Cybercriminals Exploit Fake Claude Code Downloads to Deploy Infostealer Malware
In a recent wave of cyberattacks, threat actors have been targeting developers and IT professionals by creating counterfeit download pages that mimic Claude Code, a reputable AI coding assistant. These deceptive sites are meticulously designed to resemble legitimate software portals, luring unsuspecting users into downloading what appears to be the official installation package. However, instead of the genuine software, these downloads deploy infostealer malware onto the victim’s system, compromising sensitive information.
This tactic underscores a growing trend where cybercriminals exploit the rising trust in artificial intelligence platforms to deceive users. By leveraging the credibility of well-known AI tools, attackers can bypass initial suspicions, making their malicious campaigns more effective.
The Attack Mechanism
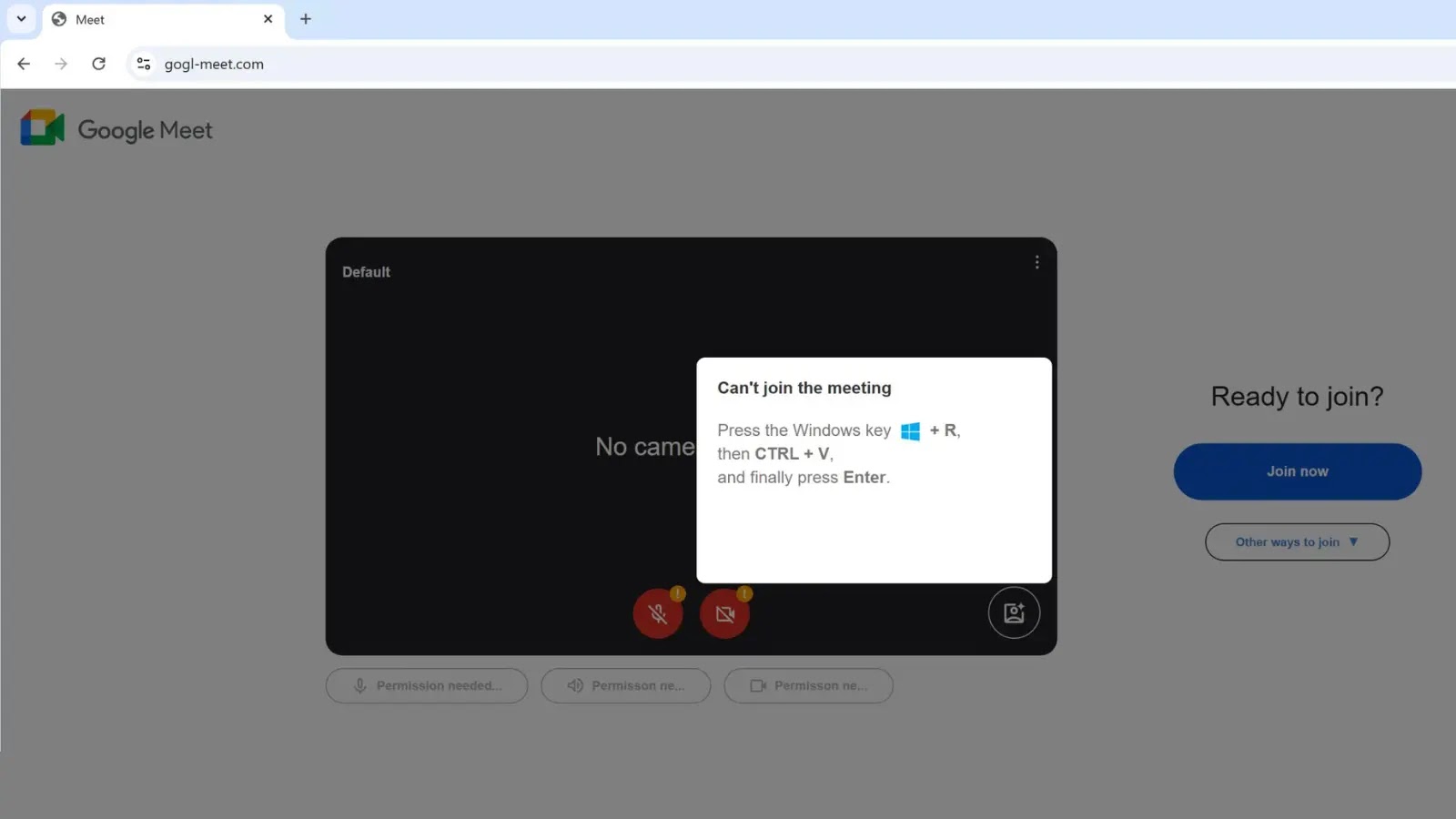
The attack begins when a user visits a fraudulent download page that closely mirrors the official Claude Code website. Upon clicking the download button, the user initiates a malicious execution chain. The downloaded file, often an HTML Application (HTA), is executed using `mshta.exe`, a legitimate Microsoft Windows binary. This process is commonly referred to as a Living off the Land Binary (LOLBin) attack, where attackers misuse legitimate system tools to execute malicious code, thereby evading detection.
Once executed, the HTA file runs scripts that deploy the infostealer malware. This malware is designed to harvest a wide range of sensitive data, including browser-stored credentials, session tokens, and other personal information. The collected data is then transmitted to attacker-controlled servers, potentially leading to further exploitation or financial loss for the victim.
Broader Implications
The implications of such attacks are particularly severe for developers and IT professionals. Compromised credentials can grant attackers unauthorized access to code repositories, cloud environments, and internal systems. This not only jeopardizes personal data but also poses significant risks to organizational security, potentially leading to data breaches, intellectual property theft, and operational disruptions.
