Massive Supply Chain Attack: Telnyx PyPI Package Compromised by TeamPCP
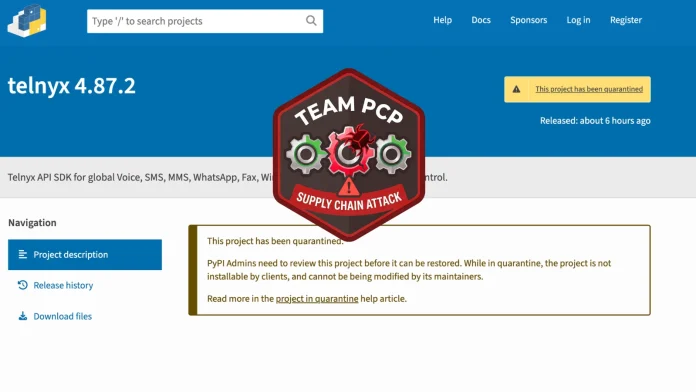
In a significant escalation of supply chain attacks, the official Telnyx Python Software Development Kit (SDK) hosted on the Python Package Index (PyPI) was compromised on March 27, 2026. This breach is part of a broader, coordinated campaign by the threat actor group known as TeamPCP, which has been actively targeting trusted developer tools and libraries to infiltrate and exploit development environments.
The Breach Details
At 03:51 UTC on March 27, malicious versions 4.87.1 and 4.87.2 of the `telnyx` package were uploaded to PyPI. These versions contained payloads designed to execute automatically upon import, affecting both Windows and Unix-based systems. Given that the Telnyx SDK has been downloaded approximately 742,000 times in the past month, the potential impact of this compromise is substantial.
Understanding TeamPCP’s Attack Strategy
TeamPCP’s modus operandi involves a systematic approach to compromising the software supply chain:
1. Initial Compromise: The group first targets a widely-used security or developer tool.
2. Credential Harvesting: By infiltrating the tool, they gain access to Continuous Integration/Continuous Deployment (CI/CD) credentials.
3. Propagation: Utilizing the stolen credentials, they compromise subsequent targets, creating a cascading effect throughout the development ecosystem.
This method not only allows for widespread infiltration but also makes detection and mitigation more challenging due to the interconnected nature of modern development pipelines.
Timeline of the Attack Campaign
The following timeline outlines the progression of TeamPCP’s campaign leading up to the Telnyx compromise:
– March 19, 2026: Aqua Security’s open-source vulnerability scanner, Trivy, was backdoored. This breach, identified as CVE-2026-33634 with a CVSS score of 9.4, involved the attacker force-pushing malicious binaries to multiple Trivy-related tags. As a result, CI/CD secrets, including npm tokens, Docker Hub credentials, and PyPI publishing tokens, were harvested from pipelines running unpinned versions of Trivy.
– March 20, 2026: Leveraging the stolen npm tokens from the Trivy breach, TeamPCP deployed the CanisterWorm backdoor across over 46 npm packages. This worm automated the process of compromising packages by enumerating all publishable packages associated with a stolen token, bumping their versions, and publishing malicious releases within a minute.
– March 22, 2026: The group introduced a novel technique by embedding malware payloads within `.wav` audio files, utilizing WAV steganography. This method was employed in a Kubernetes wiper variant, marking the first instance of this technique in their campaign.
– March 23, 2026: Checkmarx’s GitHub Actions, including `kics-github-action` and `ast-github-action`, were compromised. Additionally, two OpenVSX extensions (`cx-dev-assist 1.7.0` and `ast-results 2.53.0`) were affected. The attacker hijacked 35 tags within a few hours, using a new command-and-control (C2) domain, `checkmarx[.]zone`, to impersonate Checkmarx’s brand. The malicious code was removed approximately three hours later.
– March 24, 2026: LiteLLM versions 1.82.7 and 1.82.8 were published to PyPI using credentials stolen from LiteLLM’s CI/CD pipeline, which had been running an unpinned version of Trivy. LiteLLM, serving roughly 95 million downloads per month, is widely deployed as a centralized Large Language Model (LLM) gateway with access to credentials for various AI services. PyPI quarantined the malicious packages within approximately three hours.
– March 27, 2026: The Telnyx SDK became the latest victim in this series of attacks.
Technical Analysis of the Telnyx Payload
According to an advisory by Akidio, the malicious code injected into the Telnyx package resides in the `telnyx/_client.py` file and executes upon import. This design ensures that the malware activates immediately when a developer or application imports the `telnyx` module, without relying on installation hooks or post-install scripts.
The payload’s behavior varies based on the host operating system:
– Windows Systems: The malware downloads a file named `hangup.wav` from the attacker’s C2 server at `83[.]142[.]209[.]203:8080`. This audio file contains a base64-encoded, XOR-obfuscated executable within its frame data. Once decoded, the dropper writes the executable to `%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\msbuild.exe`, ensuring it runs silently upon every system login.
– Unix-Based Systems (Linux/macOS): The payload downloads a similar `hangup.wav` file, decodes the embedded executable, and writes it to `~/.config/autostart/msbuild.desktop`. This setup ensures the malware executes upon user login, maintaining persistence on the system.
Implications and Recommendations
The compromise of the Telnyx SDK underscores the escalating threat posed by supply chain attacks, particularly those targeting widely-used developer tools and libraries. Organizations and developers utilizing the affected versions of the Telnyx package should consider their environments fully compromised and take immediate action:
1. Immediate Remediation: Uninstall the compromised versions (4.87.1 and 4.87.2) of the Telnyx package and replace them with a verified, clean version.
2. Credential Rotation: Rotate all credentials that may have been exposed, including API keys, database passwords, and any other sensitive information.
3. System Audit: Conduct a thorough audit of systems to identify any unauthorized access or anomalies that may have resulted from the compromise.
4. Enhance Security Practices: Implement stricter controls over CI/CD pipelines, including version pinning for dependencies, regular security assessments, and monitoring for unusual activity.
This incident serves as a stark reminder of the importance of vigilance in software supply chain security. As attackers continue to refine their methods, it is imperative for organizations to adopt proactive measures to safeguard their development environments and the integrity of their software products.