Exploiting OAuth Device Code Flow: A New Frontier in Phishing Attacks
In recent developments, cybersecurity experts have identified a surge in phishing campaigns that exploit Microsoft’s OAuth Device Authorization Grant flow. This sophisticated technique allows attackers to hijack Microsoft 365 accounts without the need to steal passwords, presenting a significant challenge to traditional security measures.
Understanding OAuth Device Code Flow
OAuth 2.0’s Device Authorization Grant flow was originally designed to facilitate user authentication on devices with limited input capabilities, such as smart TVs or IoT devices. This method enables users to grant access to applications by entering a short code on a separate device, streamlining the login process without requiring direct credential input on the constrained device.
The Phishing Attack Mechanism
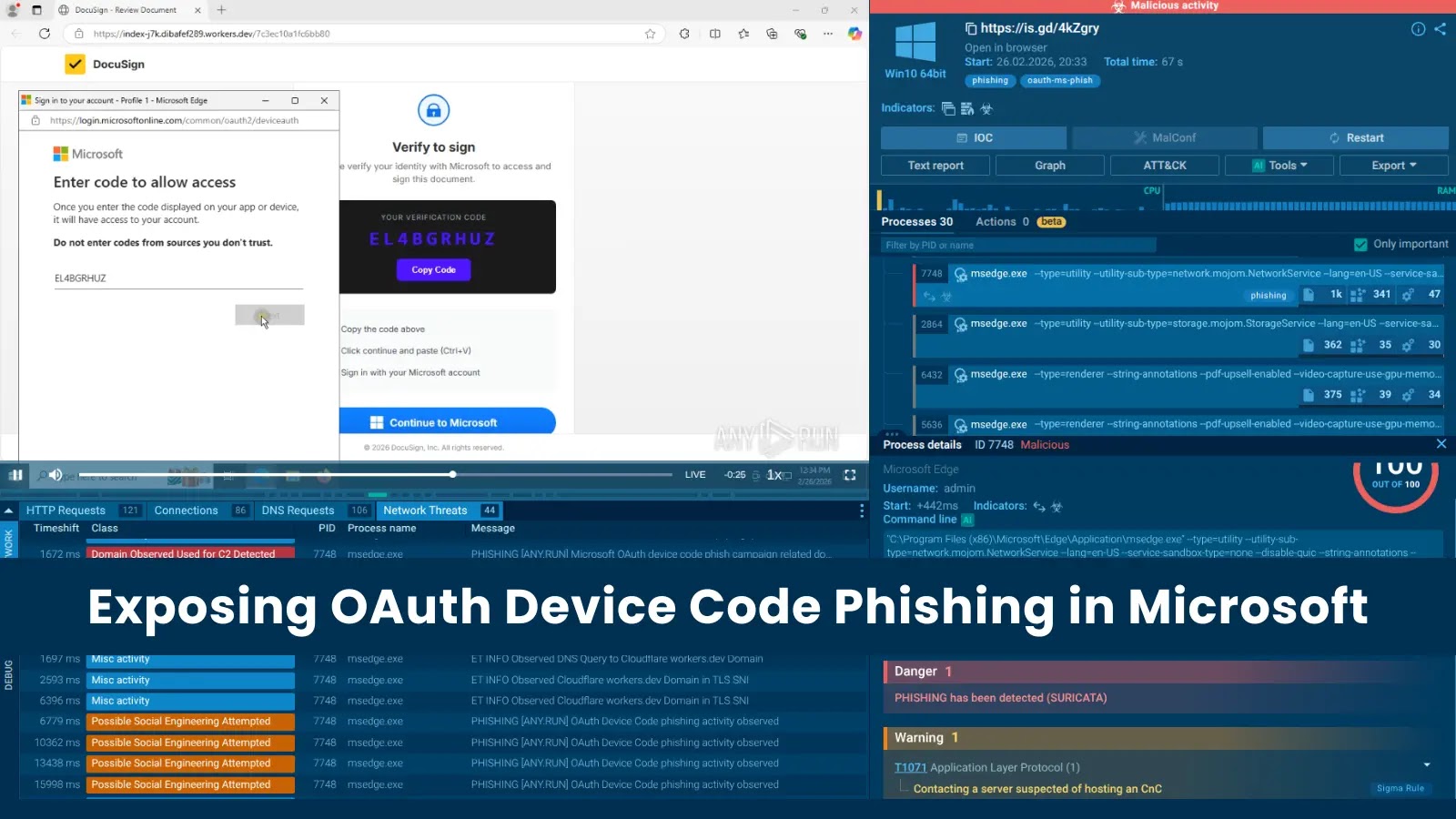
Attackers have ingeniously repurposed this legitimate authentication flow to orchestrate phishing attacks. The attack sequence typically unfolds as follows:
1. Initiation of Device Authorization Request: The attacker initiates a device authorization request through Microsoft’s OAuth service, generating two critical values:
– User Code: A short, user-friendly code intended for the victim to enter.
– Device Code: A token retained by the attacker to monitor the authorization process.
