Covert Eavesdropping: Transforming Fiber Optic Cables into Hidden Microphones
In a groundbreaking revelation, security researchers have demonstrated a method to convert standard Fiber-to-the-Home (FTTH) telecom fiber optic cables into covert listening devices, capable of capturing private conversations without detection. This discovery challenges the long-held belief that fiber optic communications are inherently secure and immune to external eavesdropping.
The Research Breakthrough
A collaborative team from The Hong Kong Polytechnic University, The Chinese University of Hong Kong, and the Technological and Higher Education Institute of Hong Kong presented their findings at the Network and Distributed System Security (NDSS) Symposium 2026 in San Diego, California. Their study, titled Hiding an Ear in Plain Sight: On the Practicality and Implications of Acoustic Eavesdropping with Telecom Fiber Optic Cables, unveils a side-channel attack that exploits the physical properties of fiber optic cables to intercept audio signals.
Exploiting Acoustic Sensitivity
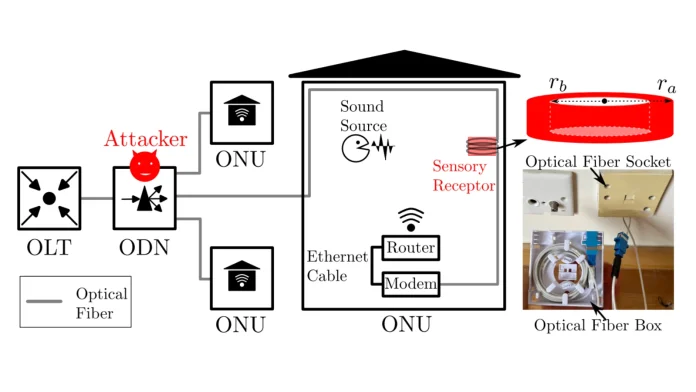
Fiber optic cables, traditionally valued for their resistance to electromagnetic interference and RF emissions, are susceptible to acoustic vibrations. When exposed to sound waves, these cables undergo minute structural deformations, leading to measurable phase shifts in the transmitted laser light. By employing a Distributed Acoustic Sensing (DAS) system connected to one end of the fiber, an attacker can detect these phase shifts and reconstruct the original sound waves from the opposite end, even over distances exceeding 50 meters.
Enhancing Sound Capture with Sensory Receptors
To amplify the cable’s sensitivity to airborne speech, the researchers developed a Sensory Receptor—a hollow PET (polyethylene terephthalate) cylinder, 65mm in diameter, with 15 meters of optical fiber tightly wound around it. This configuration enhances the cable’s responsiveness to acoustic pressure fluctuations, converting them into longitudinal strain along the fiber and significantly improving sound capture capabilities. Notably, this device can be disguised as a standard optical fiber box, commonly installed in homes and offices during FTTH deployments, making it virtually indistinguishable from legitimate networking equipment.
Real-World Implications and Experimental Results
The attack necessitates physical access to both the victim’s premises (Optical Network Unit, ONU) and the Optical Distribution Network (ODN). Such access is plausible during routine FTTH installations, upgrades, or maintenance, where technicians or subcontractors might handle fiber endpoints. In controlled experiments, the researchers achieved remarkable results:
– Speech Recovery: At a distance of 2 meters, the system achieved a Word Error Rate (WER) below 20%, meaning over 80% of spoken content was accurately transcribed using AI speech recognition models like OpenAI Whisper and NVIDIA Parakeet.
– Speaker Localization: The system pinpointed a speaker’s position within a room with an average accuracy of 77 centimeters.
– Sound Event Detection: Activities such as typing, coughing, or alarms were identified with 83% accuracy after fine-tuning deep learning models on the recovered audio.
– Office Scenario: In a real office setting spanning two rooms separated by over 50 meters of fiber cable, optimal placement (e.g., a fiber box under a desk) yielded a mean WER of just 9%, resulting in near-perfect transcription.
Challenges in Detection and Countermeasures
Unlike traditional hidden microphones, fiber optic sensors operate without electricity and emit no RF signatures, rendering them invisible to standard Technical Surveillance Countermeasures (TSCM) sweeps or RF bug detectors. Alarmingly, commercial ultrasonic jammers, commonly used to disrupt covert microphones, proved ineffective against this fiber-based eavesdropping method.
Broader Context and Related Vulnerabilities
This discovery adds to a growing list of vulnerabilities in communication infrastructures. For instance, the Crimson Collective threat group recently claimed responsibility for breaching Brightspeed, a major fiber broadband provider, compromising sensitive customer and employee data. Such incidents underscore the critical need for enhanced security measures in fiber optic networks.
Mitigation Strategies
To counteract this novel eavesdropping technique, the following measures are recommended:
1. Physical Security: Implement strict access controls to prevent unauthorized physical access to fiber optic infrastructure.
2. Tamper Detection: Deploy tamper-evident seals and monitoring systems on fiber optic enclosures to detect unauthorized modifications.
3. Acoustic Isolation: Design and install fiber optic cables in a manner that minimizes exposure to ambient sound vibrations.
4. Regular Inspections: Conduct routine inspections of fiber optic installations to identify and address potential security vulnerabilities.
Conclusion
The ability to transform fiber optic cables into covert microphones represents a significant advancement in surveillance techniques, challenging existing security paradigms. As fiber optic networks continue to proliferate, it is imperative to develop and implement robust security measures to safeguard against such sophisticated eavesdropping methods.