DeepLoad Malware Exploits ClickFix and WMI for Stealthy Infections
In the ever-evolving landscape of cyber threats, a new malware strain named DeepLoad has emerged, employing sophisticated techniques to infiltrate systems undetected. This malware leverages the deceptive ClickFix method alongside Windows Management Instrumentation (WMI) to execute malicious payloads directly in memory, thereby evading traditional security measures.
Understanding ClickFix: A Deceptive Entry Point
ClickFix is a social engineering tactic that deceives users into executing malicious commands under the guise of resolving non-existent issues. Typically, victims encounter fake error messages or CAPTCHA verifications prompting them to copy and paste commands into their system’s Run dialog. This method has been increasingly adopted by various malware campaigns due to its effectiveness in bypassing initial access defenses.
DeepLoad’s Exploitation of ClickFix
DeepLoad capitalizes on the ClickFix technique by presenting users with deceptive prompts that instruct them to execute commands purportedly to fix system errors. Once the user complies, the malware initiates its infection chain, leading to the deployment of its payload. This approach not only facilitates initial access but also reduces reliance on traditional methods like phishing emails or exploiting known vulnerabilities.
Leveraging WMI for Stealthy Execution
Beyond the initial access, DeepLoad employs Windows Management Instrumentation (WMI) to execute its payloads directly in memory. WMI is a powerful Windows feature that allows for the management of system components and is often exploited by malware for its ability to execute commands without leaving traces on the disk. By utilizing WMI, DeepLoad minimizes its footprint, making detection and analysis significantly more challenging.
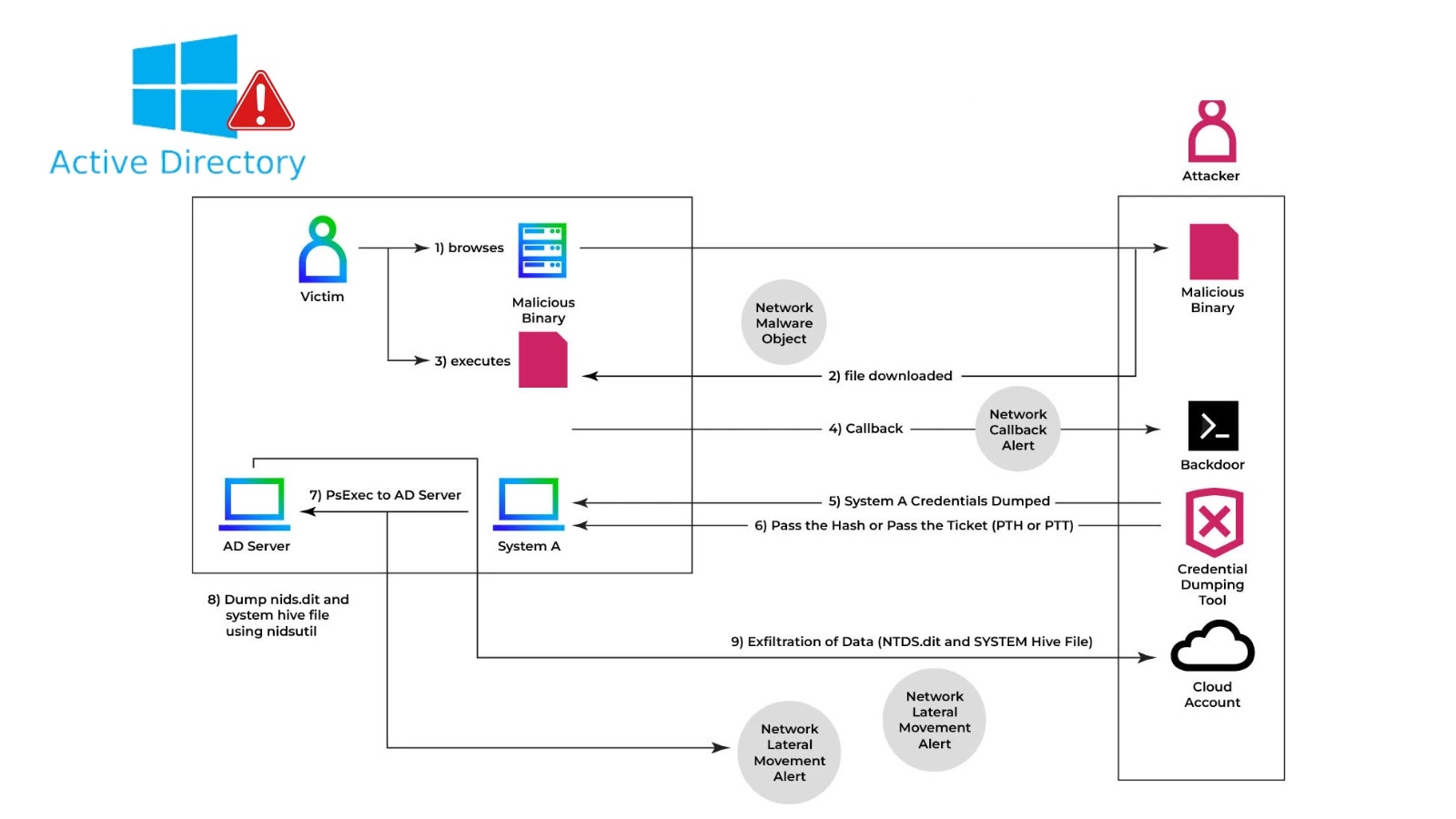
The Infection Chain: A Closer Look
The attack sequence initiated by DeepLoad is methodical and designed to evade detection at each stage:
1. Initial Deception: The user encounters a fake error message or CAPTCHA prompt, instructing them to execute a command to resolve the issue.
2. Command Execution: Upon execution, the command leverages WMI to fetch and execute a secondary payload directly in memory.
3. Payload Deployment: The in-memory execution ensures that the malware operates without writing files to the disk, thereby evading traditional antivirus solutions that monitor file-based activities.
