North Korean Operative’s Deceptive Tactics Unveiled in Remote Job Application Scam
In June 2025, a cybersecurity firm uncovered a sophisticated attempt by a suspected North Korean operative to infiltrate its workforce. The individual applied for a Lead AI Architect position, utilizing a stolen identity, an AI-generated resume, and a VoIP phone number to mask their true origins. This incident highlights the evolving and increasingly sophisticated methods employed by North Korean state-sponsored IT workers to penetrate international organizations.
The Evolving Threat of North Korean IT Operatives
Since early 2023, North Korean IT workers have been clandestinely securing remote positions in companies across the United States and other nations. These operatives pose as qualified professionals, with their earnings funneled back to the North Korean government, thereby supporting its weapons programs. Their targets are diverse, encompassing organizations of all sizes, including those in the technology, intelligence, and cybersecurity sectors.
Anatomy of the Deception
The operative in question applied for a high-level AI role, presenting themselves as a Florida-based professional with over a decade of experience in AI architecture and full-stack development. The application process was meticulously crafted to appear legitimate:
– Stolen Identity: The operative appropriated the personal information of a real Florida resident, including name and address details. This individual’s identity was used to create multiple resume accounts across various platforms, each listing slightly different educational backgrounds, employers, and locations. All these fabricated profiles traced back to the same unsuspecting individual, who was likely unaware of the misuse of their personal information.
– AI-Generated Resume: The resume submitted for the Lead AI Architect role contained an extensive list of technical skills, including programming languages, cloud platforms, agentic AI tools, and OSINT frameworks. Notably, many of these skills were directly lifted from the job posting itself. This tactic is a known strategy among North Korean IT workers, who mirror job description language in their resumes to pass keyword screening filters used by hiring systems.
– VoIP Phone Number: The phone number provided, 850-308-4867, was identified as a Voice over Internet Protocol (VoIP) number. This method is commonly used by these operatives to match their phone area code with their claimed U.S. location, further enhancing the illusion of legitimacy.
– VPN Usage: The operative utilized IP addresses 167.88.61.250 and 167.88.61.117, linked to the Astrill VPN anonymization network. This tool is frequently associated with North Korean IT workers operating out of China, allowing them to mask their actual geographic location.
Detection and Implications
