Cybercriminals Exploit Tax Season with Sophisticated IRS Impersonation Scams
As the tax filing deadline approaches, cybercriminals are intensifying their efforts to exploit taxpayers through sophisticated phishing campaigns. These malicious actors impersonate the Internal Revenue Service (IRS), national tax authorities, and corporate human resources departments to deceive individuals into installing malware or divulging sensitive information. In 2026 alone, over a hundred such campaigns have been identified, delivering a range of threats from credential-stealing pages to remote access tools.
Diverse Tactics and Targets
The methods employed by these cybercriminals are varied and increasingly sophisticated. They send emails about expired tax documents, IRS filing notices, and W-2 form requests from fake HR teams. Some campaigns even target non-U.S. taxpayers with fraudulent W-8BEN filings. These attacks are not limited to the United States; individuals in Canada, Australia, Switzerland, and Japan have also been targeted. Email volumes range from a few targeted messages to tens of thousands, indicating the scale and reach of these operations.
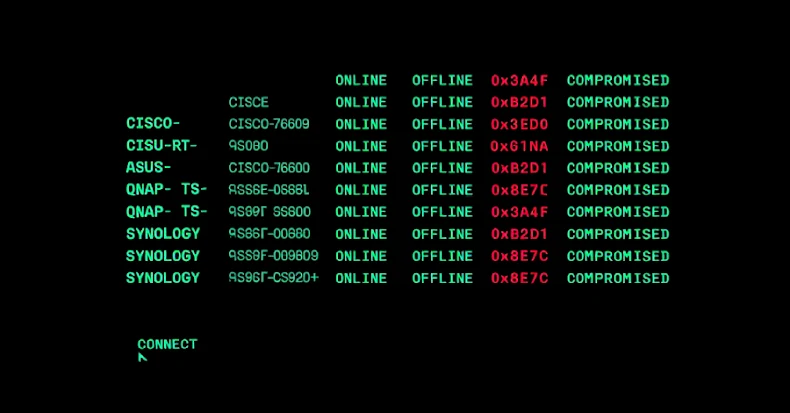
Abuse of Remote Monitoring and Management (RMM) Tools
A notable trend in these campaigns is the abuse of legitimate Remote Monitoring and Management (RMM) software. Tools such as N-able, Datto, RemotePC, Zoho Assist, and ScreenConnect are exploited due to their trusted status and digital signatures, making them difficult to detect as threats. For instance, on February 5, a campaign impersonating the IRS sent emails with a fake Transcript Viewer button, linking to a Bitbucket-hosted executable that silently installed N-able RMM on the victim’s machine. The inclusion of a real IRS phone number in the email added a layer of credibility to the scam.
Organized Threat Actor Groups
Security researchers have identified specific threat actor groups orchestrating these campaigns. TA4922, believed to be based in East Asia, employs a multi-stage attack chain to gain remote access to victims’ systems. Another group, TA2730, has been running credential phishing campaigns since June 2025, impersonating investment firms and requesting targets to update W-8BEN tax forms. In February 2026, TA2730 impersonated Swissquote in Switzerland and Questrade in Canada, directing victims to fake login pages designed to steal account credentials for financial gain.
Protective Measures for Taxpayers
To safeguard against these sophisticated scams, taxpayers are advised to:
1. Verify Communications: The IRS does not initiate contact via email or text messages regarding tax issues. Any unexpected communication claiming to be from the IRS should be treated with caution.
2. Avoid Clicking Suspicious Links: Do not click on links or download attachments from unsolicited emails. Instead, visit the official IRS website by typing the URL directly into your browser.
3. Use Multi-Factor Authentication (MFA): Enable MFA on all financial and tax-related accounts to add an extra layer of security.
4. Monitor Financial Accounts: Regularly check bank statements and credit reports for unauthorized activities.
5. Report Suspicious Activities: Forward phishing emails to [email protected] and report any monetary losses to the Treasury Inspector General for Tax Administration and the Federal Trade Commission.
Conclusion
As cybercriminals continue to refine their tactics, it is imperative for taxpayers to remain vigilant and proactive in protecting their personal and financial information. By staying informed about the latest scams and implementing robust security measures, individuals can significantly reduce the risk of falling victim to these malicious campaigns.