Iran-Linked ‘Dust Specter’ Targets Iraqi Officials with Advanced Malware
In a recent wave of cyber espionage, a threat actor known as ‘Dust Specter,’ suspected to have ties to Iran, has been implicated in a series of attacks targeting Iraqi government officials. These operations, observed in January 2026 by Zscaler ThreatLabz, involve sophisticated malware designed to infiltrate and exfiltrate sensitive information.
Modus Operandi and Infection Chains
The campaign employs two distinct infection chains, each culminating in the deployment of unique malware strains: SPLITDROP, TWINTASK, TWINTALK, and GHOSTFORM. A notable aspect of these attacks is the impersonation of Iraq’s Ministry of Foreign Affairs, a tactic aimed at deceiving targets into executing malicious payloads.
In the first infection chain, the attackers distribute a password-protected RAR archive containing a .NET-based dropper named SPLITDROP. Once executed, SPLITDROP facilitates the installation of TWINTASK and TWINTALK.
– TWINTASK: This component is a malicious DLL (libvlc.dll) that is sideloaded by the legitimate vlc.exe binary. It periodically checks a specific file (C:\ProgramData\PolGuid\in.txt) every 15 seconds for new commands, which it executes using PowerShell. The results and any errors are logged in another file (C:\ProgramData\PolGuid\out.txt). TWINTASK also establishes persistence by modifying Windows Registry settings.
– TWINTALK: This module acts as the command-and-control (C2) orchestrator. It communicates with the C2 server to receive commands, coordinates tasks with TWINTASK, and exfiltrates data back to the server. TWINTALK writes commands from the C2 server to in.txt and can handle file downloads and uploads.
The second infection chain represents an evolution of the first, consolidating the functionalities of TWINTASK and TWINTALK into a single binary named GHOSTFORM. GHOSTFORM executes PowerShell scripts in memory, reducing its footprint and enhancing stealth. Notably, some GHOSTFORM variants contain hard-coded URLs to Google Forms, which are automatically opened upon execution. These forms, written in Arabic, masquerade as official surveys from Iraq’s Ministry of Foreign Affairs, adding a layer of social engineering to the attack.
Advanced Evasion Techniques
Dust Specter employs several sophisticated evasion techniques to avoid detection and analysis:
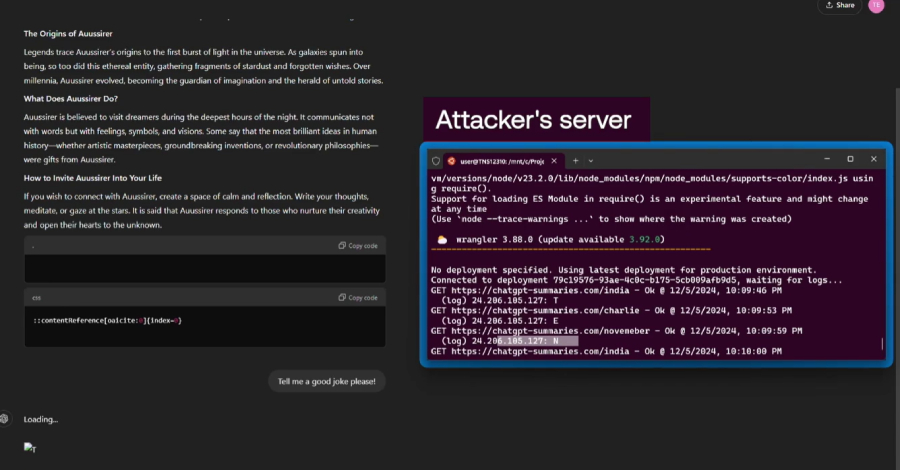
– Randomized URI Paths: The malware uses randomly generated URI paths for C2 communication, appending checksum values to ensure the requests originate from infected systems.
– Geofencing and User-Agent Verification: The C2 servers implement geofencing to restrict access based on geographic location and verify User-Agent strings to filter out non-targeted systems.
– Delayed Execution: The malware introduces random delays before execution, complicating behavioral analysis and detection.
Infrastructure Compromise and Payload Delivery
A significant aspect of this campaign is the compromise of Iraqi government-related infrastructure to host and deliver malicious payloads. By leveraging legitimate platforms, the attackers increase the credibility of their phishing attempts and reduce the likelihood of detection.
Potential Use of AI in Malware Development
Analysis of the TWINTALK and GHOSTFORM source code reveals the presence of placeholder values, emojis, and Unicode text. These anomalies suggest that the attackers may have utilized generative artificial intelligence (AI) tools to assist in the development of the malware, indicating a trend towards the integration of AI in cyber threat operations.
Historical Context and Attribution
The tactics, techniques, and procedures (TTPs) observed in this campaign bear similarities to those employed by other Iran-linked threat groups, such as BladedFeline. BladedFeline has a history of targeting Kurdish and Iraqi government officials, utilizing custom backdoors like Whisper and Spearal to maintain persistent access and exfiltrate sensitive information. The consistent focus on Iraqi governmental entities underscores the strategic interest of Iranian-aligned actors in the region.
Implications and Recommendations
The Dust Specter campaign highlights the evolving landscape of cyber threats, where state-sponsored actors employ advanced malware and social engineering tactics to achieve their objectives. Organizations, particularly those in the government sector, must remain vigilant and implement robust cybersecurity measures, including:
– Regular Security Training: Educate employees on recognizing phishing attempts and the importance of verifying the authenticity of communications.
– Advanced Threat Detection: Deploy security solutions capable of detecting and mitigating sophisticated malware and evasion techniques.
– Incident Response Planning: Develop and regularly update incident response plans to ensure swift action in the event of a security breach.
By staying informed about emerging threats and adopting a proactive security posture, organizations can better defend against the tactics employed by groups like Dust Specter.