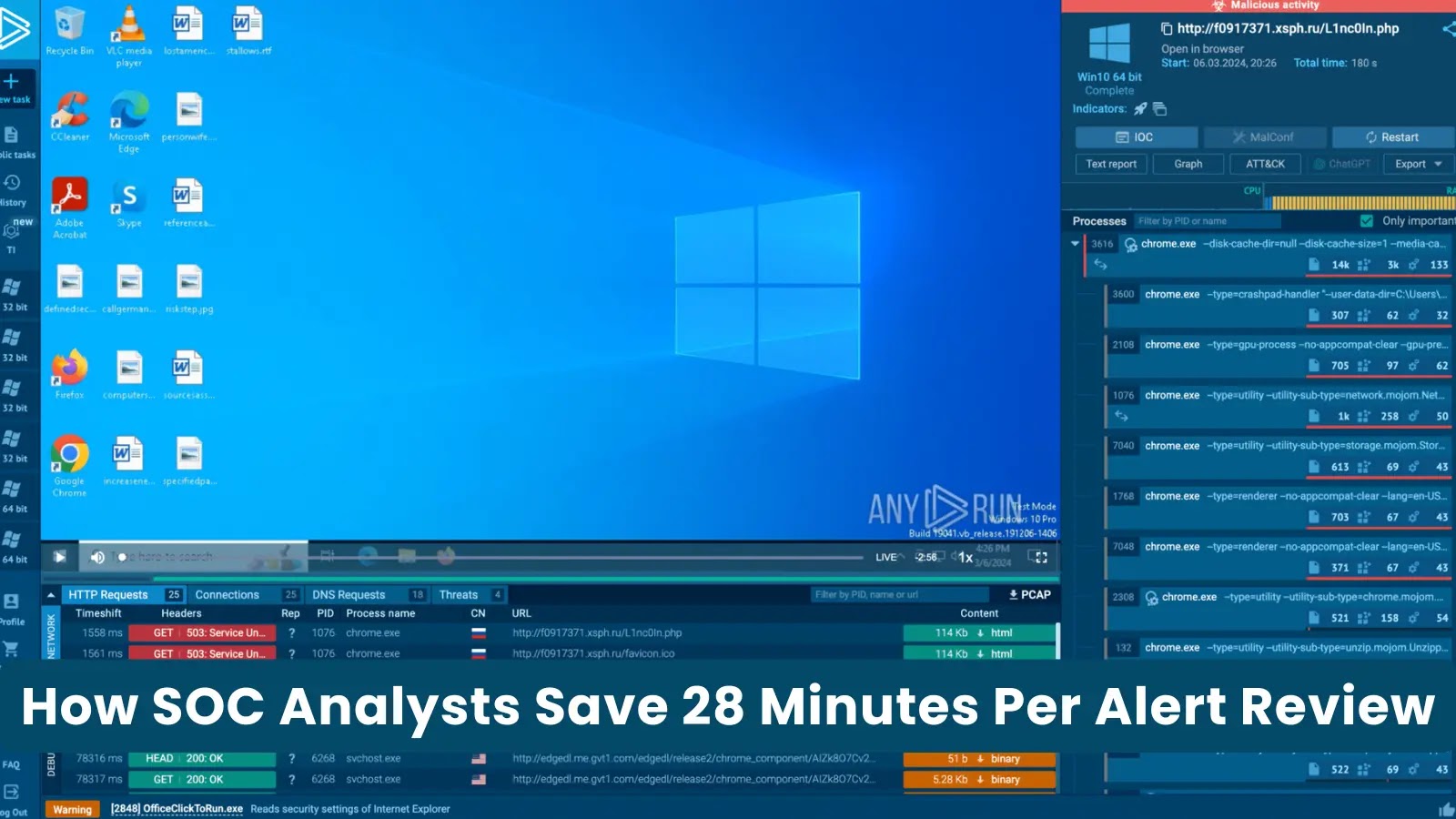
Revolutionizing SOC Efficiency: How Interactive Sandboxing Saves 28 Minutes Per Alert
Security Operations Centers (SOCs) are inundated with alerts daily, many of which are benign. Traditionally, investigating each alert consumes approximately 30 minutes, as analysts gather context from various tools—conducting reputation checks, enrichment processes, detonation requests, and log pivots. This labor-intensive approach leads to backlogs, increased operational costs, and delayed responses to genuine threats.
