Silver Fox APT’s Advanced Malware Tactics: DLL Sideloading and BYOVD Exploits
The cybersecurity landscape has recently been disrupted by the emergence of sophisticated malware campaigns orchestrated by the Silver Fox Advanced Persistent Threat (APT) group. These operations predominantly target organizations across Asia, employing highly localized deceptive strategies to infiltrate corporate networks.
Deceptive Phishing Tactics
Silver Fox’s modus operandi involves dispatching meticulously crafted phishing emails that masquerade as official communications. These emails often contain malicious attachments or embedded links, luring recipients into interacting with them. Common disguises include tax audit notifications, software installation prompts, and electronic invoice downloads. Upon engagement, these elements initiate a stealthy infection chain, deploying the Winos 4.0 malware, also known as ValleyRat, into the victim’s system.
Severe Consequences of Infection
Once the malware establishes a foothold, it executes a series of malicious activities that can have devastating effects:
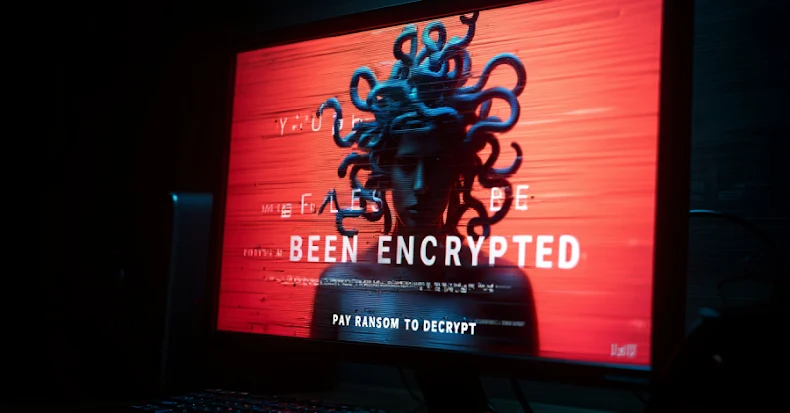
– File Encryption: Critical files are encrypted, rendering them inaccessible and disrupting business operations.
– Data Exfiltration: Sensitive information is extracted, potentially leading to data breaches and further cyberattacks.
The dynamic nature of Silver Fox’s infrastructure, characterized by a rapidly changing network of cloud domains, complicates traditional defense mechanisms. This volatility renders static domain blocking largely ineffective, necessitating more adaptive security strategies.
Sophisticated Evasion Techniques
To maintain prolonged access and evade detection, Silver Fox employs advanced techniques:
1. DLL Sideloading: The attackers deliver an archive containing a legitimate application alongside a malicious dynamic link library (DLL). When the application runs, it inadvertently loads the malicious DLL into memory, initiating the infection process.
2. Bring Your Own Vulnerable Driver (BYOVD): The malware introduces a signed, yet vulnerable, Windows kernel-mode driver named wsftprm.sys. This driver is exploited to escalate privileges silently, granting the malware elevated system access without triggering security alerts.
3. Security Process Termination: With kernel-level access secured, the malware continuously monitors and terminates active security processes. By targeting a wide array of antivirus and endpoint protection tools, it effectively blinds the system’s defenses, allowing unhindered operation and communication with command-and-control servers.
Defensive Measures
Given the sophistication of Silver Fox’s tactics, organizations must adopt a multi-layered defense approach:
– Email Vigilance: Treat all unexpected documents and external links with extreme caution. Educate employees on recognizing phishing attempts and the importance of verifying the authenticity of communications.
– Behavioral Monitoring: Implement tools that analyze system behavior to detect anomalies indicative of malware activity.
– Endpoint Protection: Regularly update endpoint protection signatures to recognize and neutralize emerging threats.
– Email Filtering: Deploy robust email filtering solutions to identify and block phishing emails before they reach end-users.
By integrating these strategies, organizations can enhance their resilience against the advanced and evolving threats posed by groups like Silver Fox.