U.S. Sanctions Russian Exploit Broker for Theft of Government Cyber Tools
On February 24, 2026, the U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) imposed sanctions on Russian national Sergey Sergeyevich Zelenyuk and his St. Petersburg-based company, Matrix LLC, publicly known as Operation Zero. This action marks the inaugural use of the Protecting American Intellectual Property Act (PAIPA) to penalize foreign entities profiting from the theft of U.S. intellectual property.
The Theft of U.S. Cyber Tools
Central to this case is Peter Williams, a 39-year-old Australian national and former executive at Trenchant, a cybersecurity unit under U.S. defense contractor L3Harris. Between 2022 and 2025, Williams exploited his access to steal at least eight zero-day exploits—hacking tools developed exclusively for the U.S. government and select allies. He sold these tools to Operation Zero for $1.3 million in cryptocurrency, causing approximately $35 million in losses to Trenchant. Williams pleaded guilty to two counts of theft of trade secrets on October 29, 2025, and was sentenced to 87 months in federal prison on February 24, 2026.
Operation Zero’s Exploit Brokerage
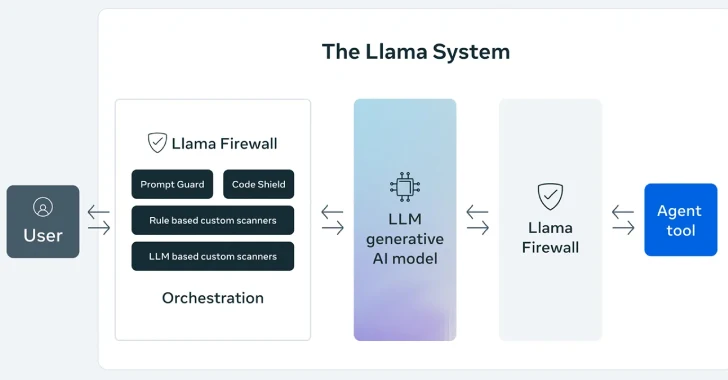
Since its inception in 2021, Operation Zero has functioned as an exploit broker, offering substantial bounties to cybersecurity researchers and hackers for zero-day exploits targeting widely used software, including U.S.-developed operating systems and encrypted messaging applications like Telegram. Notably, Operation Zero does not disclose discovered vulnerabilities to affected software vendors and restricts its clientele to non-NATO countries, including the Russian government. Beyond brokering exploits, Zelenyuk and his company have pursued the development of spyware and techniques for extracting sensitive personal data from AI large language model applications, actively recruiting hackers through social media to support their operations.
Sanctioned Individuals and Entities
The sanctions extend to several individuals and entities associated with Operation Zero:
– Sergey Zelenyuk: Founder of Operation Zero, designated for cyber-enabled activities threatening U.S. national security.
– Matrix LLC (Operation Zero): Russian exploit brokerage involved in acquiring and selling stolen U.S. cyber tools.
– Marina Evgenyevna Vasanovich: Zelenyuk’s assistant, acting on his behalf.
– Special Technology Services LLC FZ (STS): UAE-based affiliate controlled by Zelenyuk, sanctioned under PAIPA.
– Oleg Vyacheslavovich Kucherov: Suspected member of the TrickBot cybercrime gang, providing material support to Zelenyuk.
– Azizjon Makhmudovich Mamashoyev: Operator of Advance Security Solutions, offering material support to Zelenyuk.
– Advance Security Solutions: Exploit brokerage based in UAE/Uzbekistan, owned and controlled by Mamashoyev.
Notably, Oleg Kucherov is suspected to be a member of the TrickBot cybercrime gang, a modular malware suite identified in 2016, previously used in ransomware attacks against U.S. government agencies and healthcare centers. OFAC had designated TrickBot members in February and September 2023.
Implications of the Sanctions
As a result of these designations, all U.S.-held property and interests of the sanctioned entities are immediately blocked and must be reported to OFAC. Any entity owned 50% or more by a designated person is similarly blocked, and U.S. persons are prohibited from engaging in transactions with those on the Specially Designated Nationals (SDN) list.
This decisive action underscores the U.S. government’s commitment to protecting its intellectual property and national security by targeting foreign entities that illicitly acquire and distribute sensitive cyber tools.