This campaign is not an isolated incident. Similar tactics have been observed in previous attacks where cybercriminals exploited the branding of popular AI tools to distribute malware. For instance, earlier campaigns utilized fake Claude-themed lures to deceive users, indicating a persistent strategy among threat actors to capitalize on the growing adoption of AI-assisted coding platforms.
Technical Analysis
The use of `mshta.exe` in this attack is particularly noteworthy. As a signed Microsoft binary, `mshta.exe` is inherently trusted by the Windows operating system. By leveraging this tool, attackers can execute malicious scripts without triggering security alerts, effectively bypassing traditional detection mechanisms. This technique is cataloged under MITRE ATT&CK as T1218.005, highlighting its recognition as a method for defense evasion.
The malicious HTA files used in these attacks often contain obfuscated scripts that perform various functions, such as downloading additional payloads, establishing persistence, and exfiltrating data. The obfuscation makes it challenging for security tools to analyze and detect the malicious code, further enhancing the stealthiness of the attack.
Preventive Measures
To mitigate the risks associated with such attacks, users are advised to adopt the following preventive measures:
1. Verify Download Sources: Always download software from official and reputable sources. Be cautious of download links provided through unsolicited emails or unfamiliar websites.
2. Monitor System Processes: Keep an eye on the execution of system binaries like `mshta.exe`. Unusual activity involving these processes can be indicative of malicious behavior.
3. Implement Endpoint Protection: Utilize comprehensive endpoint protection solutions that can detect and block malicious scripts and behaviors associated with LOLBin attacks.
4. Educate Users: Regularly train employees and users on the latest phishing tactics and social engineering techniques to enhance their ability to recognize and avoid potential threats.
5. Regular Updates: Ensure that all software, including operating systems and security tools, are up to date with the latest patches and definitions to protect against known vulnerabilities.
Conclusion
The exploitation of fake Claude Code downloads to deploy infostealer malware highlights the evolving tactics of cybercriminals who are increasingly leveraging the trust in AI tools to execute their attacks. By understanding the mechanisms of such attacks and implementing robust security measures, individuals and organizations can better protect themselves against these sophisticated threats.