Magecart Hackers Exploit Over 100 Domains to Hijack eStore Checkouts and Steal Payment Data
A sophisticated and prolonged Magecart campaign has been actively compromising e-commerce websites across at least 12 countries over the past two years. Utilizing more than 100 malicious domains, this operation aims to steal payment card data in real-time, with banks and cardholders bearing the brunt of the financial impact.
Discovery and Scope
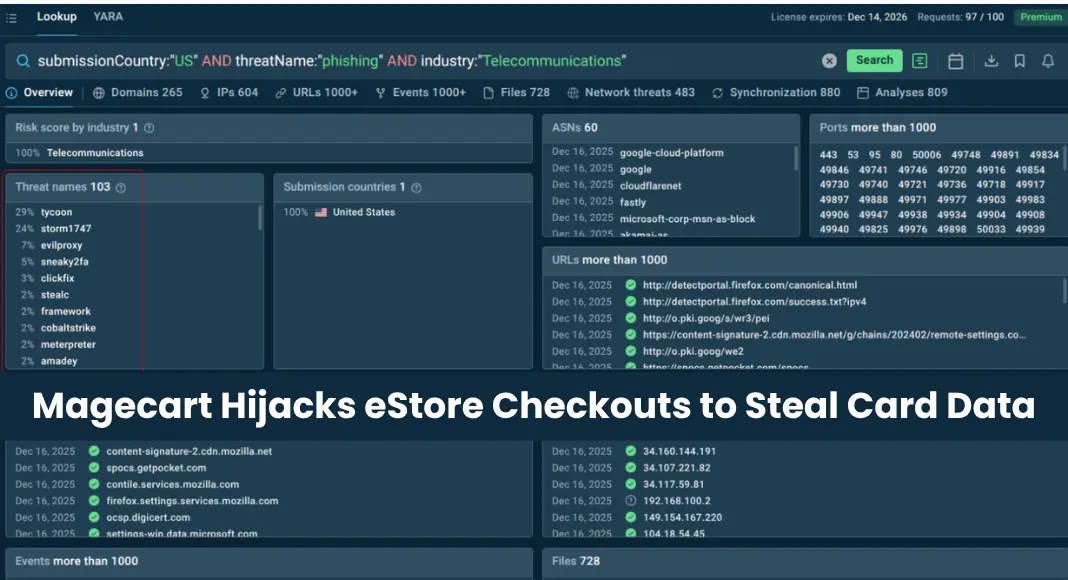
Security researchers at ANY.RUN have uncovered this extensive Magecart operation, which has been operational since early 2024. Between February 2024 and April 2025, the campaign infected 17 confirmed WooCommerce websites. The infrastructure supporting this operation spans over 100 domains, indicating a level of investment and planning characteristic of organized cybercrime rather than opportunistic skimming.
Victims have been identified in countries including the United Kingdom, Denmark, France, Spain, and the United States. A significant concentration of attacks in Spain is linked to the campaign’s exploitation of the Redsys payment ecosystem.
Financial Impact
While e-commerce merchants are the initial targets, the primary financial burden falls on banks and cardholders. Stolen card data fuels downstream fraud losses and undermines consumer trust in digital payment systems, creating ongoing challenges for financial institutions even after the skimmer is removed.
Attack Methodology
The attackers employ a multi-stage infection chain designed to evade detection and removal:
1. Initial Compromise: After infiltrating a WooCommerce site, attackers inject a small, obfuscated JavaScript loader into an existing script file.
2. Dynamic Payload Retrieval: This loader, devoid of card-stealing logic, contacts external infrastructure to fetch a JSON configuration payload (encoded as numeric character arrays) and subsequently retrieves the next malicious stage dynamically.
3. Resilience Mechanism: The loader includes a fallback mechanism; if one staging domain is unreachable or blocked, it cycles through a list of backup domains until it receives a valid response. This design ensures the campaign’s continuity even when individual components are taken down, contributing to its prolonged undetected operation.
4. Second-Stage Payload Delivery: Delivered from domains crafted to resemble legitimate web services—such as fake jQuery libraries, CDN resources, and analytics platforms—the second-stage payload waits for the checkout page to appear. It then hijacks the payment interface by replacing or overlaying the legitimate payment form with a convincing fake.
Impersonation Techniques
A key tactic of this campaign is the high-fidelity impersonation of trusted payment service providers. One variant closely mimics Redsys, a widely used payment processor in Spain, incorporating the legitimate Redsys domain `sis.redsys.es` into the attack flow to enhance credibility. PayPlug SAS interfaces have also been replicated. The fake payment UI supports multiple languages—including English, Spanish, Arabic, and French—indicating a deliberate, globally oriented targeting strategy.
Data Exfiltration
Once victims enter their card details into the spoofed form, the payload transmits the data—including BIN, full card number, expiration date, and CVV—not via a standard HTTP POST request, but through an encrypted WebSocket connection. This method adds an extra layer of obfuscation, making detection and interception more challenging.
Recommendations for Mitigation
To protect against such sophisticated attacks, e-commerce businesses and financial institutions should consider the following measures:
– Regular Security Audits: Conduct comprehensive security assessments to identify and remediate vulnerabilities in web applications and server configurations.
– Implement Content Security Policy (CSP): Deploy CSP headers to restrict the sources from which scripts can be loaded, thereby preventing unauthorized script execution.
– Monitor for Anomalous Activity: Utilize intrusion detection systems (IDS) and web application firewalls (WAF) to detect and block suspicious activities in real-time.
– Educate Staff and Users: Provide training on recognizing phishing attempts and the importance of verifying the authenticity of payment interfaces.
– Keep Software Updated: Ensure that all software components, including plugins and third-party integrations, are regularly updated to patch known vulnerabilities.
By implementing these strategies, organizations can enhance their defenses against Magecart and similar cyber threats, safeguarding both their operations and their customers’ sensitive information.