CyberStrikeAI: The Open-Source Tool Powering AI-Driven Cyber Attacks Across 55 Countries
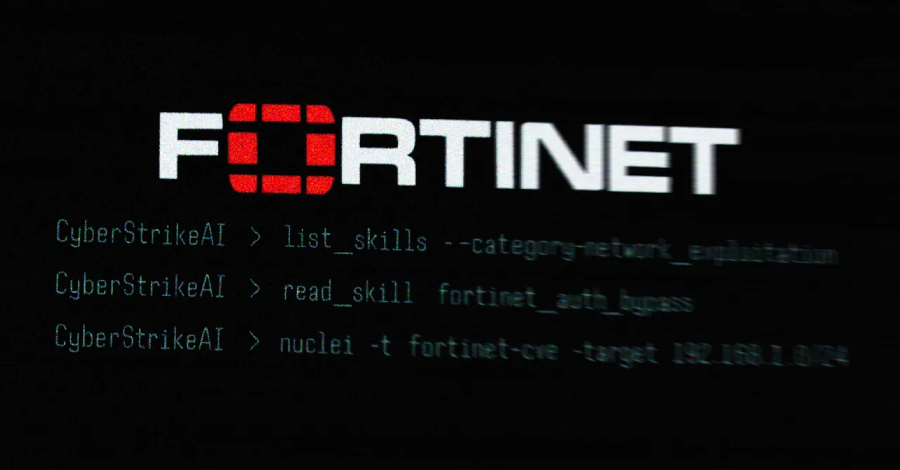
In a significant development in the cybersecurity landscape, an open-source platform named CyberStrikeAI has been identified as the driving force behind a series of AI-assisted cyber attacks targeting Fortinet FortiGate appliances across 55 countries. This revelation underscores the escalating integration of artificial intelligence in cyber warfare, presenting new challenges for global security.
Unveiling the CyberStrikeAI Connection
Recent investigations by Team Cymru have traced the origins of these sophisticated attacks to CyberStrikeAI, an AI-native security testing platform. The platform was utilized by a suspected Russian-speaking threat actor who conducted automated mass scanning for vulnerable FortiGate appliances. The analysis pinpointed the IP address 212.11.64[.]250 as a key node in these operations.
CyberStrikeAI is an open-source offensive security tool developed by a Chinese developer known by the alias Ed1s0nZ. Security researcher Will Thomas, also known as @BushidoToken, highlighted that the developer is believed to have affiliations with the Chinese government. The platform is built in Go and integrates over 100 security tools, facilitating vulnerability discovery, attack-chain analysis, knowledge retrieval, and result visualization.
The Scope of the Attacks
The AI-powered campaign came to light when Amazon Threat Intelligence reported systematic targeting of FortiGate devices using generative AI services like Anthropic Claude and DeepSeek. This campaign led to the compromise of over 600 appliances in 55 countries, marking a significant escalation in the use of AI in cyber attacks.
Developer’s Profile and Affiliations
The developer behind CyberStrikeAI, Ed1s0nZ, has a GitHub repository that hosts several other tools indicating a deep interest in exploitation and AI model manipulation. These tools include:
– watermark-tool: Adds invisible digital watermarks to documents.
– banana_blackmail: A Golang-based ransomware.
– PrivHunterAI: Utilizes Kimi, DeepSeek, and GPT models to detect privilege escalation vulnerabilities.
– ChatGPTJailbreak: Contains prompts to jailbreak OpenAI’s ChatGPT by inducing it into a Do Anything Now (DAN) mode or enabling Developer Mode.
– InfiltrateX: A Golang-based scanner for detecting privilege escalation vulnerabilities.
– VigilantEye: Monitors databases for the disclosure of sensitive information, such as phone numbers and ID card numbers, and sends alerts via a WeChat Work bot if a potential data breach is detected.
Further analysis reveals that Ed1s0nZ has interacted with organizations supporting potentially state-sponsored cyber operations. Notably, the developer has connections with Knownsec 404, a Chinese security vendor that suffered a significant data leak exposing internal documents, employee data, government clientele, hacking tools, and information related to cyber operations targeting other countries.
Implications and Future Outlook
The deployment of CyberStrikeAI in these attacks signifies a concerning evolution in cyber threats, where AI tools are increasingly being weaponized. The open-source nature of CyberStrikeAI allows for widespread access and potential misuse, raising alarms about the proliferation of AI-augmented offensive security tools.
As AI continues to advance, its integration into cyber attack methodologies is likely to become more sophisticated. This trend necessitates a reevaluation of current cybersecurity strategies and the development of robust defenses against AI-driven threats.
In conclusion, the emergence of CyberStrikeAI as a tool in widespread cyber attacks highlights the dual-use nature of AI technologies. While AI offers numerous benefits, its potential for misuse in cyber warfare presents a formidable challenge that requires coordinated global efforts to address.