ScarCruft’s Sophisticated Cyber Assaults: Exploiting Zoho WorkDrive and USB Malware to Infiltrate Air-Gapped Networks
In a recent cybersecurity revelation, the North Korean state-sponsored hacking group known as ScarCruft has been identified employing advanced tactics to breach highly secure, air-gapped networks. This campaign, dubbed Ruby Jumper by Zscaler ThreatLabz, showcases the group’s evolving methodologies in cyber espionage.
Unveiling the Ruby Jumper Campaign
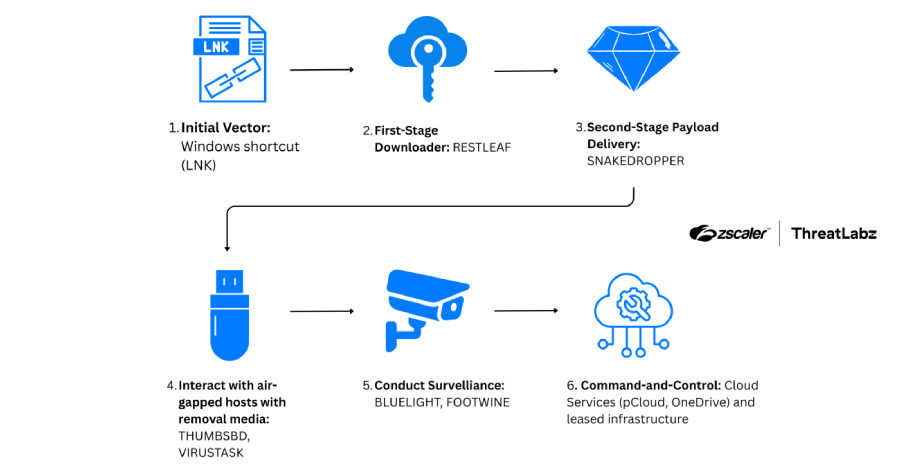
Discovered in December 2025, the Ruby Jumper campaign involves a series of sophisticated malware tools designed to infiltrate and surveil target systems. The primary components of this campaign include:
– RESTLEAF: A backdoor leveraging Zoho WorkDrive for command-and-control (C2) communications.
– SNAKEDROPPER: A payload installer that sets up the environment for further malware deployment.
– THUMBSBD: An implant utilizing removable media to bridge the gap between internet-connected and air-gapped systems.
– VIRUSTASK: A component focusing on propagating malware via removable media.
– FOOTWINE: A surveillance tool capable of keylogging and capturing audio and video.
– BLUELIGHT: A backdoor previously associated with ScarCruft, now repurposed in this campaign.
Initial Attack Vector: Malicious LNK Files
The attack sequence commences when an unsuspecting user opens a malicious Windows shortcut (LNK) file. This action triggers a PowerShell command that scans the directory to locate the LNK file based on its size. Subsequently, the PowerShell script extracts multiple embedded payloads from the LNK file, including:
– A decoy document.
– An executable payload.
– An additional PowerShell script.
– A batch file.
One such decoy document presents an article on the Palestine-Israel conflict, translated from a North Korean newspaper into Arabic, aiming to lure specific targets.
Progression of the Attack Chain
The extracted batch script initiates another PowerShell command responsible for decrypting and loading shellcode containing the RESTLEAF payload. Executed in memory, RESTLEAF establishes a connection with Zoho WorkDrive, marking ScarCruft’s first known exploitation of this cloud storage service for C2 communications.
Upon successful authentication using a valid access token, RESTLEAF downloads additional shellcode, leading to the deployment of SNAKEDROPPER. This component installs the Ruby runtime environment, sets up persistence via a scheduled task, and deploys both THUMBSBD and VIRUSTASK.
THUMBSBD: Bridging Air-Gapped Networks
THUMBSBD, masquerading as a Ruby file, plays a pivotal role in this campaign by utilizing removable media to relay commands and transfer data between internet-connected and air-gapped systems. Its capabilities include:
– Harvesting system information.
– Downloading secondary payloads from remote servers.
– Exfiltrating files.
– Executing arbitrary commands.
Upon detecting removable media, THUMBSBD creates a hidden folder to stage operator-issued commands or store execution outputs, effectively breaching the physical security measures of air-gapped environments.
FOOTWINE: Advanced Surveillance Capabilities
Delivered by THUMBSBD, FOOTWINE is an encrypted payload equipped with a shellcode launcher. It boasts advanced surveillance features, such as:
– Keylogging.
– Audio and video capturing.
FOOTWINE communicates with its C2 server using a custom binary protocol over TCP, supporting a comprehensive set of commands, including:
– Interactive command shell.
– File and directory manipulation.
– Plugin and configuration management.
– Windows Registry modification.
– Process enumeration.
– Screenshot capture and keystroke logging.
– Audio and video surveillance.
– Batch script execution.
– Proxy connection setup for bidirectional traffic relay.
– DLL loading.
BLUELIGHT: Leveraging Legitimate Cloud Services
THUMBSBD also facilitates the distribution of BLUELIGHT, a backdoor associated with ScarCruft since at least 2021. BLUELIGHT exploits legitimate cloud services, including Google Drive, Microsoft OneDrive, pCloud, and BackBlaze, for C2 communications. Its functionalities encompass:
– Executing arbitrary commands.
– File system enumeration.
– Downloading additional payloads.
– Uploading files.
– Self-removal.
VIRUSTASK: Propagating Malware via Removable Media
Similar to THUMBSBD, VIRUSTASK focuses exclusively on leveraging removable media to propagate malware to non-infected air-gapped systems. Unlike THUMBSBD, which handles command execution and data exfiltration, VIRUSTASK’s primary objective is to achieve initial access on air-gapped systems by weaponizing removable media.
Implications and Recommendations
The Ruby Jumper campaign underscores ScarCruft’s advanced capabilities in cyber espionage, particularly their innovative use of cloud services and removable media to infiltrate secure environments. Organizations, especially those operating air-gapped networks, should implement stringent security measures, including:
– Regularly updating and patching systems to mitigate vulnerabilities.
– Restricting the use of removable media and implementing strict access controls.
– Monitoring network traffic for unusual activities, especially communications with cloud storage services.
– Educating employees about the risks associated with phishing attacks and the importance of verifying the authenticity of received files.
By adopting a proactive and layered security approach, organizations can enhance their resilience against sophisticated cyber threats like those posed by ScarCruft.