The deception was uncovered through a combination of pre-employment Open-Source Intelligence (OSINT) research and carefully crafted interview questions. Analysts identified inconsistencies and red flags that led to the exposure of the operative’s true identity. The cybersecurity firm coordinated victim notification in connection with law enforcement following the discovery.
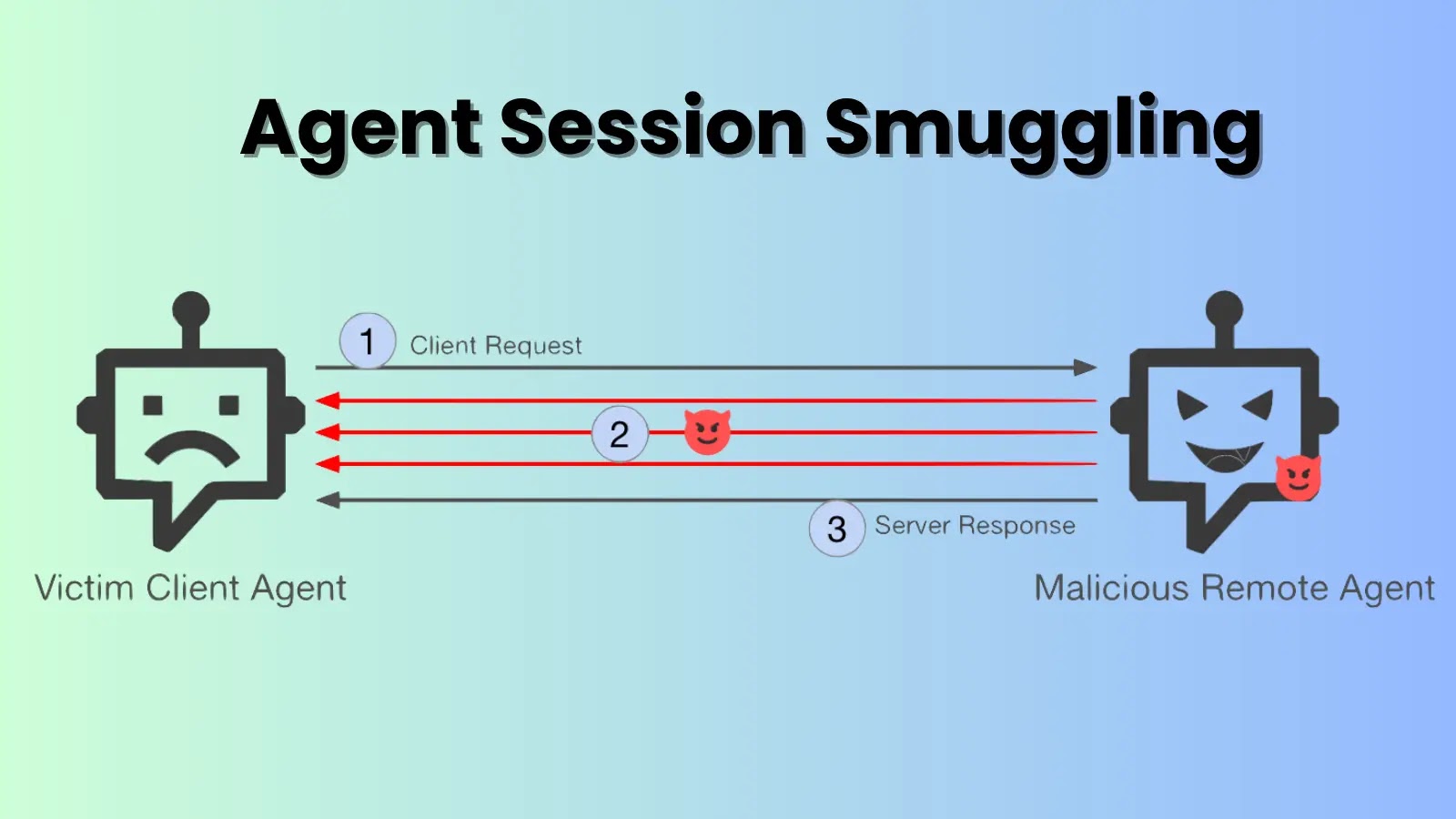
The implications of such fraudulent activities are profound. Hiring individuals tied to these schemes can expose companies to data theft, intellectual property loss, regulatory penalties, and significant reputational damage. Once hired, these operatives can use remote access tools to control company laptops from abroad while appearing to work locally, making detection extremely challenging for standard IT security teams.
Broader Context and Countermeasures
This incident is not isolated. North Korean operatives have been known to infiltrate companies by posing as remote IT workers, using similar tactics:
– Use of Deepfake Technology: In April 2025, reports emerged of North Korean IT workers deploying real-time deepfake technology during remote job interviews. This advanced technique allows them to present convincing synthetic identities, bypassing traditional identity verification processes and infiltrating companies for financial gain and potential espionage.
– Exploitation of GitHub: In March 2025, cybersecurity research revealed that suspected North Korean IT workers were leveraging GitHub to create elaborate fake personas aimed at securing employment with companies in Japan and the United States. These individuals posed as nationals from various countries, seeking positions in remote engineering and full-stack blockchain development.
– Infiltration of European Organizations: By April 2025, North Korean IT workers had expanded their operations beyond the United States, focusing on European organizations. They posed as legitimate remote workers to infiltrate companies, generating revenue for the DPRK regime while potentially compromising sensitive corporate infrastructure.
To counter these threats, organizations must implement robust identity verification processes for remote hires, including:
– Enhanced Screening Procedures: Conduct thorough background checks, including verification of educational and employment histories, and cross-reference provided information with multiple sources.
– Technical Controls: Implement insider threat monitoring, geolocation of devices, and restrict data exposure to minimize potential risks.
– Awareness and Training: Educate HR and IT security teams about the tactics used by these operatives and the importance of vigilance during the hiring process.
The infiltration of North Korean IT workers into international companies poses a dual threat of sanctions violations and severe cybersecurity risks. As remote work continues to grow, it is crucial for organizations and governments to collaborate on enhanced security measures and intelligence sharing to combat this evolving threat.