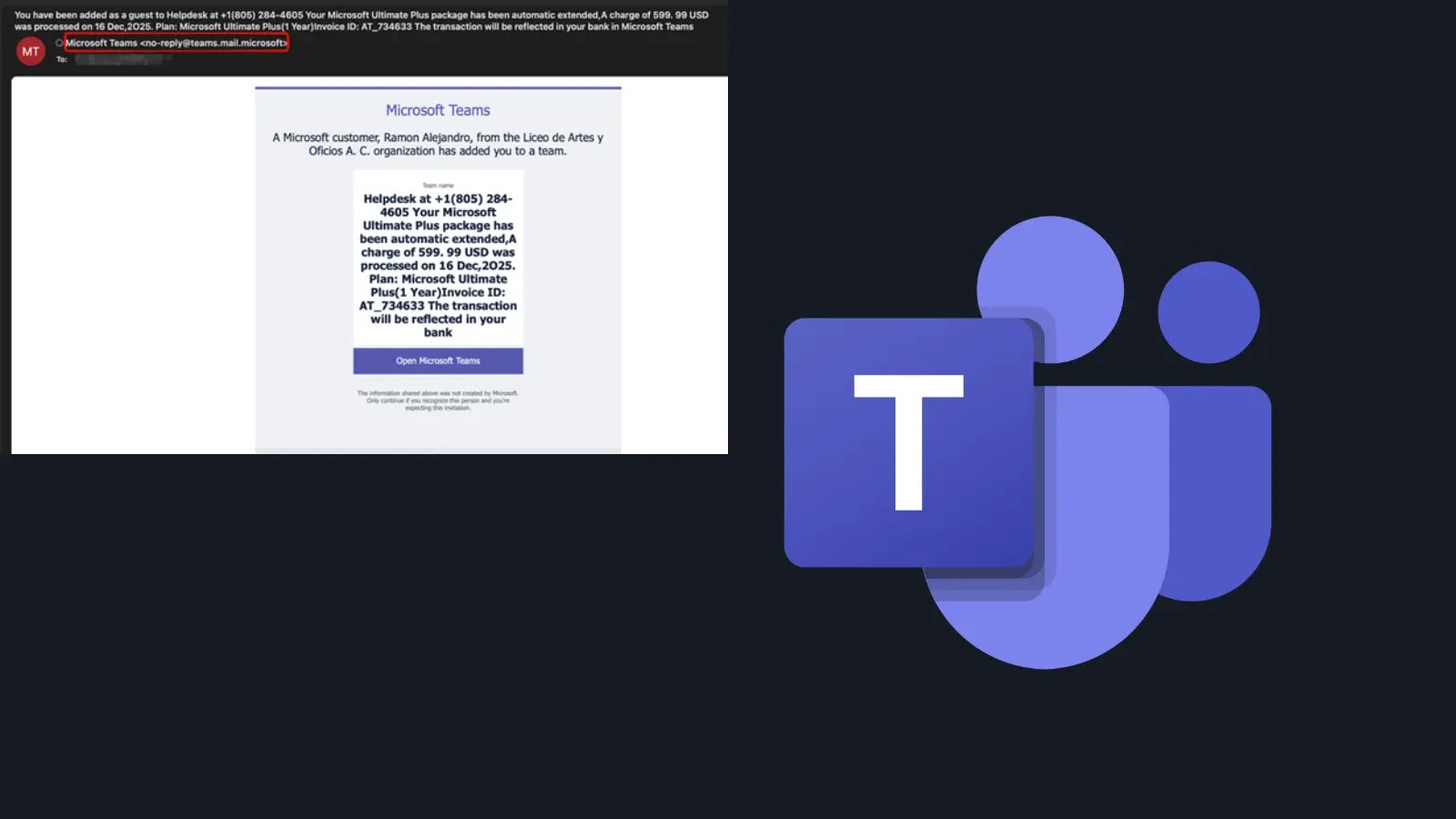
2. Phishing Email Delivery: The victim receives a phishing email, often masquerading as a legitimate service like DocuSign or Microsoft Teams. This email prompts the user to visit Microsoft’s official device login page (`microsoft.com/devicelogin`) and enter the provided user code to access a document or service.
3. User Authorization: Trusting the legitimacy of the request, the victim navigates to the genuine Microsoft device login page and inputs the user code. This action inadvertently grants the attacker OAuth tokens, including access and refresh tokens, without the victim’s knowledge.
4. Attacker Gains Access: With the OAuth tokens in hand, the attacker gains persistent access to the victim’s Microsoft 365 account, enabling them to read emails, access files, and perform other actions as the authenticated user.
Challenges in Detection
This method of attack poses significant challenges for detection and prevention:
– Legitimate Infrastructure Utilization: The entire process leverages Microsoft’s legitimate authentication infrastructure, making it difficult for security systems to flag the activity as malicious.
– Bypassing Multi-Factor Authentication (MFA): Since the user willingly completes the MFA process during the device code entry, traditional MFA mechanisms are rendered ineffective against this attack vector.
– Delayed Detection: Security teams may only become aware of the compromise after observing suspicious activities within the account, such as unauthorized email forwarding or data exfiltration.
Mitigation Strategies
To defend against such sophisticated phishing attacks, organizations and individuals should consider implementing the following measures:
1. User Education and Awareness: Educate users about the risks associated with device code authentication and the importance of verifying requests before entering codes on official platforms.
2. Restrict Device Code Flow Usage: Evaluate the necessity of the device code flow within the organization. If not essential, consider disabling it or restricting its use through conditional access policies.
3. Monitor OAuth Applications: Regularly audit and monitor OAuth applications that have been granted access to organizational resources. Be vigilant for any unauthorized or suspicious applications.
4. Implement Conditional Access Policies: Utilize conditional access policies to enforce stricter controls over how and when users can grant permissions to applications, reducing the risk of unauthorized access.
5. Enhance Logging and Monitoring: Strengthen logging and monitoring capabilities to detect unusual activities associated with OAuth token usage, such as unexpected sign-ins from unfamiliar locations or devices.
Conclusion
The exploitation of OAuth’s Device Authorization Grant flow in phishing campaigns underscores the evolving tactics of cyber attackers. By leveraging legitimate authentication processes, these attacks can effectively bypass traditional security measures, including MFA. It is imperative for organizations to stay informed about such threats and proactively implement comprehensive security strategies to safeguard against unauthorized access and data breaches.