4. Establishing Persistence: DeepLoad may create WMI event subscriptions or utilize other persistence mechanisms to maintain control over the infected system.
Comparative Analysis with Other Malware Campaigns
DeepLoad’s tactics bear similarities to other recent malware campaigns that have exploited the ClickFix technique:
– LeakNet Ransomware: This ransomware operation adopted ClickFix to gain initial access through compromised websites, instructing users to execute malicious commands. LeakNet further utilized a Deno-based loader to execute payloads in memory, akin to DeepLoad’s use of WMI for in-memory execution. ([thehackernews.com](https://thehackernews.com/2026/03/leaknet-ransomware-uses-clickfix-via.html?utm_source=openai))
– CastleLoader Malware: CastleLoader employed ClickFix phishing attacks and fake GitHub repositories to distribute various information stealers and remote access trojans. Its modular structure allowed for flexible payload deployment, similar to DeepLoad’s stealthy execution methods. ([thehackernews.com](https://thehackernews.com/2025/07/castleloader-malware-infects-469.html?utm_source=openai))
Implications for Cybersecurity
The emergence of DeepLoad underscores a concerning trend in malware development: the combination of social engineering tactics with advanced execution methods to bypass security defenses. By exploiting user trust and leveraging legitimate system features like WMI, such malware can infiltrate systems with minimal detection.
Mitigation Strategies
To defend against threats like DeepLoad, organizations and individuals should consider the following measures:
– User Education: Train users to recognize and avoid deceptive prompts that encourage the execution of unknown commands.
– Restrict WMI Usage: Implement policies to monitor and control the use of WMI, especially for script execution, to prevent unauthorized activities.
– Behavioral Analysis Tools: Deploy security solutions that focus on behavioral analysis to detect anomalies associated with in-memory execution and other stealthy tactics.
– Regular System Audits: Conduct periodic audits to identify and remediate unauthorized changes or suspicious activities within the system.
Conclusion
DeepLoad represents a sophisticated evolution in malware tactics, combining deceptive social engineering with stealthy execution methods to compromise systems. As cyber threats continue to advance, it is imperative for security professionals to stay vigilant and adopt comprehensive strategies to detect and mitigate such insidious attacks.