Critical Active Directory Vulnerability Allows Attackers to Gain SYSTEM Privileges
On March 10, 2026, Microsoft released a crucial security update addressing a significant vulnerability in Active Directory Domain Services (AD DS). Identified as CVE-2026-25177, this flaw carries a CVSS score of 8.8, indicating its high severity. The vulnerability enables authorized network attackers to escalate their privileges to full SYSTEM control, posing a substantial risk to organizational security.
Understanding the Vulnerability
The core issue arises from an improper restriction on file and resource names, classified under CWE-641. This elevation of privilege flaw allows attackers to exploit the system by creating duplicate Service Principal Names (SPNs) or User Principal Names (UPNs) using specially crafted Unicode characters. These hidden characters can bypass standard Active Directory security checks designed to prevent such duplicates.
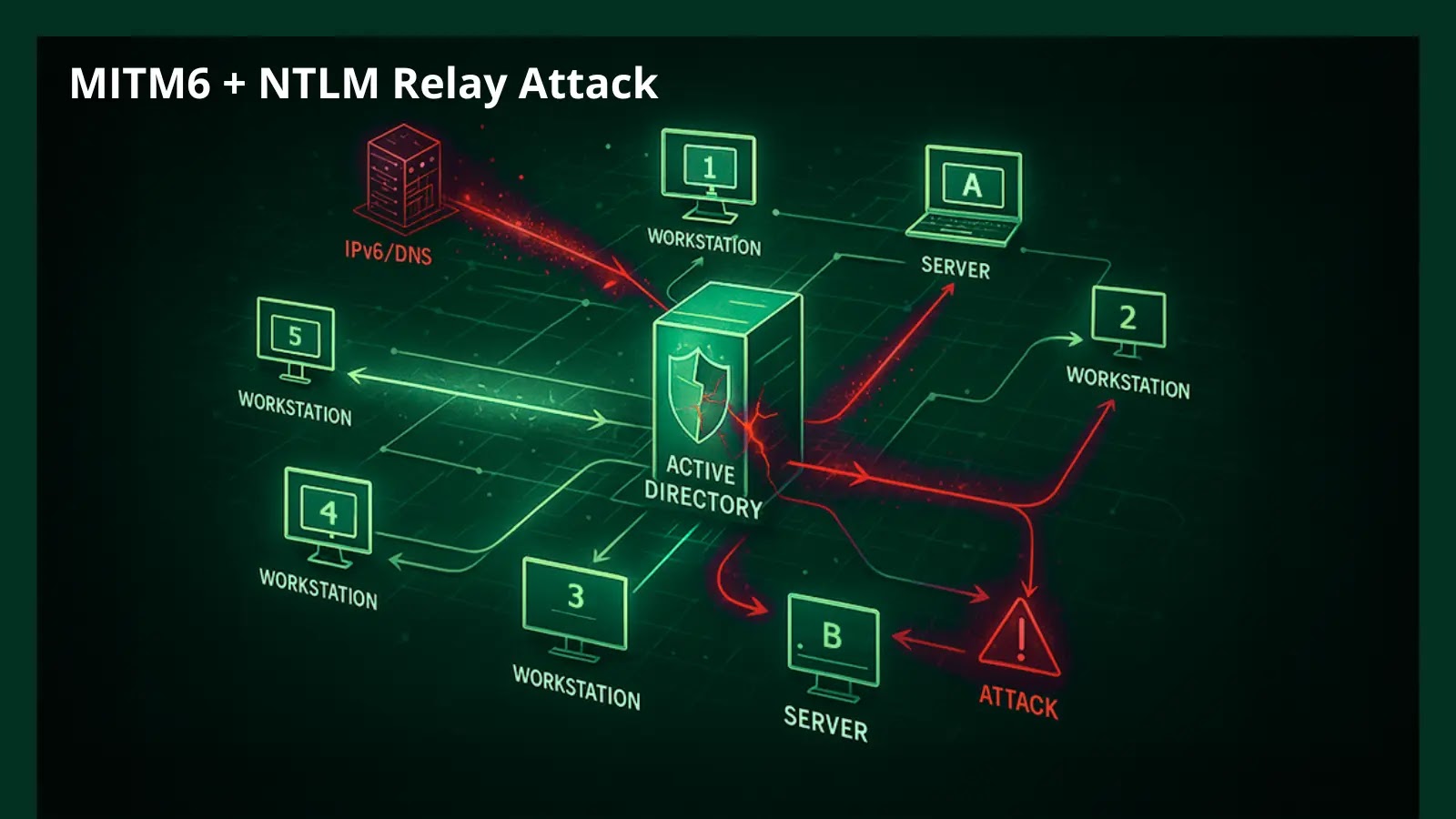
Attack Mechanism
To exploit this vulnerability, an attacker requires minimal privileges—specifically, the standard permission to write or modify SPNs on an account. The attack is conducted entirely over the network, has low complexity, and does not necessitate user interaction. When a client requests Kerberos authentication for a service associated with a duplicate SPN, the domain controller issues a ticket encrypted with an incorrect key. Consequently, the target service rejects the ticket, leading to a denial-of-service (DoS) attack or forcing the network to revert to the less secure NTLM authentication protocol if it remains enabled.
Notably, the attacker does not need direct access to the targeted server beyond the initial SPN-write permission. A successful exploit grants the attacker full SYSTEM privileges, allowing complete control over the server and potentially the broader domain environment.
Current Risk Assessment
As of the update’s release, Microsoft assesses the exploitability of this vulnerability as Less Likely, with no public exploit code or active attacks reported in the wild. However, the potential impact of a successful exploit necessitates immediate attention and remediation.
Mitigation Measures
Microsoft, in coordination with cybersecurity firm Semperis, has released official security updates to address this flaw. Network administrators are strongly advised to apply these patches promptly to secure their environments. The updates are comprehensive, covering a wide range of operating systems, including Windows 10, Windows 11, and various Windows Server editions from 2012 through the latest 2025 releases.
In addition to applying the patches, organizations should proactively monitor their Active Directory environments for unusual SPN modifications. Implementing robust monitoring can serve as an effective defense measure, helping to detect and mitigate potential exploitation attempts.
Broader Implications
This vulnerability underscores the critical importance of maintaining up-to-date security measures within Active Directory environments. Active Directory serves as the backbone of many organizational networks, managing user authentication and authorization. A compromise at this level can have far-reaching consequences, including unauthorized access to sensitive data, disruption of services, and potential lateral movement within the network by malicious actors.
Recommendations for Administrators
1. Immediate Patch Application: Ensure that all relevant systems are updated with the latest security patches provided by Microsoft to address CVE-2026-25177.
2. Monitor SPN Modifications: Implement monitoring tools to detect and alert on unusual or unauthorized changes to SPNs and UPNs within the Active Directory environment.
3. Review Permissions: Conduct a thorough review of permissions related to SPN and UPN modifications. Limit these permissions to only those accounts that absolutely require them, reducing the potential attack surface.
4. Enhance Authentication Protocols: Evaluate the use of NTLM authentication within the network. If possible, disable NTLM to prevent fallback to this less secure protocol in the event of an attack.
5. User Education: Educate users and administrators about the risks associated with this vulnerability and the importance of adhering to security best practices, including regular updates and cautious management of permissions.
Conclusion
The discovery and subsequent patching of CVE-2026-25177 highlight the ongoing challenges in securing complex network environments. While Microsoft has provided the necessary updates to mitigate this specific threat, it serves as a reminder of the importance of vigilance, prompt patch management, and proactive monitoring in maintaining the security and integrity of organizational networks.