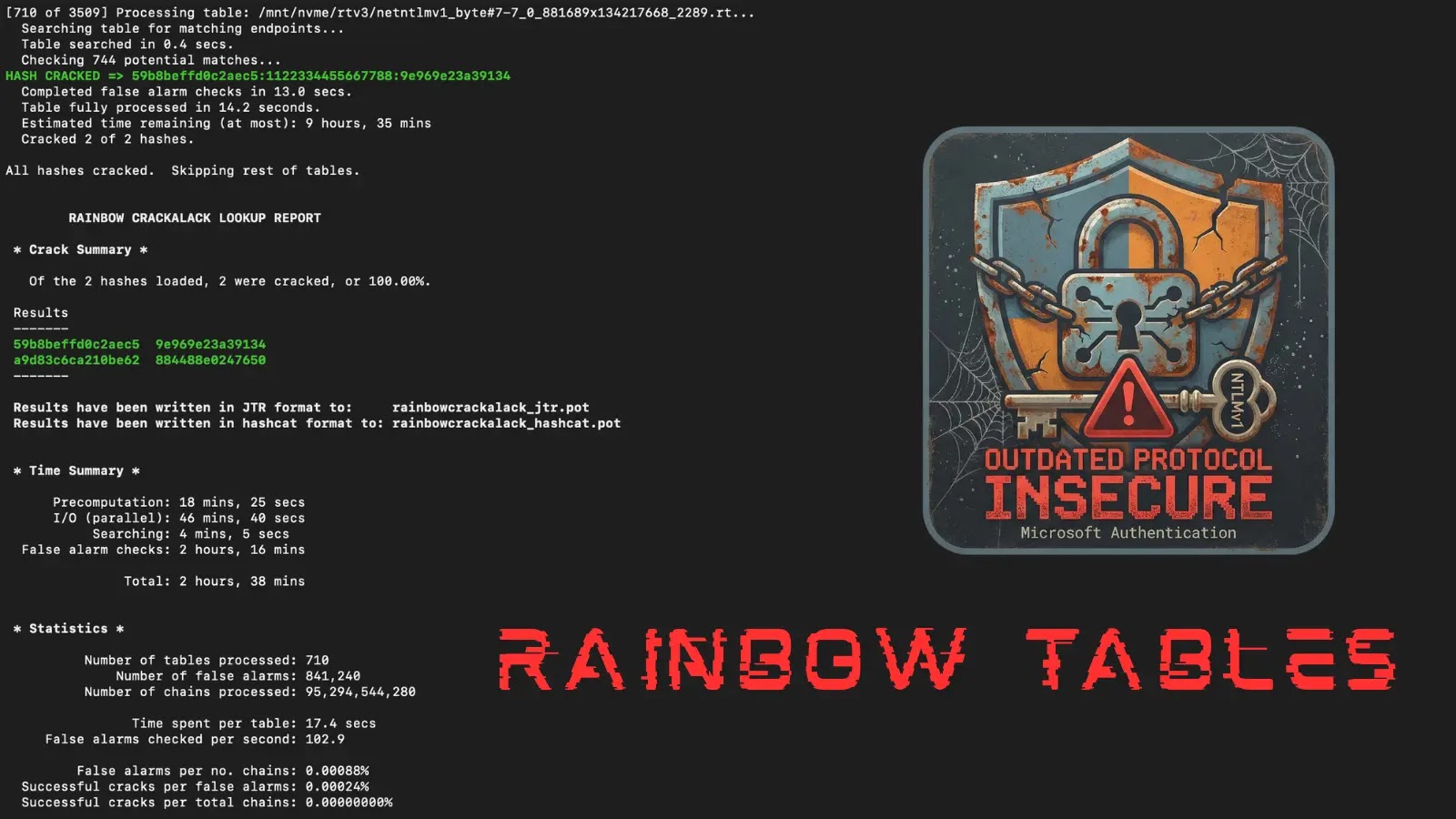
1. Malware Delivery: Phishing emails masquerading as shared Microsoft OneDrive folder notifications contain embedded n8n webhook links. When recipients click these links, they are directed to an HTML page with a CAPTCHA challenge. Upon solving the CAPTCHA, a download button appears, initiating the download of a file named `DownloadedOneDriveDocument.exe`. This file, when executed, installs a modified version of the Datto Remote Monitoring and Management (RMM) tool—a legitimate remote administration application. The malware then uses PowerShell commands to configure Datto RMM as a scheduled task, establishing a persistent connection to a relay on the `centrustage[.]net` domain before deleting itself and the rest of the payload to cover its tracks.
2. Device Fingerprinting: By embedding invisible tracking pixels hosted on n8n webhook URLs within HTML emails, attackers can silently collect device information, such as browser type and IP address, from recipients who merely open the email without clicking any link. This technique allows attackers to gather valuable data on potential targets without raising suspicion.
Broader Implications and Security Concerns
The exploitation of n8n’s webhooks underscores a broader trend where cybercriminals repurpose legitimate platforms to facilitate their malicious activities. By leveraging trusted services, attackers can effectively bypass traditional security filters, making it imperative for organizations to adopt more sophisticated detection mechanisms.
This incident also highlights the importance of scrutinizing even trusted platforms for potential vulnerabilities. As attackers continue to innovate, security professionals must remain vigilant, ensuring that all components of their infrastructure are secure and regularly updated.
Recommendations for Mitigation
To mitigate the risks associated with this exploitation:
– Update and Patch Systems: Ensure that all software, including workflow automation platforms like n8n, are updated to the latest versions to benefit from security patches.
– Monitor for Unusual Activity: Implement monitoring solutions to detect unusual activities, such as unexpected subdomain creations or unrecognized webhook traffic.
– Educate Employees: Conduct regular training sessions to educate employees about phishing tactics and the importance of verifying the authenticity of emails and links.
– Enhance Email Security: Deploy advanced email filtering solutions capable of analyzing the behavior of links and attachments, rather than relying solely on domain reputation.
– Restrict Unnecessary Webhooks: Review and restrict the use of webhooks to only those necessary for business operations, reducing the potential attack surface.
Conclusion
The abuse of n8n’s AI workflow automation platform by cybercriminals to deliver malware through trusted webhooks serves as a stark reminder of the evolving tactics employed by attackers. Organizations must adopt a proactive and comprehensive approach to cybersecurity, ensuring that even trusted platforms are continuously monitored and secured against potential threats.