Russian State-Backed APT28 Exploits SOHO Routers in Global DNS Hijacking Campaign
The Russian state-sponsored cyber espionage group known as APT28, also referred to as Forest Blizzard, has been implicated in a sophisticated campaign targeting Small Office/Home Office (SOHO) routers worldwide. This operation, active since at least May 2025, involved compromising vulnerable MikroTik and TP-Link routers to manipulate their Domain Name System (DNS) settings, effectively transforming them into nodes within a malicious infrastructure under APT28’s control.
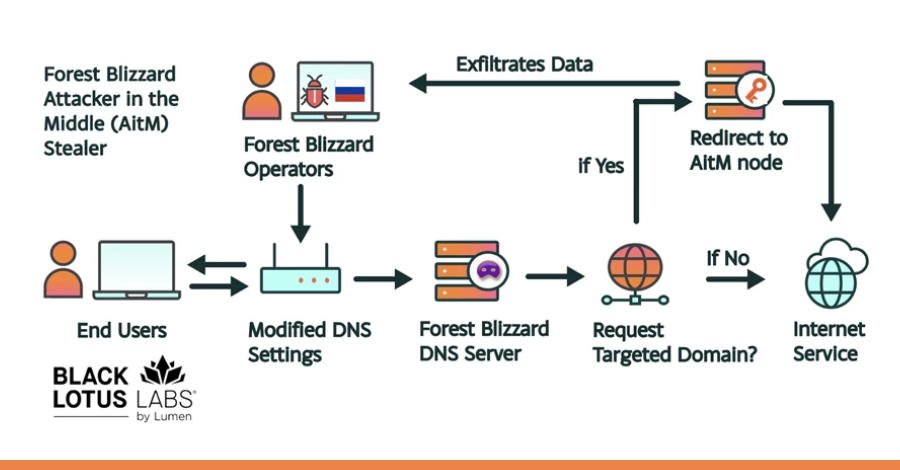
Dubbed FrostArmada by Lumen’s Black Lotus Labs, this large-scale exploitation campaign was characterized by the strategic modification of DNS configurations on compromised routers. By altering these settings, APT28 redirected network traffic through attacker-controlled nodes, enabling the passive collection and exfiltration of sensitive authentication credentials without requiring any direct interaction from end-users.
Microsoft’s Threat Intelligence team corroborated these findings, highlighting that APT28’s activities allowed for the interception of passwords, OAuth tokens, and other critical credentials associated with web and email services. This method of DNS hijacking facilitated adversary-in-the-middle (AitM) attacks, granting the threat actors unauthorized access to confidential information and posing significant risks to the security of affected organizations.
The campaign’s reach was extensive, with over 18,000 unique IP addresses across more than 120 countries communicating with APT28’s infrastructure at its peak in December 2025. The primary targets included government agencies such as ministries of foreign affairs, law enforcement bodies, and third-party email and cloud service providers spanning regions in North Africa, Central America, Southeast Asia, and Europe.
In response to this pervasive threat, a coordinated international effort was launched to dismantle the malicious network. The U.S. Department of Justice (DoJ), in collaboration with the Federal Bureau of Investigation (FBI) and other global partners, initiated Operation Masquerade. This court-authorized technical operation successfully neutralized the U.S. segment of the compromised network, effectively disrupting APT28’s activities and mitigating the immediate threat posed by the hijacked routers.
The DoJ emphasized that the DNS hijacking operation orchestrated by APT28 enabled Russian intelligence agencies to surveil individuals of interest to the Kremlin. This included personnel within military, governmental, and critical infrastructure sectors, underscoring the campaign’s strategic intent to gather intelligence on key figures and organizations.
Microsoft’s analysis further revealed that APT28’s exploitation of SOHO routers marked a significant evolution in their tactics. By compromising edge devices that are often less monitored or managed, the threat actors could pivot into enterprise environments, achieving persistent and passive reconnaissance at scale. This approach not only enhanced their ability to gather intelligence but also demonstrated a sophisticated understanding of network vulnerabilities and the potential for leveraging them to achieve broader objectives.
The FrostArmada campaign highlights the critical importance of securing SOHO routers, which are frequently overlooked in cybersecurity strategies. Organizations and individuals are urged to implement robust security measures, including regular firmware updates, strong authentication protocols, and continuous monitoring of network configurations, to defend against such sophisticated threats.
In conclusion, the APT28-led DNS hijacking campaign represents a significant escalation in state-sponsored cyber espionage activities. The successful international collaboration to disrupt this operation underscores the necessity for vigilance and proactive defense strategies in the face of evolving cyber threats.