Critical Windows Error Reporting Vulnerability Enables SYSTEM-Level Privilege Escalation
A significant security flaw has been identified in the Windows Error Reporting (WER) service, designated as CVE-2026-20817. This vulnerability allows attackers with standard user privileges to escalate their access to SYSTEM-level control, posing a substantial risk to Windows systems.
Understanding CVE-2026-20817
CVE-2026-20817 is a local privilege escalation vulnerability within the WER service, which is responsible for collecting and reporting crash data in Windows operating systems. The flaw arises from improper handling of permissions during WER operations, enabling a local attacker to execute code with elevated privileges. This vulnerability is classified under CWE-280, indicating a failure in managing insufficient permissions or privileges.
Technical Details and Exploitation
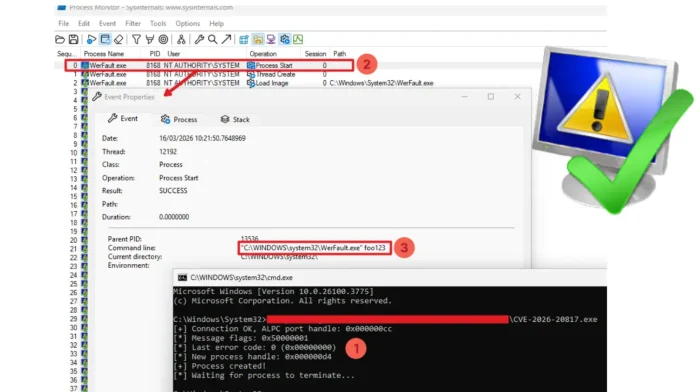
The core issue lies in the `wersvc.dll` file, the main executable library of the WER service. The vulnerability is exploited through the manipulation of Advanced Local Procedure Call (ALPC) messages sent to the `\WindowsErrorReportingServicePort` endpoint. An attacker crafts a message containing a File Mapping object, prompting the internal `ElevatedProcessStart` function to duplicate the handle and read the malicious command-line arguments using the `MapViewOfFile` API. Ultimately, the `CreateElevatedProcessAsUser` function is called, which inadvertently launches the legitimate `WerFault.exe` application with highly privileged SYSTEM rights and the attacker’s controlled parameters.
To exploit this flaw, an attacker must first connect to the ALPC port using the `NtAlpcConnectPort` API and subsequently send their payload using the `NtAlpcSendWaitReceivePort` API. The malicious data structure must contain the correct `MessageFlags` parameter and structural padding to successfully trigger the vulnerable dispatcher logic.
Discovery and Mitigation
Security researchers Denis Faiustov and Ruslan Sayfiev at GMO Cybersecurity identified this vulnerability. Given the structural danger of the flaw, Microsoft opted to remove the vulnerable feature entirely rather than attempting a traditional code patch. Developers introduced a strict `__private_IsEnabled()` feature test that permanently disables the `SvcElevatedLaunch` functionality. If the patched code is executed, the function immediately returns an `0x80004005 (E_FAIL)` error code, effectively neutralizing the entire attack surface by removing the feature entirely.
Implications and Recommendations
The exploitation of CVE-2026-20817 allows attackers to gain SYSTEM-level privileges, enabling complete system compromise, persistence establishment, and lateral movement capabilities. While the vulnerability requires local access, its low complexity and lack of user interaction make it an attractive target for post-exploitation privilege escalation.
To mitigate the risk associated with this vulnerability, it is crucial to apply the security updates provided by Microsoft promptly. Additionally, monitoring for unusual process creation by `WerFault.exe` or `wermgr.exe` with unexpected child processes, anomalous file operations in WER directories, and suspicious privilege token manipulation events associated with WER processes can help detect potential exploitation attempts.
In conclusion, CVE-2026-20817 represents a critical security concern within the Windows Error Reporting service. Timely application of patches and vigilant monitoring are essential to protect systems from potential exploitation.