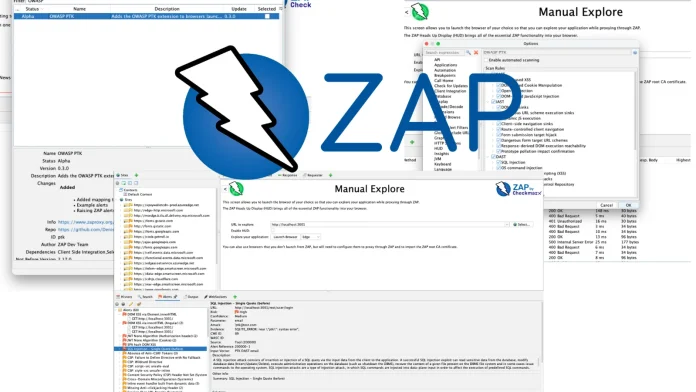
Enhancing Web Application Security: ZAP’s OWASP PTK Add-On Integrates Browser-Based Findings into Native Alerts
The Zed Attack Proxy (ZAP) team has unveiled version 0.3.0 of the OWASP PenTest Kit (PTK) add-on, marking a significant advancement in web application security testing. This latest release bridges the gap between traditional proxy-level scanning and modern client-side execution by mapping in-browser security findings directly into native ZAP alerts.
Addressing the Limitations of Traditional Proxy-Level Scanning
Historically, ZAP has excelled at monitoring traffic at the proxy layer, analyzing requests, responses, and server-side behaviors. However, the evolution of web applications has introduced security risks that occur entirely within the browser’s runtime environment, beyond the reach of traditional proxy monitoring. These include Single Page Application (SPA) routing, Document Object Model (DOM) updates, client-side rendering decisions, and potentially hazardous JavaScript patterns.
Bridging the Gap with OWASP PTK Add-On
The OWASP PTK add-on addresses these challenges by transforming the browser into an active security testing platform. While previous versions automatically pre-installed the PTK extension into ZAP-launched browsers such as Chrome, Firefox, and Edge, version 0.3.0 introduces a crucial communication loop. Now, PTK can report its client-side findings back to ZAP as native alerts, enabling security professionals to conduct scans within the actual browser context and review all results within ZAP’s centralized interface.
Customizable Rule Selection for Comprehensive Scanning
The new update introduces customizable rule selection for three core scanning engines, each targeting different aspects of client-side risk:
1. Interactive Application Security Testing (IAST): This engine monitors runtime signals during real user interactions, detecting issues often invisible to a proxy, such as DOM-based Cross-Site Scripting (XSS) and risky data flows where tainted input reaches sensitive operations without triggering a server response.
2. Static Application Security Testing (SAST): PTK SAST analyzes the actual JavaScript loaded by the browser, including minified production bundles and external third-party scripts. It identifies dangerous sinks like `eval` or unsafe `innerHTML` and DOM injection patterns that do not appear in standard HTTP traffic.
3. Dynamic Application Security Testing (DAST): The DAST engine focuses on browser-driven runtime request mutation, offering real behavior testing within the exact authenticated session the user is operating.
Integration of Findings into ZAP Alerts
This integration represents a significant leap in vulnerability detection capabilities. ZAP now features 142 new OWASP PTK-tagged alert types. Since these findings appear as standard ZAP alerts, security teams can leverage existing triage workflows, including severity filtering, false-positive marking, and comprehensive report generation.
Streamlined Testing Workflow
To utilize the new capabilities, users can install or update the OWASP PTK add-on via the ZAP Marketplace. After configuring the desired scan rules in ZAP’s options, testers can launch a browser directly to their target application. The update also features a new auto-start option; when enabled, PTK scanning initiates automatically when the browser opens.
As testers navigate the application and perform realistic workflows—such as logging in, adding items to a cart, or submitting forms—the PTK extension silently analyzes the client-side code and streams identified vulnerabilities directly to the ZAP Alerts tab. This integration is the first step toward a fully automated, continuous integration-style scanning pipeline.
Future Developments and Community Engagement
Future updates to OWASP ZAP will enable auto-launching browsers, running scripted journeys, and integrating with headless browser environments, further enhancing automated security testing capabilities. The ZAP team encourages the security community to explore the new PTK add-on, provide feedback, and contribute to its ongoing development.
Conclusion
The release of the OWASP PTK add-on version 0.3.0 signifies a pivotal advancement in web application security testing. By integrating browser-based security findings into native ZAP alerts, this update empowers security professionals to detect and address client-side vulnerabilities more effectively, ensuring comprehensive protection for modern web applications.