The Time Drain in Traditional Alert Reviews
Despite intentions for swift investigations, the process often extends to half an hour per alert. Analysts begin by verifying hashes and consulting threat intelligence sources, followed by detonation, log analysis, and meticulous review of alert details to ensure nothing is overlooked. Each step, while necessary, cumulatively prolongs the investigation. The complexity isn’t always due to the alert itself but stems from the need to piece together fragmented information to understand the file or link’s behavior.
A Two-Minute Solution: Interactive Execution for Alert Review
Imagine if the answer was visible before the search began. By executing the suspicious file or link within an interactive sandbox, such as ANY.RUN, analysts can observe real-time behavior. Processes initiate instantly, network connections materialize, and redirect chains unfold before their eyes. Analysts can interact with the page as a user would, eliminating uncertainty within seconds.
Benign alerts exhibit no suspicious behavior and can be confidently dismissed. Malicious alerts reveal their full chain immediately, providing clear evidence for escalation and response. Decisions are based on observable behavior rather than assumptions.
Case Study: Unveiling a Complex Phishing Attack
In a notable analysis, an alert was reviewed in just 35 seconds, uncovering a sophisticated phishing chain combining Salty2FA and Tycoon 2FA. What initially appeared as a simple suspicious link was, in reality, a multi-stage credential harvesting attack, swiftly identified through interactive execution.
The Transformative Impact of Sandbox-Based Alert Reviews
The efficiency stems from immediate visibility into behavior. In many environments, approximately 90% of alerts receive an initial verdict within the first 60 seconds of sandbox execution. Once the file or link is executed, uncertainty diminishes rapidly as activities become apparent from the outset.
The sandbox integrates automation with interactivity, mimicking real user behavior by triggering redirects, following infection chains, and exposing malicious content concealed behind QR codes or CAPTCHA gates. Analysts are spared from manually replicating each step to trace the chain’s progression.
Simultaneously, analysts can interact freely—clicking through pages, submitting data, downloading payloads, and observing the full response in real time. The process tree unfolds immediately, revealing which parent process initiated what and identifying any suspicious branches.
Network connections appear in real time, ensuring outbound traffic or command-and-control attempts are promptly detected. If the sample drops files, modifies the registry, or triggers browser activity, all actions are accessible within the same session, eliminating the need to switch between tools.
Indicators of compromise (IOCs) are automatically collected and organized in a dedicated tab, encompassing domains, IPs, hashes, URLs, and all extracted session data. Analysts no longer need to compile IOC lists manually; they are pre-structured for convenience.
Upon completing the investigation, a comprehensive report is auto-generated, including behavioral evidence, screenshots, network data, and extracted indicators. If escalation is necessary, sharing the session replaces the need to rewrite findings, saving additional minutes per case.
Measurable Improvements in SOC Performance
Reducing alert review time by 28 minutes per case significantly enhances SOC operations. It alleviates the time tax that slows queues, forces unnecessary escalations, and extends response timelines.
SOCs implementing ANY.RUN report:
– A 21-minute reduction in Mean Time to Respond (MTTR) per case through faster evidence collection and earlier containment.
– Up to a 20% decrease in Tier-1 workload by minimizing repetitive manual triage.
– A 30% reduction in Tier-1 to Tier-2 escalations due to clearer verdicts and stronger evidence.
– 94% of users report faster triage and quicker decisions on suspicious activity.
– Up to a threefold increase in SOC efficiency by reclaiming analyst time and improving throughput.
– Enhanced Service Level Agreement (SLA) performance with faster closure of benign alerts and quicker escalation of real threats.
– Reduced tooling overhead by avoiding hardware setup costs with cloud-based execution.
– Less alert fatigue with instant visibility into session activities.
Integrating ANY.RUN into workflows accelerates triage, reduces escalations, and shortens MTTR by providing execution-based evidence from the initial minutes of every investigation.